Android Security 101


how to
How to See All Your Wi-Fi Passwords on Android


how to
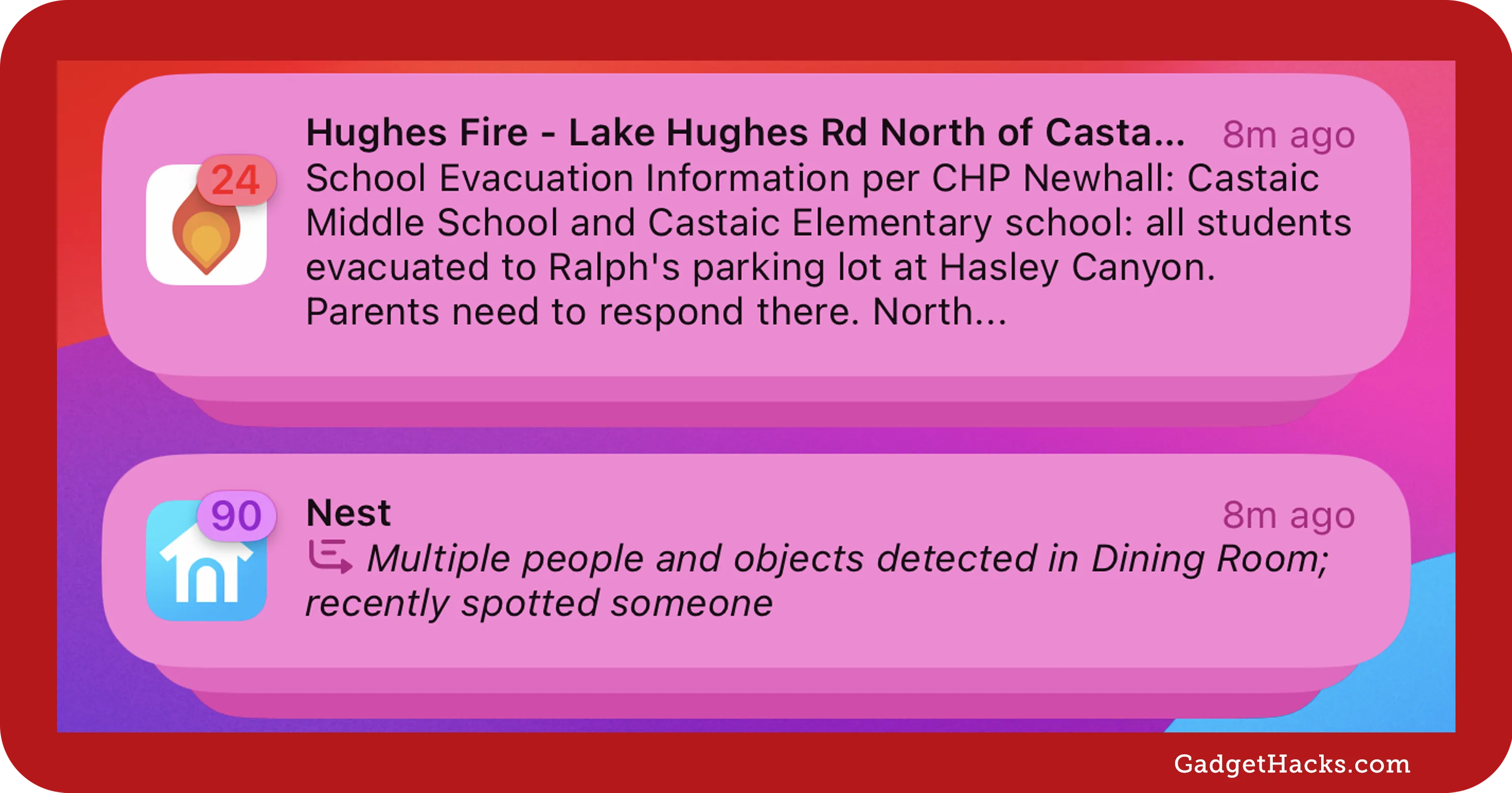
Attention Android Users — Activate This New Privacy Setting to Help Keep Thieves Out of Your Phone


how to
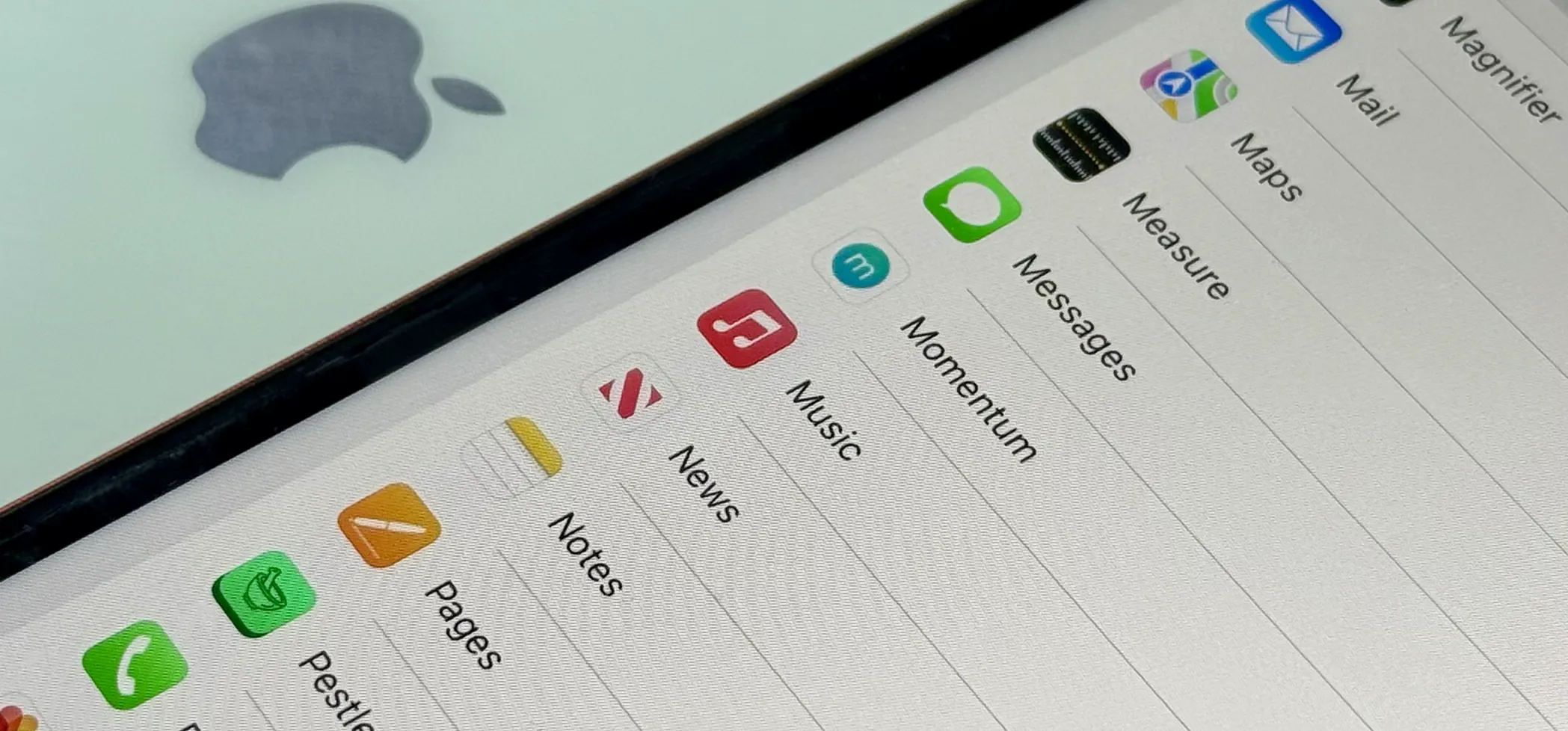
Your Android Phone May Be Spying on You — Here's How to Tell and Take Control