Because of the way Google Play works, Android has a "bad app" problem. Google allows any developer to upload an app to the Play Store, regardless of if it works, how it looks, or whether or not it can harm users. Malware scanning happens primarily after apps are uploaded, and though Google has recently taken steps to safeguard users with its Play Protect program, you don't have to depend on them.
Android has several tools accessible to users which provide protection. By combining secure technology with good decision making, you can protect yourself from most malicious apps. You can also apply these skills to protect yourself from broken apps or ugly ones. Unfortunately, these tips will not eliminate the possibility of downloading a malware app, but they'll significantly reduce the threat.
Tip 1: Don't Depend on Google Play Protect
After multiple issues with malicious apps making their way onto the Google Play Store, Google introduced Google Bouncer as a way to address the problem. This was an antivirus system which automatically scanned apps within the Play Store for malware and other forms of malicious code. Earlier this year, Google rebranded this feature along with "Find My Device" under the new title, Google Play Protect.
Performing the same tasks that each application did separately, Play Protect was Google's way of showing developers and consumers that they were serious about security. However, Play Protect doesn't eliminate the problem. According to AV-Test.org, as of November 2018, Google Play Protect only detected 66.9% of malware in real-time.
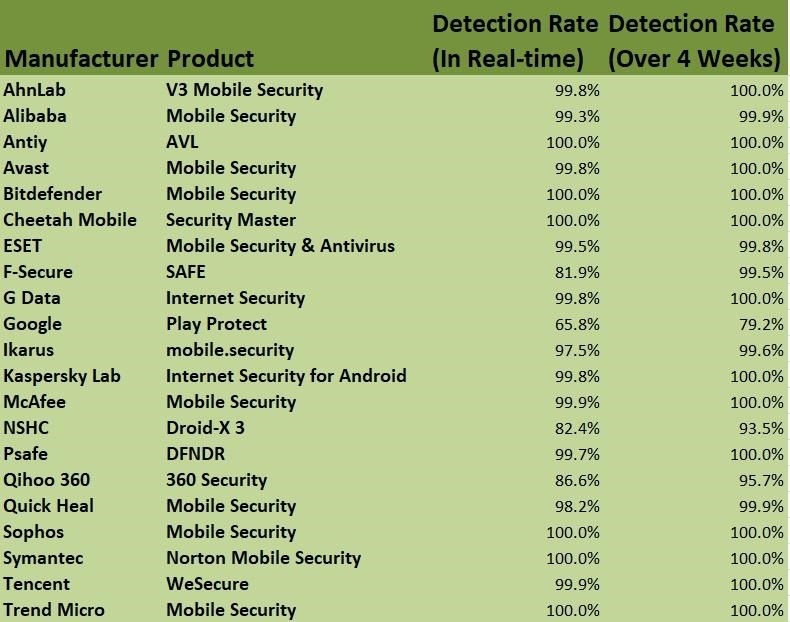
Compared to the industry average of 98%, Play Protect is an inefficient antivirus application. Play Protect also only detected 79.6% of the latest malware in the previous four weeks, which is well below the 98.6% industry average.
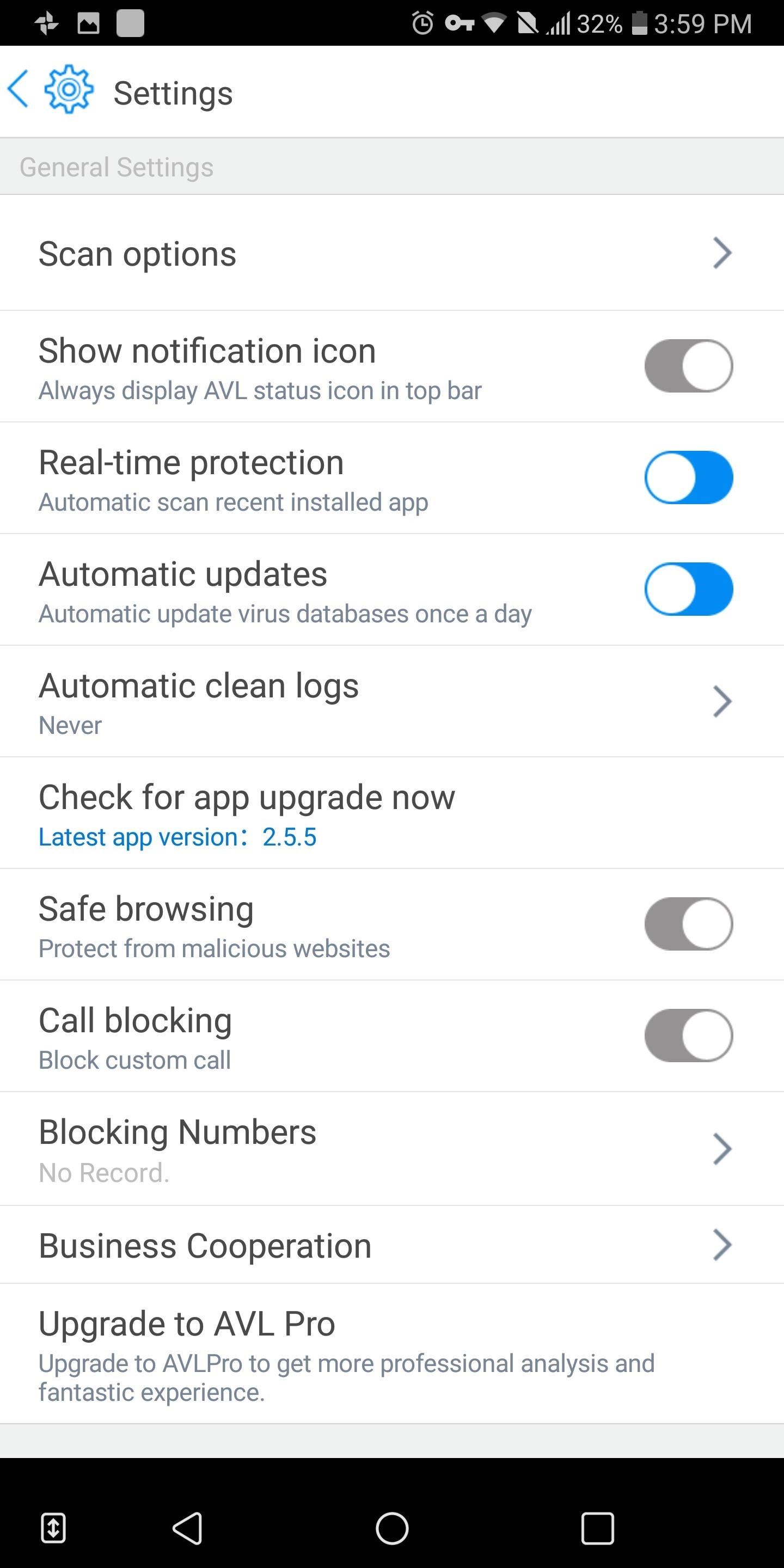
While we don't recommend disabling the feature (since it already built in and the "Find My Device" features are useful), we do recommend downloading another antivirus app to supplement malware scanning. Specifically, one with a much higher detection rate and a minimal effect on battery life: Antiy AVL.
Antiy AVL is above the industry average on both real-time detection and detection over four weeks with a 100% detection rate in both categories. According to AV-Test.org, it has minimal impact on the battery and performance of your smartphone and had zero false positives for app found on the Play Storeor third-party app stores. Similar to the Play Protect, it offers real-time protection before you install an application from any source.
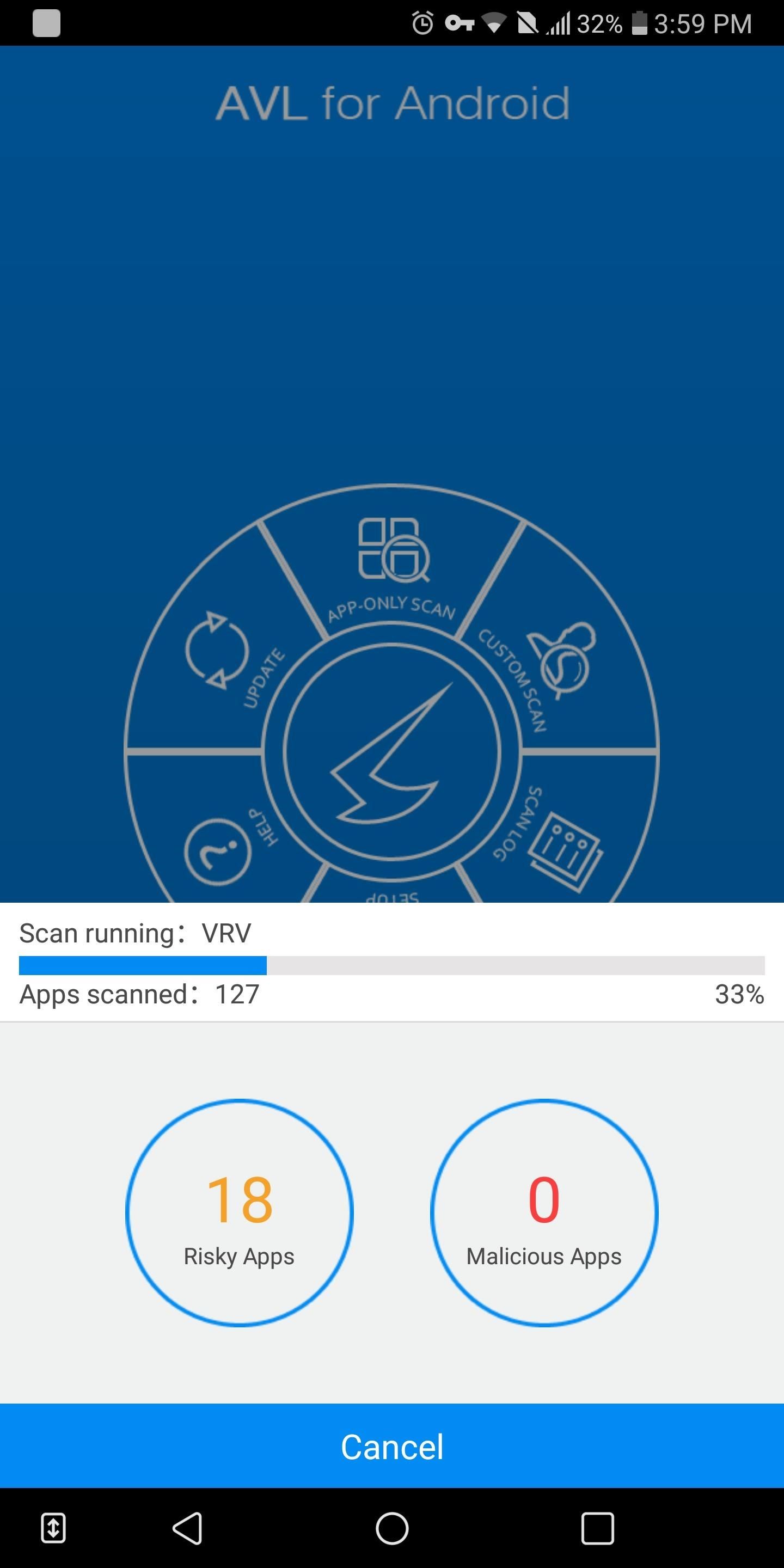
Once you install the application, we recommend performing an "app only" scan to make sure nothing malicious is already installed on your device. After you've scanned your smartphone, let AVL perform background scans (which is enabled by default) to automatically protect your device.
Tip 2: Review App Permissions
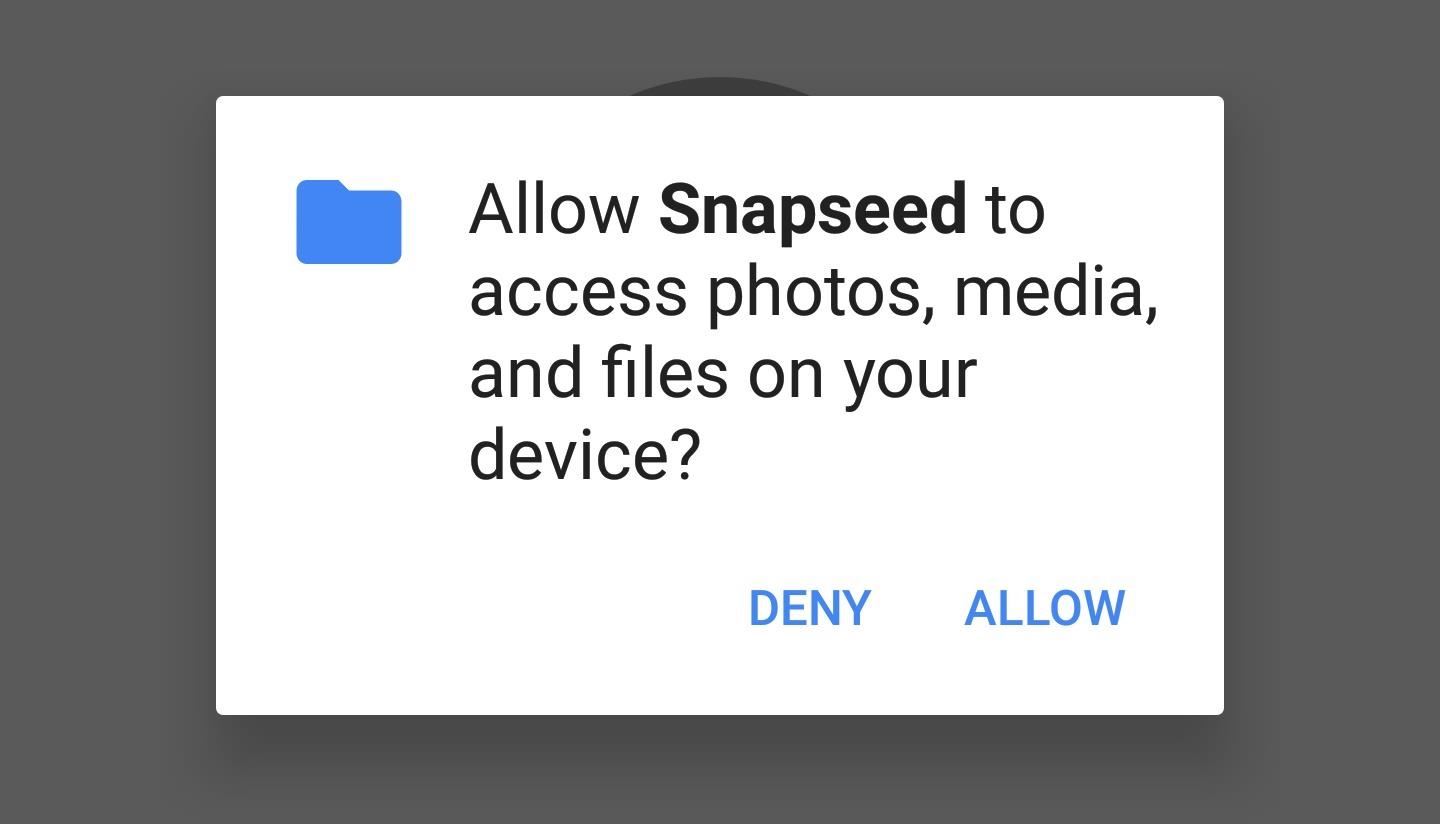
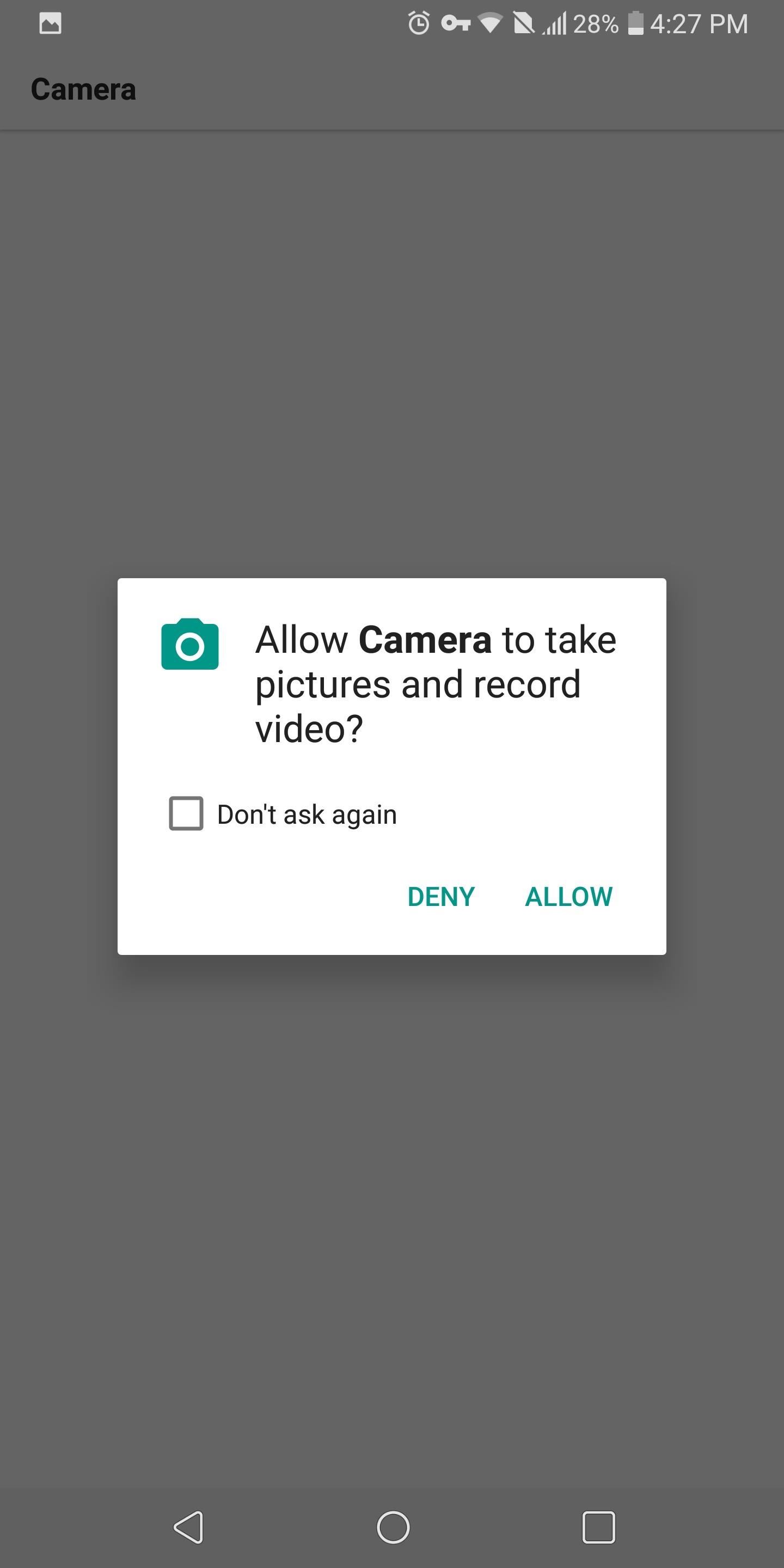
Starting with 6.0 Marshmallow, Android uses an app permissions system to dole out access to certain functions of your smartphone. For instance, a camera app would obviously need access to your phone's camera, and a navigation app would require usage of your GPS or location data.
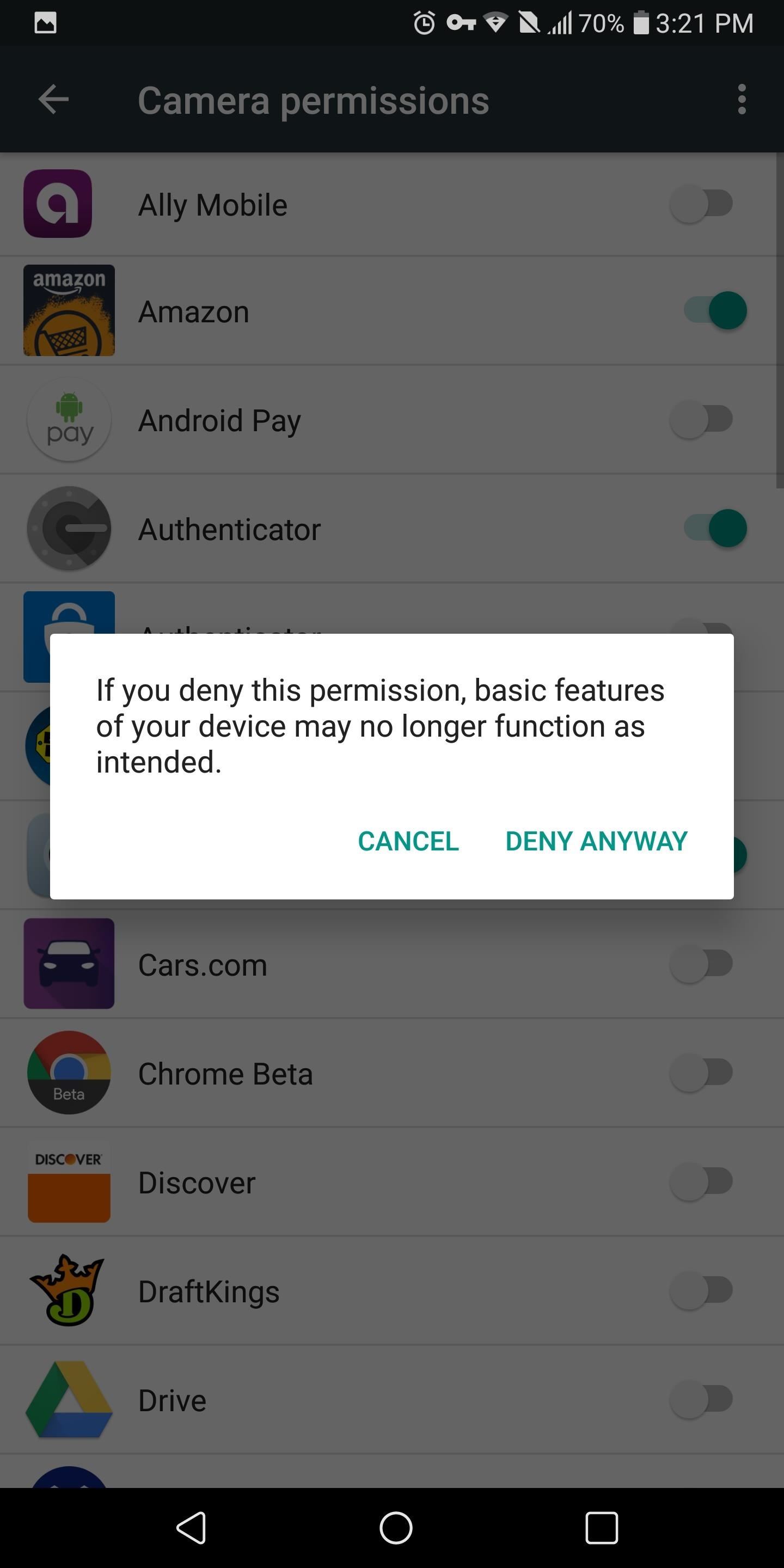
However, the apps aren't granted these permissions by default, so you'll usually see a series of permission requests the first time you open an app or the first time you attempt to use a feature that requires one of these permissions. Once you tap "Allow" on a permission request, the app can now access that function of your smartphone anytime it wants.
Unfortunately, not every app uses this new system (despite the fact that new apps and updates to existing apps have to), and instead, will request permissions in bulk when you're installing the app. This is an all-or-nothing deal, so if you didn't want the app to access certain functions of your phone, you simply can't install it.
It's also very easy to misinterpret the initial batch permission request as a confirmation popup asking if you're sure you'd like to install the app — if you tap "Allow," the app now has permission to access every function it requested.
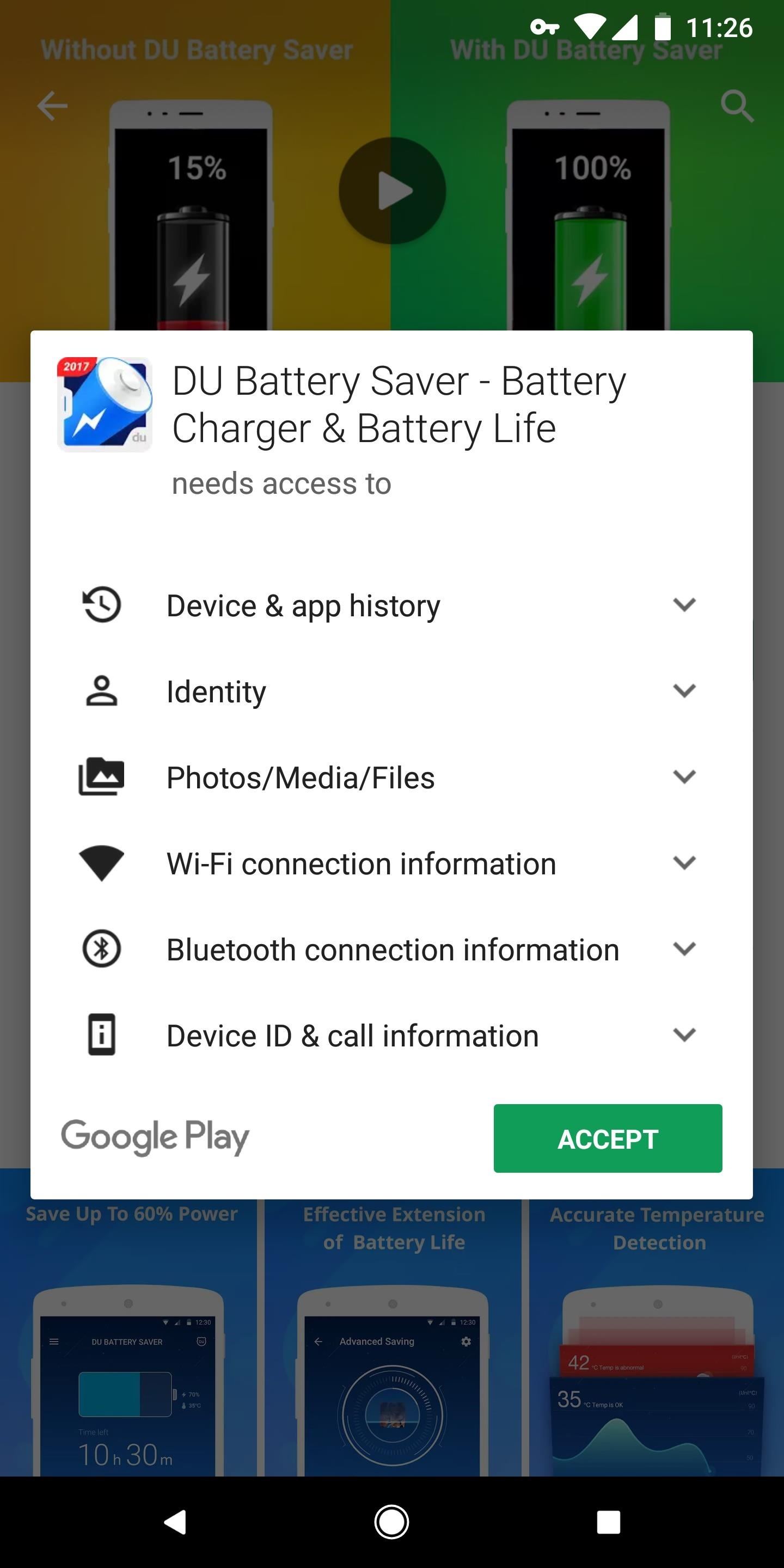
Even if they use the new system, many apps request permissions that they do not need for functionality. Reviewing all apps permissions provides both privacy and security. Fortunately, Android makes reviewing application easy by grouping permissions together instead of making you review apps individually.
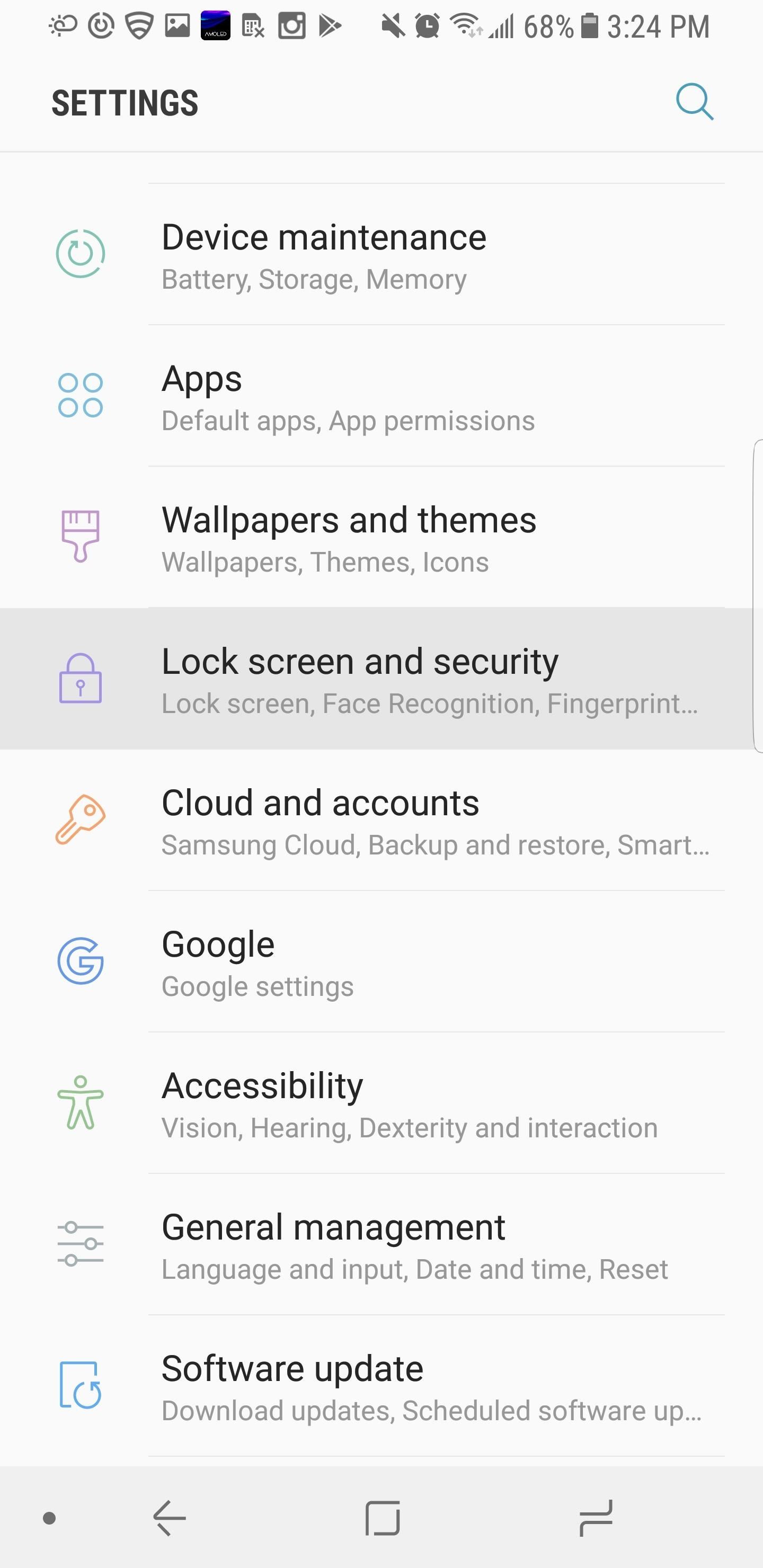
To review app permissions, open the Settings menu by either selecting the gear icon in Quick Settings or selecting the "Settings" icon in the app drawer. Located at the top of this menu will be a search bar or a magnifying glass icon, select either one and type in "Configure Apps" or "App Permissions."
If nothing shows up (as is the case with LG UX devices), choose "Apps" in the Settings menu and select the three vertical dots. When the sub-menu opens, choose "Configure Apps," then "App Permissions" (depending on the skin, it might just say "Permissions").

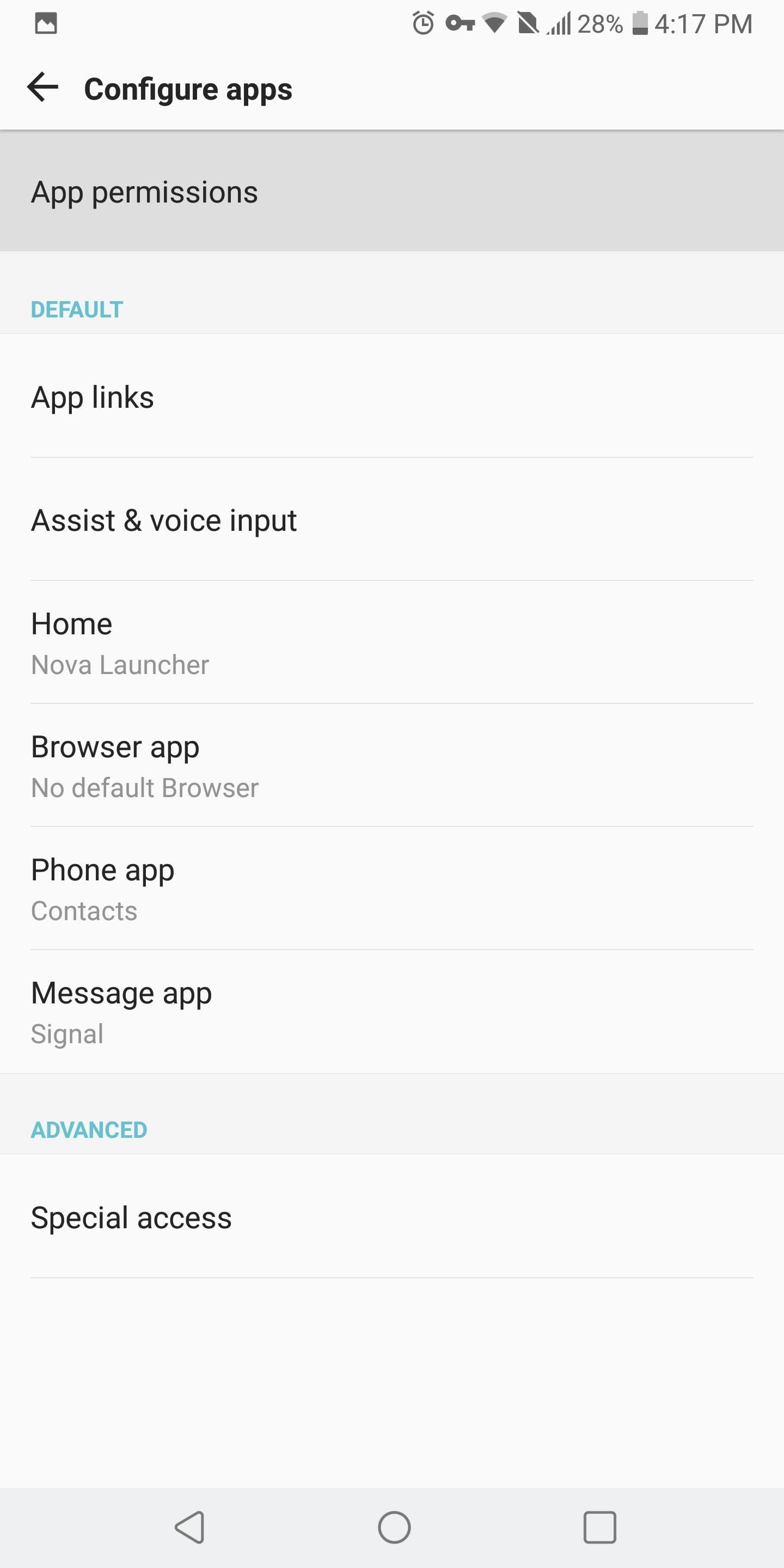
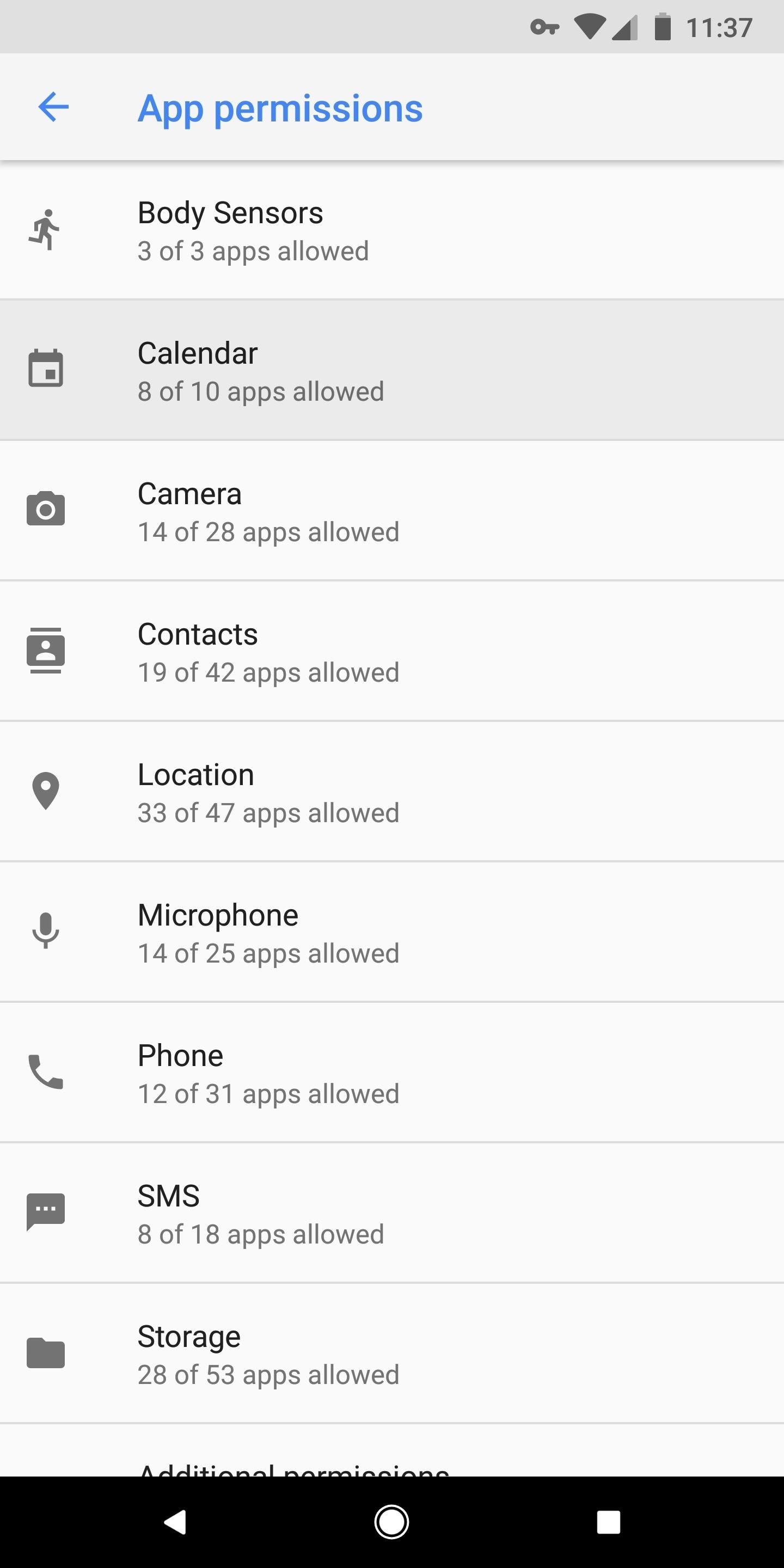
Next, you'll see a list of all permissions allowable to apps and the number of applications that currently have access to that function of your smartphone. Starting from the top, select each one and decide if the application needs to have permission.
The recommended strategy to follow is the principle of least privilege. This principle states that individuals (in this case, apps) should only have access to the absolute minimum permissions needed to perform their task, and nothing more.
An example of this can be found in the official app for Foot Locker. This application can obtain permission to your calendar to add events. If you don't wish to use this feature, deactivate this permission to prevent the collecting of personal data.
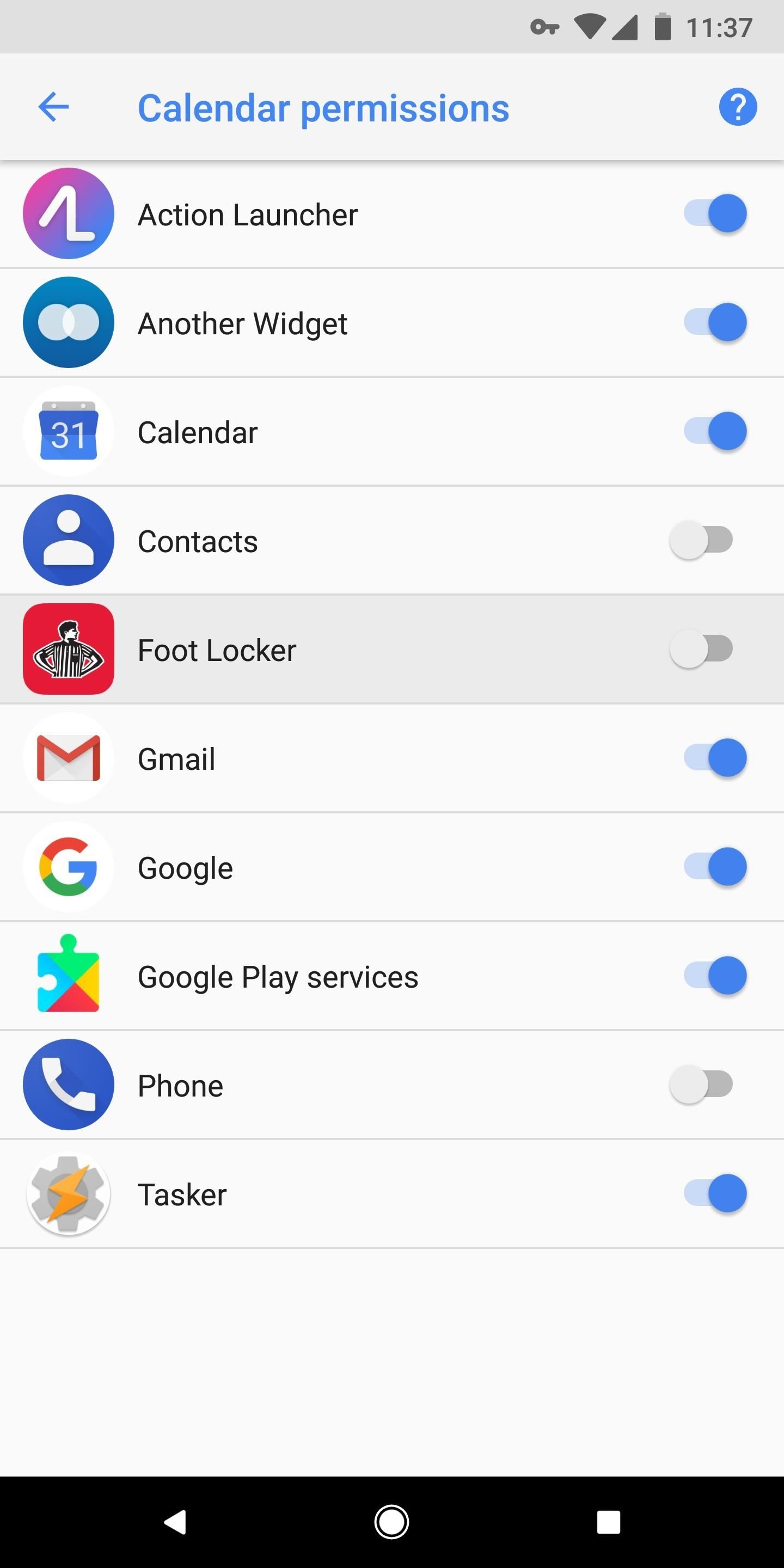
By minimizing app access, you'll protect yourself from companies obtaining an unnecessary amount of information about you. This practice also protects you from malicious agents (such as hackers) who might compromise the app to attack your device. A hacker could perform a more sophisticated attack of allowing the app to operate as usual, but using the app's extensive list of permissions to gather information about you.
Unless it's an older app that doesn't use the new permissions system, you don't have to worry about breaking an app when removing permissions. After you deactivate a permission, open the application. The app will ask for the permission back if it deems it necessary for regular operations.
Tip 3: Turn Off Unknown Sources
Despite the Play Store's issue with compromised applications, the Play Store is the most secure place to download Android apps. However, Android does provide the option to sideload apps from alternative sources. While we here at Gadget Hacks don't condemn the use of third-party apps, we do recommend using Play Store apps whenever possible.
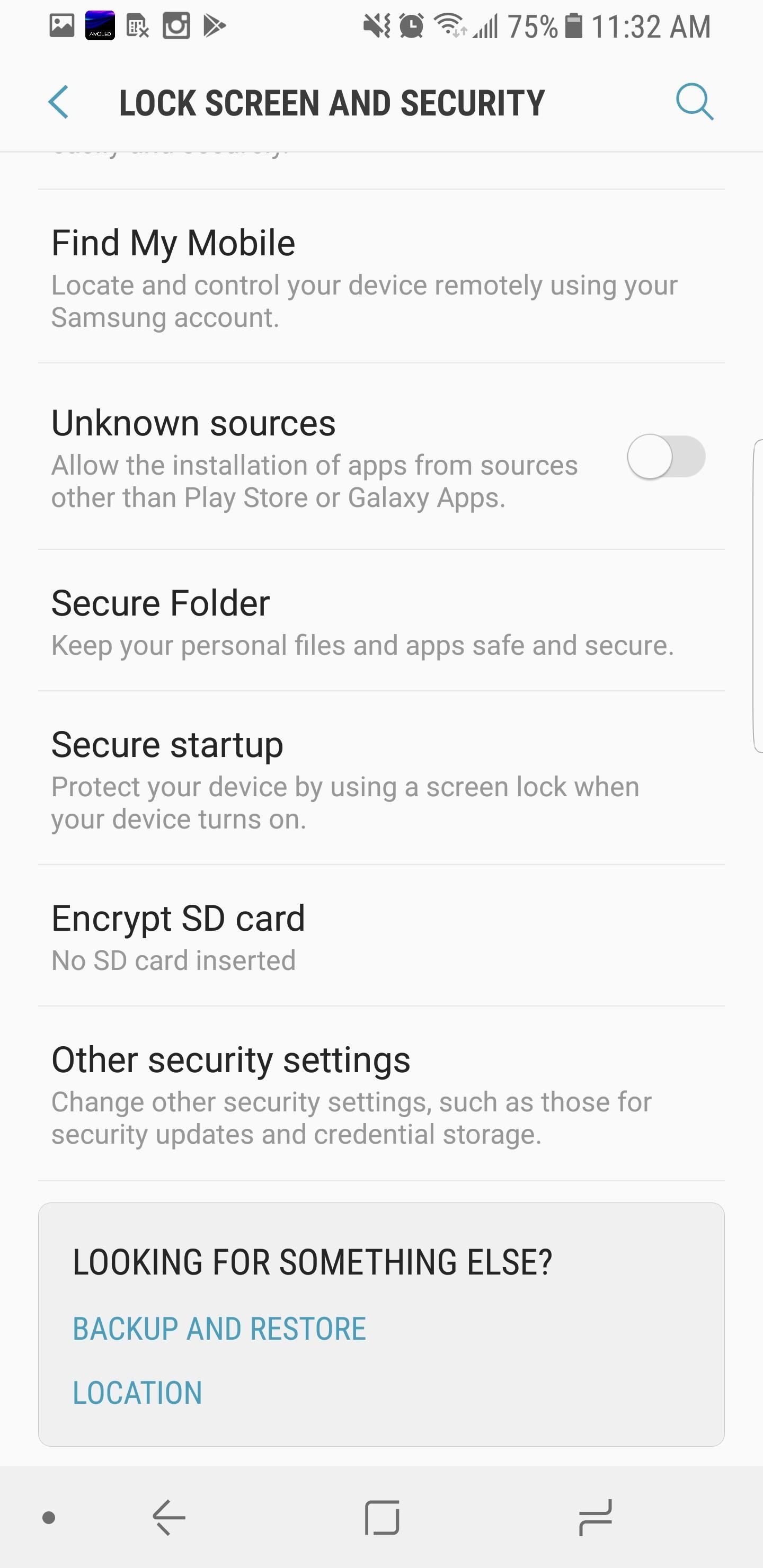
Android controls the ability to install third-party apps with an option known as "Unknown Sources" — you'll only be able to install non-Play Store apps when this option is enabled. "Unknown Sources" is disabled by default, but, if you're a long time reader, you've probably enabled the option for additional functionality such as adding the Pixel's Dialer or getting Google Now on a third-party launcher. Since you already installed the application, disabling "Unknown sources" won't deactivate the third-party apps. Instead, it will prevent unauthorized installation of non-Play Store apps by outside threats scheming to attack your device.
To disable "Unknown Sources," navigate to the Settings menu and select "Security." This menu may be bundled with other options such as "Lock Screen & Security" or "Privacy & Security," but if you don't see anything similar to the previously mentioned options, search for "Security" within the main Settings menu. Once there, scroll down until you see the "Unknown Sources" option and disable it.
If you're on a newer Android version (8.0+), Unknown Sources has been replaced with a per-app permission called "Install Other Apps." You can revoke this permission for any app that you don't think should have the ability to install apps. To do so, head to Settings –> Apps & notifications –> Advanced –> Special App Access, then select "Install Other Apps."
Tip 4: Take Care of the Little Things
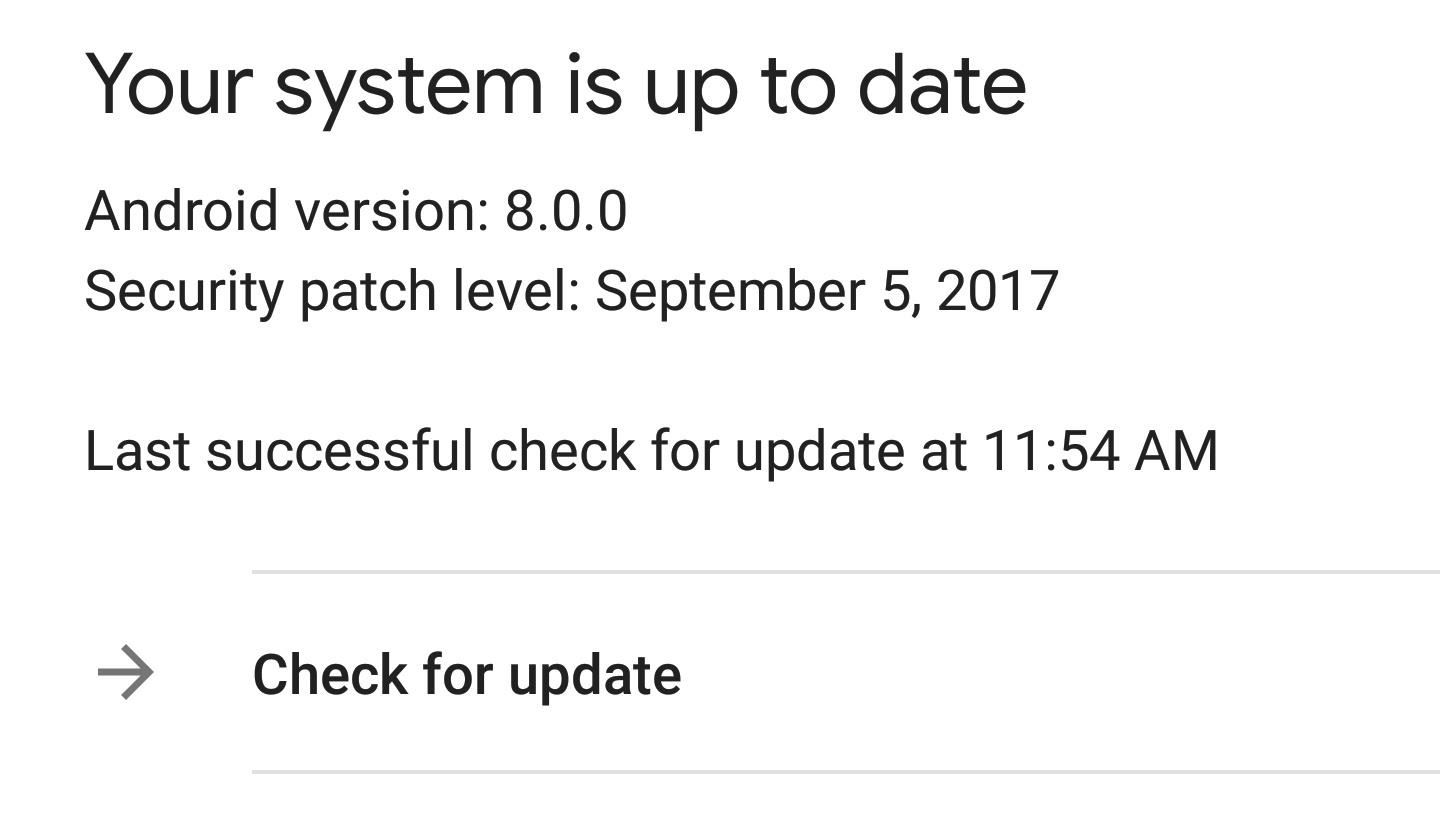
There are several little things that you can do improve your chances of not being infected with malware or accidentally installing a malicious application. The first thing is to keep your phone's firmware updated by accepting any available upgrades in Settings –> System –> System Updates.
Unfortunately, this step isn't always in our control since hardly any OEM provides monthly Android security patches promptly. Except for the Pixel lineup and a few others, most Android smartphones are at least two months behind. However, when your device does get an update, accept it immediately.
Usually, firmware updates will not only include the latest security patches, but also bug fixes. Recently, the KRACK vulnerability of Wi-Fi's WPA2 protocol has compromised millions of Android devices, but Google added a fix in the most recent security patch. However, if you didn't update your device, it remains susceptible to hacking when using Wi-Fi. For those who didn't get the patch, follow the link below for ways to protect yourself while browsing the web using Wi-Fi a you wait for the update.
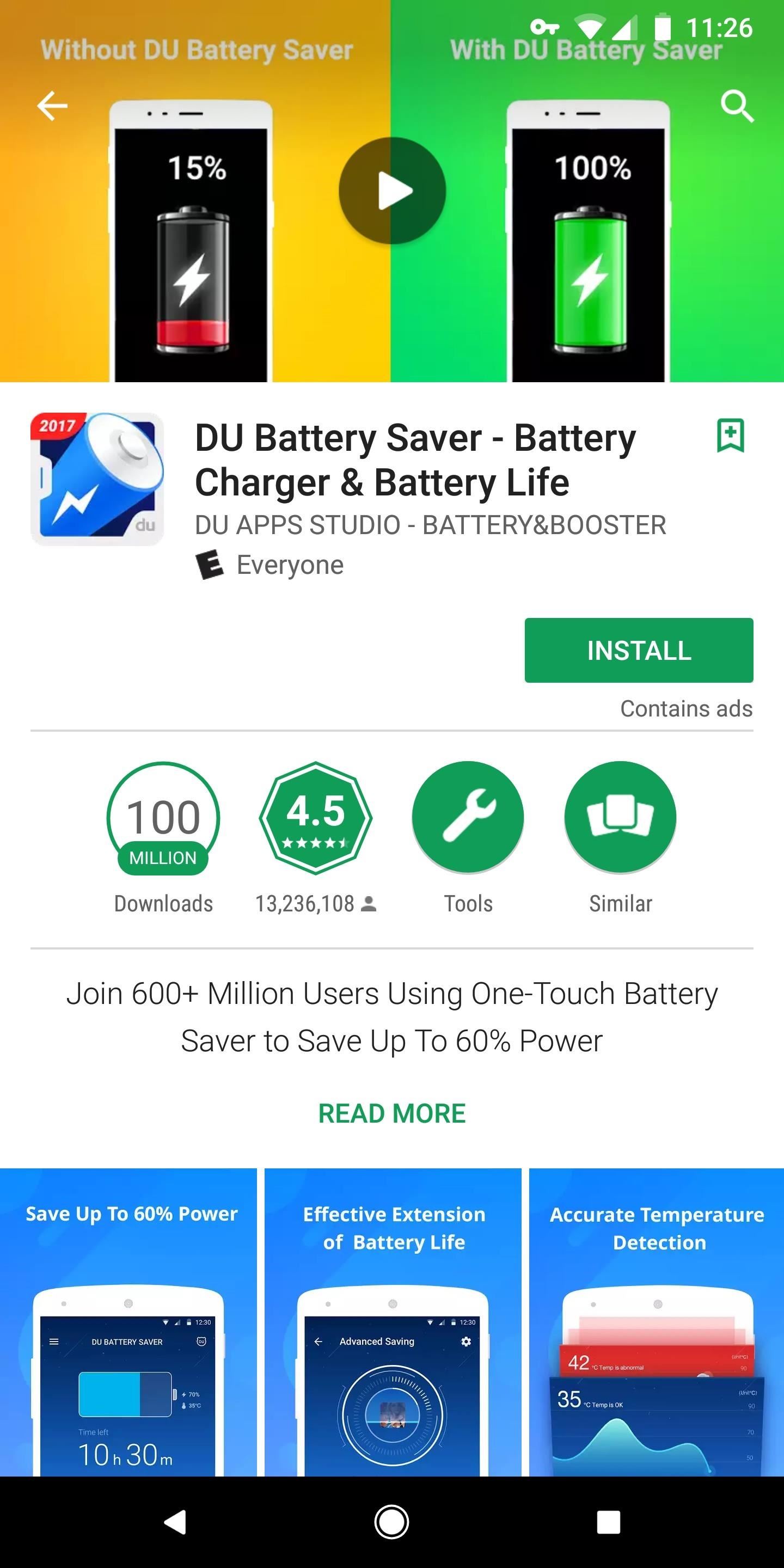
Now that you know malware infested apps are on the Play Store, do a little research before you install an app. Read the reviews by Android users for any reported issues. Most of the time, if the app isn't doing what it advertised to do, the reviews will reflect that. Also, look at the author of the app. If the application has extensive controls or links you to a company's resources, the author should be a company and not an individual. For example, if you see an app called Amazon with an author name "Hacker Joe," don't install it.
Avoid obscure apps that provide too much functionality. As the saying goes, "if something is too good to be true, it probably is." Also, understand that if the app as good as advertised, many outlets (including here at Gadget Hacks) would test it and cover it so that readers would know.
We've covered these and other habits you can implement to make sure you don't install malware from the Play Store. To read all about those, hit up the following link.
Finally, use a VPN when possible. A VPN will ensure that communications between you and the app's server are secure, and some VPNs (such as NordVPN) will review the traffic for malware and block it from reaching your device. When it comes to Android security and privacy, VPN is always a recommendation.
By using these tips, you can reduce your chances of downloading a malicious app. Unfortunately, these steps won't eliminate the risk, so always be vigilant with your device, monitoring it for any changes. Let us know in the comments below if you have been affected by malware on your Android device.
This article was produced during Gadget Hacks' special coverage on smartphone privacy and security. Check out the whole Privacy and Security series.
Who needs a wand? Unlock your magical powers and transform yourself from a Muggle into a Wizard or Witch just by using your Android phone. See how:






















Be the First to Comment
Share Your Thoughts