If you've ever rooted an Android device in the past or installed a custom recovery, you're surely familiar with the term "unlocked bootloader." But if all of this sounds like gibberish to you, some major changes in Android have made it to where you should definitely get familiar with the concepts.
Enabling a single Android setting called "OEM unlocking" has the potential to prevent your device from falling victim to complete software failure, and it only takes a minute to turn this on. If you'd like to know why this option can cause your device to become bricked, I'll explain it all below.
Background Info: Kill Switch Law & Factory Reset Protection
In August of 2014, the state of California signed SB-962—the so-called "Smartphone Kill Switch" law—and this had some major repercussions on Android. From that point on, all new devices would need to have extra security measures implemented to be in compliance with this law, and more importantly, to be eligible for sale in America's most populous state.
To make sure they were in compliance, Google implemented a new Android feature called Factory Reset Protection, which ensures that even if a device is fully wiped, it cannot be used unless the original owner signs in with their account credentials. However, devices with unlockable bootloaders were still vulnerable considering that someone could unlock the bootloader, which would allow them to use fastboot commands to flash factory images and bypass Factory Reset Protection.
So to bolster FRP on devices with unlockable bootloaders like the Nexus series, Google added a hidden setting within Android that prevents bootloader unlocking and makes fastboot flashing impossible unless it's enabled. This setting is called "OEM unlocking," and it works because you need to sign in to Android with your pattern, PIN, or password to enable it before you can flash anything with fastboot.
Why Enabling 'OEM Unlocking' Can Save You from a Bricked Device
While the "OEM unlocking" setting being turned off by default does indeed have some security benefits, it comes with one major risk. If an over-the-air firmware update does not install properly for any reason, you'd be left with a completely bricked device.
The failed update would mean that you couldn't get into Android, which in turn would mean that you couldn't enable "OEM unlocking." With this setting still disabled, not even a smartphone repair shop could get your device back up and running.
On the other hand, if you have "OEM unlocking" enabled, a failed update is no big deal. You (or a repair technician) could simply unlock the device's bootloader and flash the factory images using fastboot, which would then overwrite the corrupt update and restore your firmware to working order.
Failed firmware updates are not exactly commonplace, but the risk is real. In fact, a corrupt update file recently left many Nexus 5 and Nexus 7 owners with devices that failed to boot—but luckily these devices were released before California SB-962 went into effect, so they weren't equipped with the extra Factory Reset Protection options.
How to Enable 'OEM Unlocking'
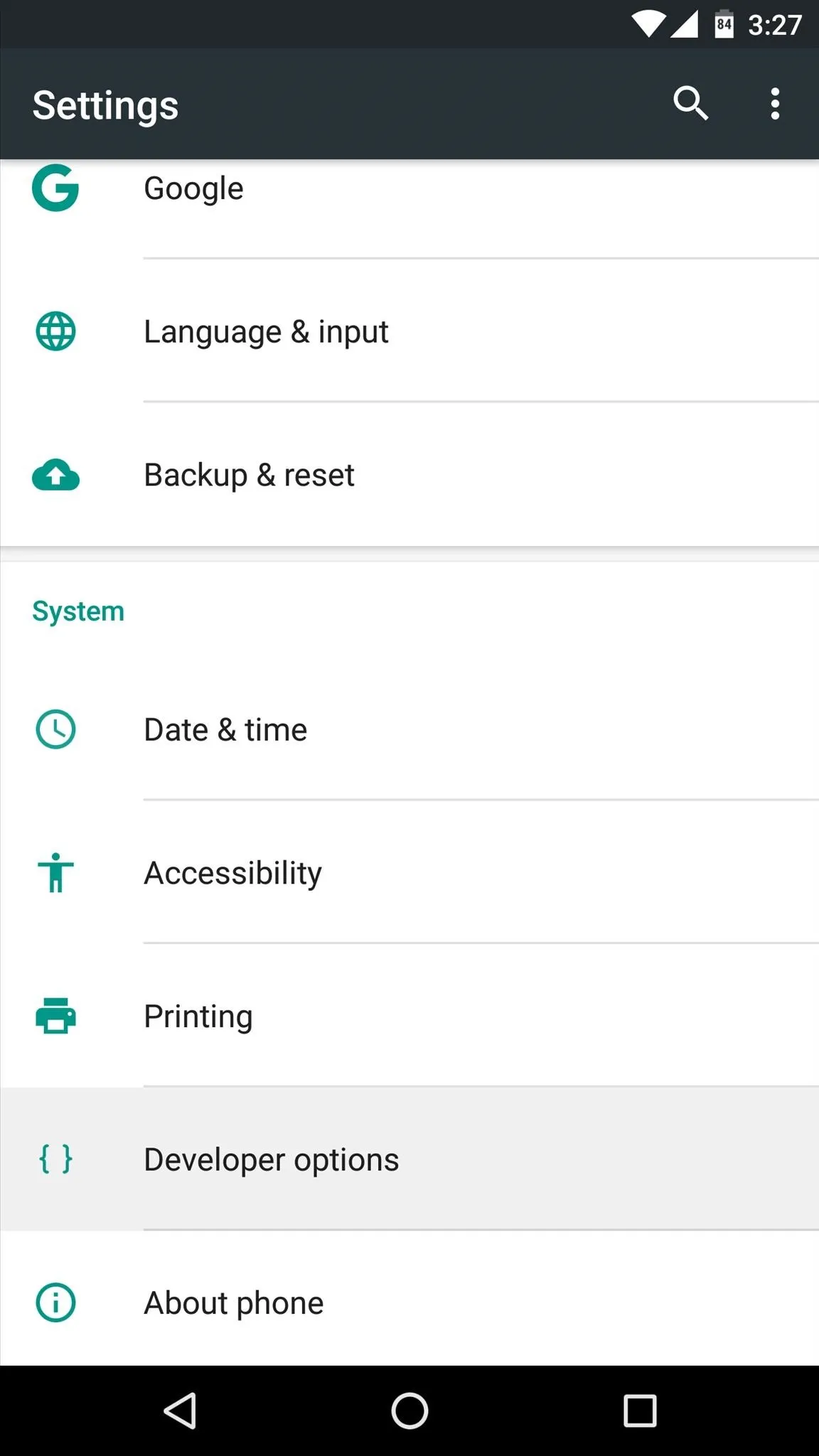
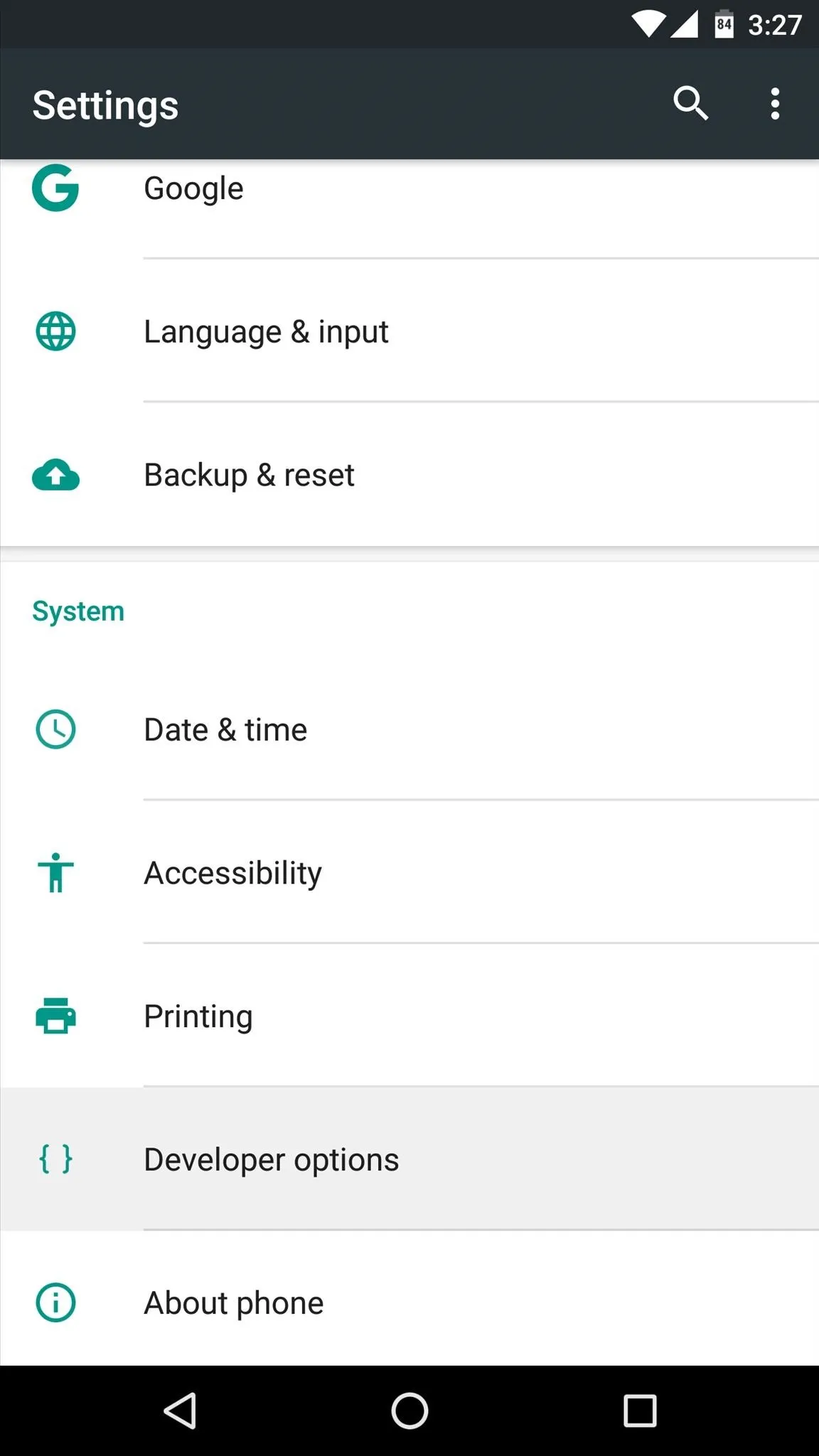
If you'd like to prevent the disastrous scenario described above, it's a relatively simple process. For starters, you'll need to enable the hidden "Developer options" menu by heading to About phone (or About tablet) in Settings, then tapping the "Build number" entry 7 times in rapid succession.
- Don't Miss: Our full guide on enabling Developer options
From there, simply head to the "Developer options" menu, then toggle the switch next to the "OEM unlocking" entry to enable it. Once you've done that, you can rest a lot easier knowing that a failed update no longer has the potential to render your device useless.
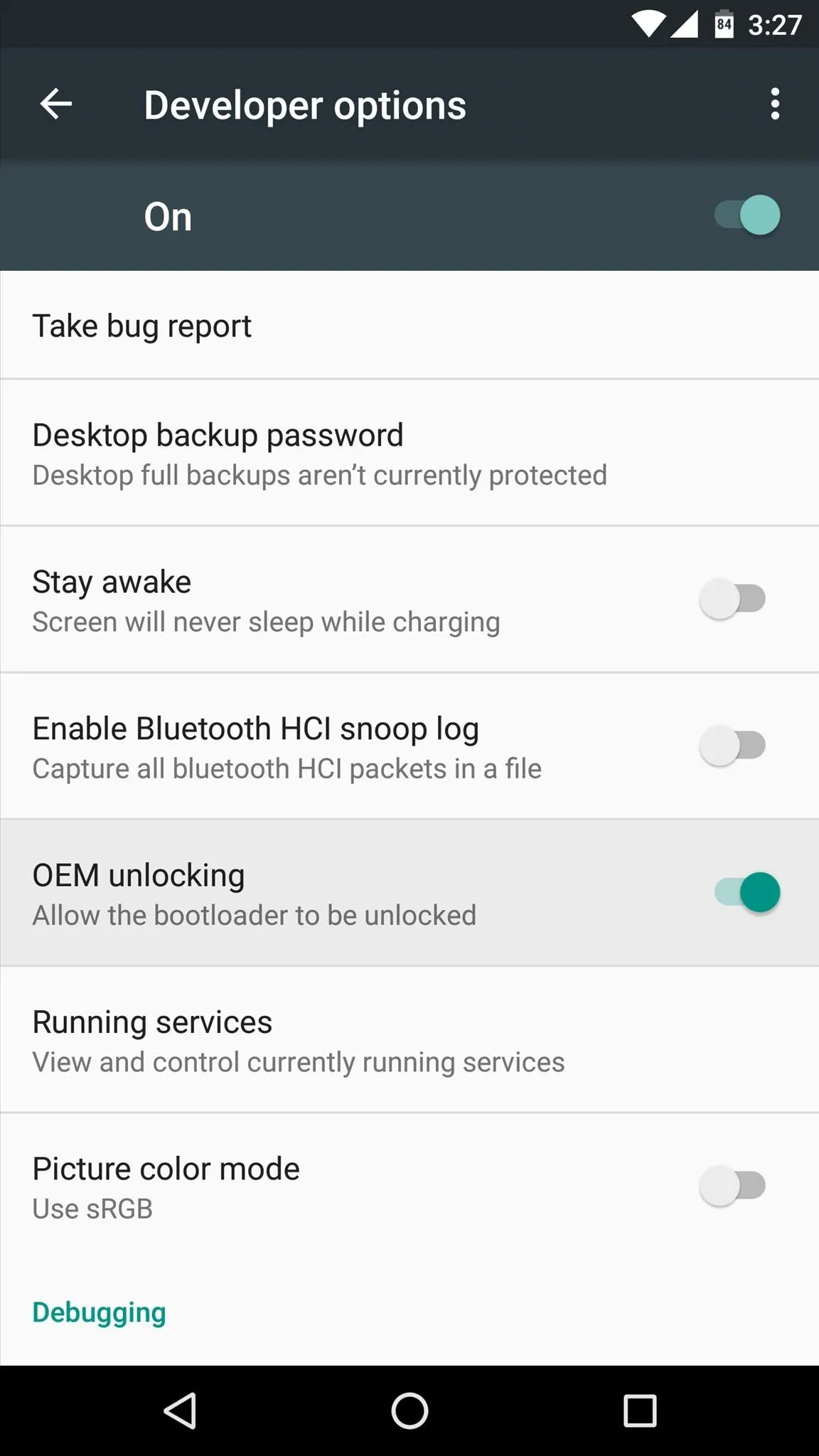
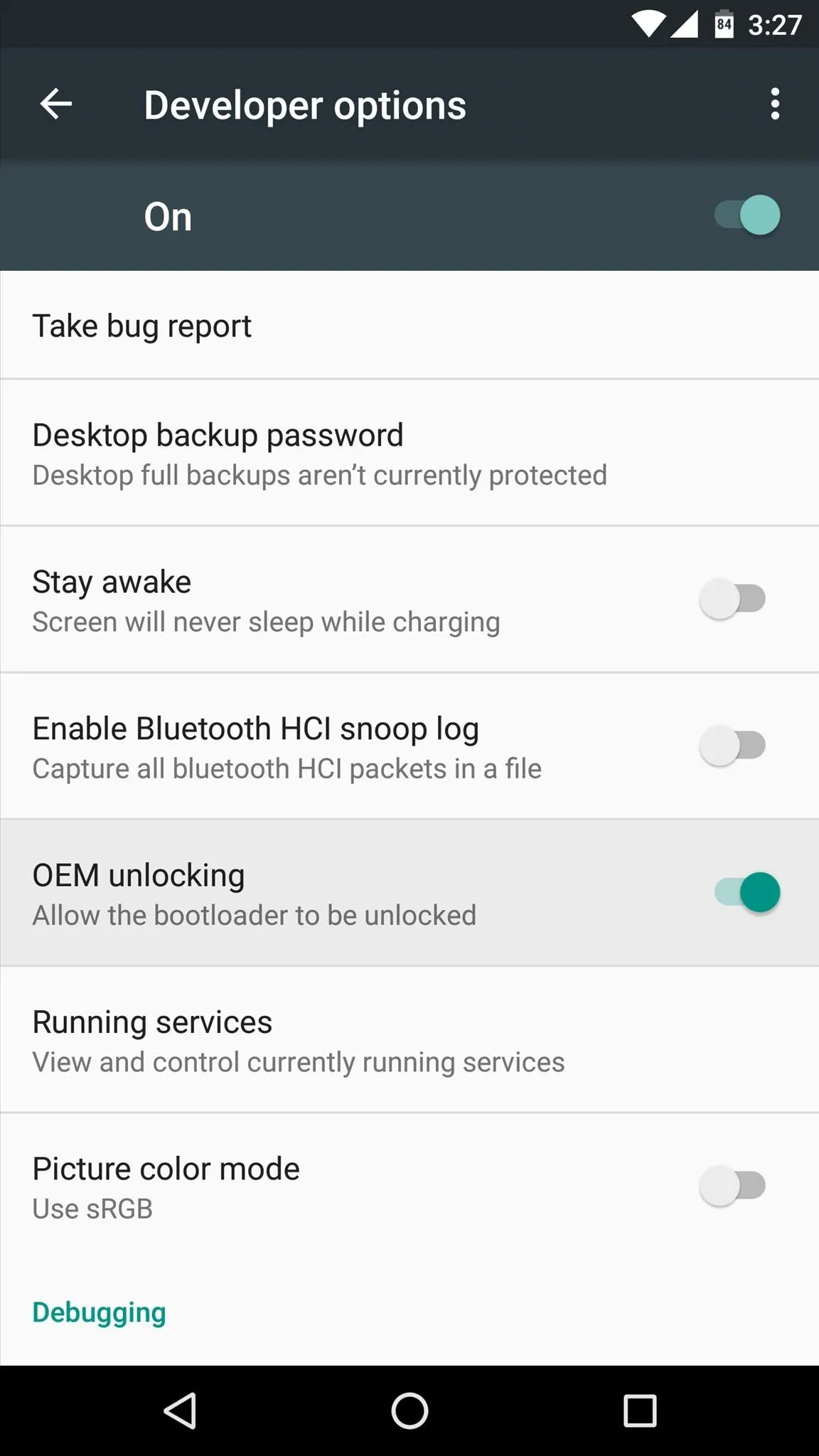
Keep in mind, though, that having the "OEM unlocking" option enabled is technically less secure. Theoretically, a tech-savvy thief could fully wipe your device with this option enabled, which means you would no longer be able to track the device's location using Android Device Manager. But the rest of Android's security measures would still be in place, so no one could access your data without your pattern, PIN, or password.
What are your thoughts on this situation? Is Factory Reset Protection more trouble than it's worth? Let us know in the comment section below, or drop us a line on Android Hacks' Facebook or Twitter, or on Gadget Hacks' Facebook, Google+, or Twitter.




















Comments
Be the first, drop a comment!