Samsung, like other OEMs, partners with third-party companies to include their apps on Galaxy devices. For example, Microsoft pays Samsung millions to pre-install certain Office apps. But one of these partners might not be on the up and up.
- Already know about Qihoo 360? Skip ahead to the instructions.
The Problem with Device Care
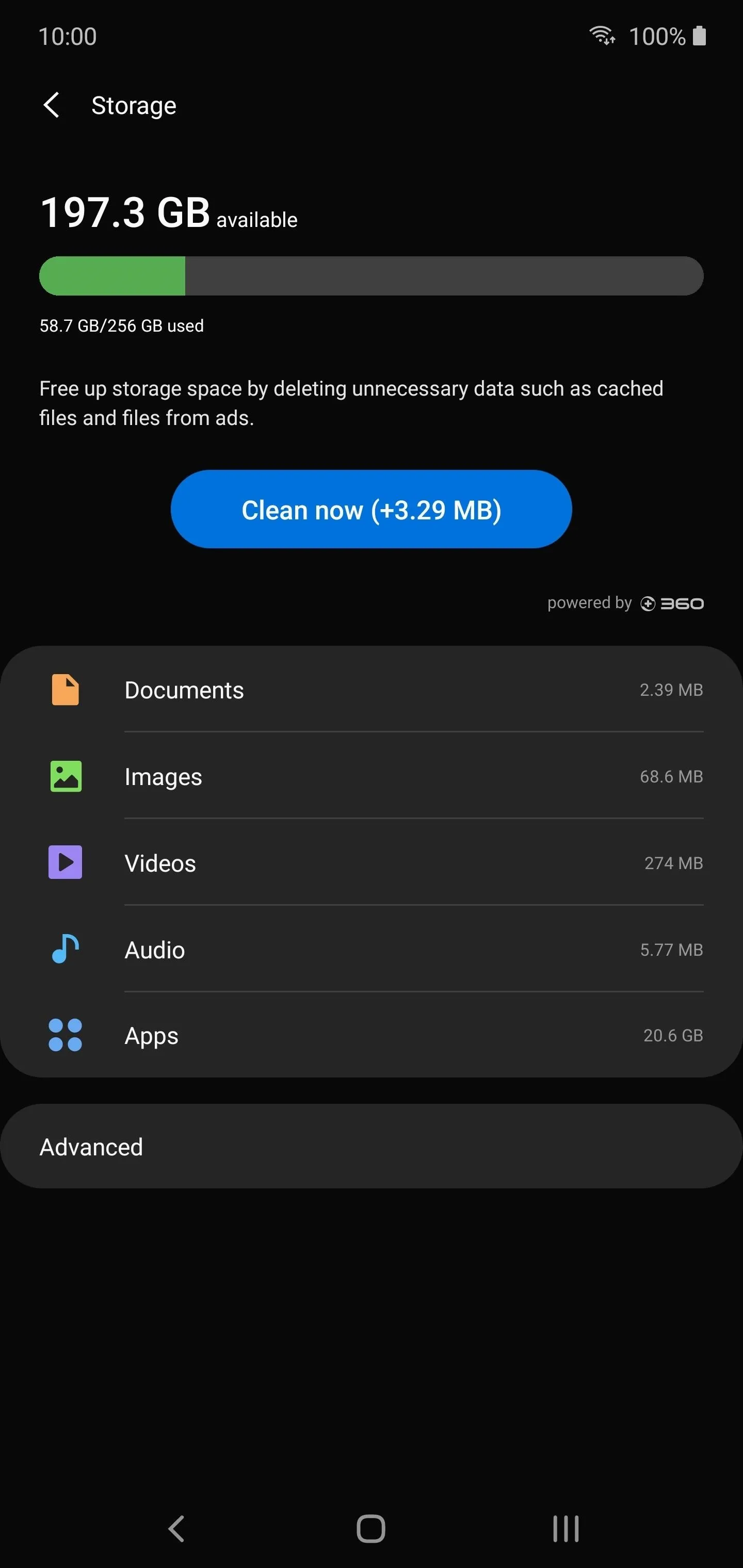
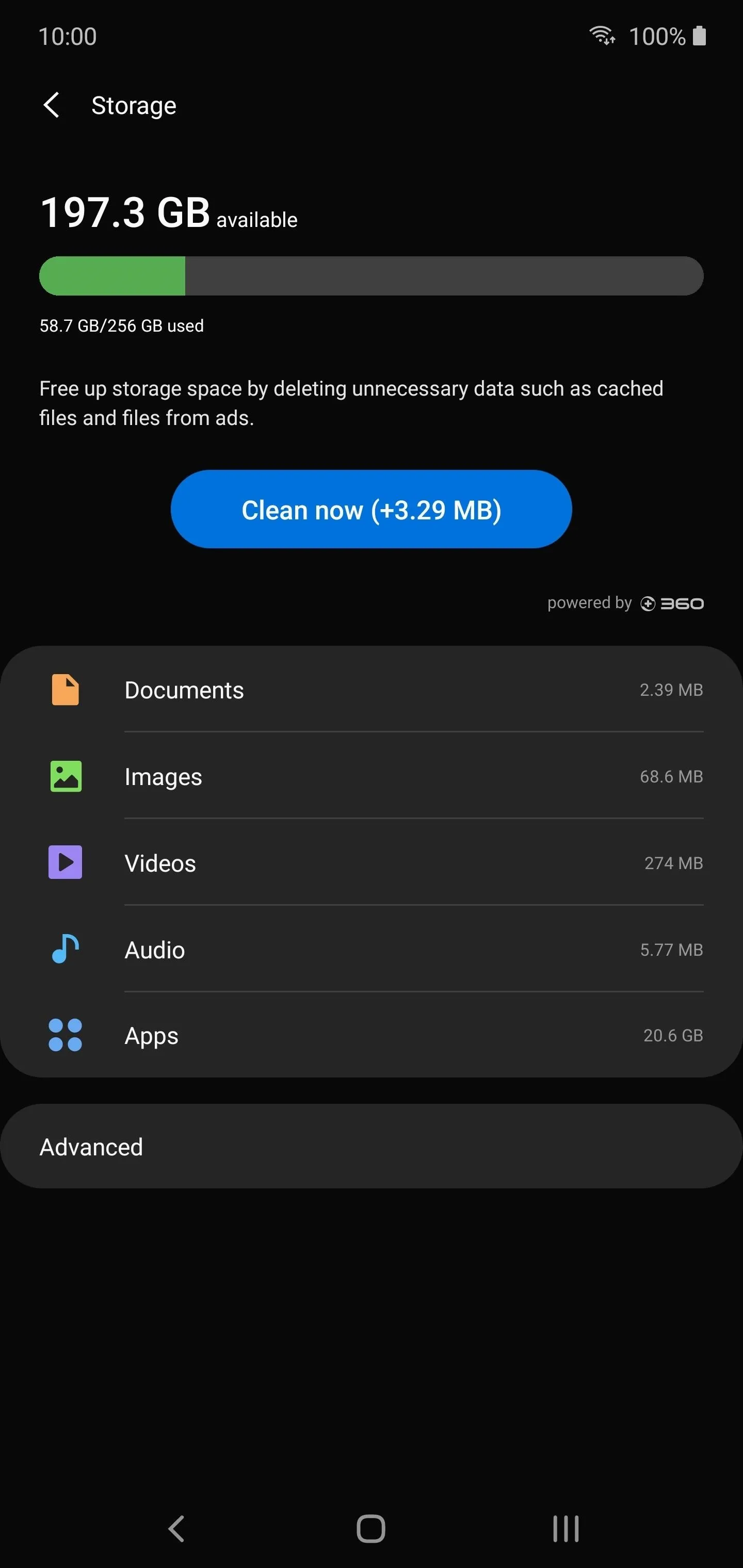
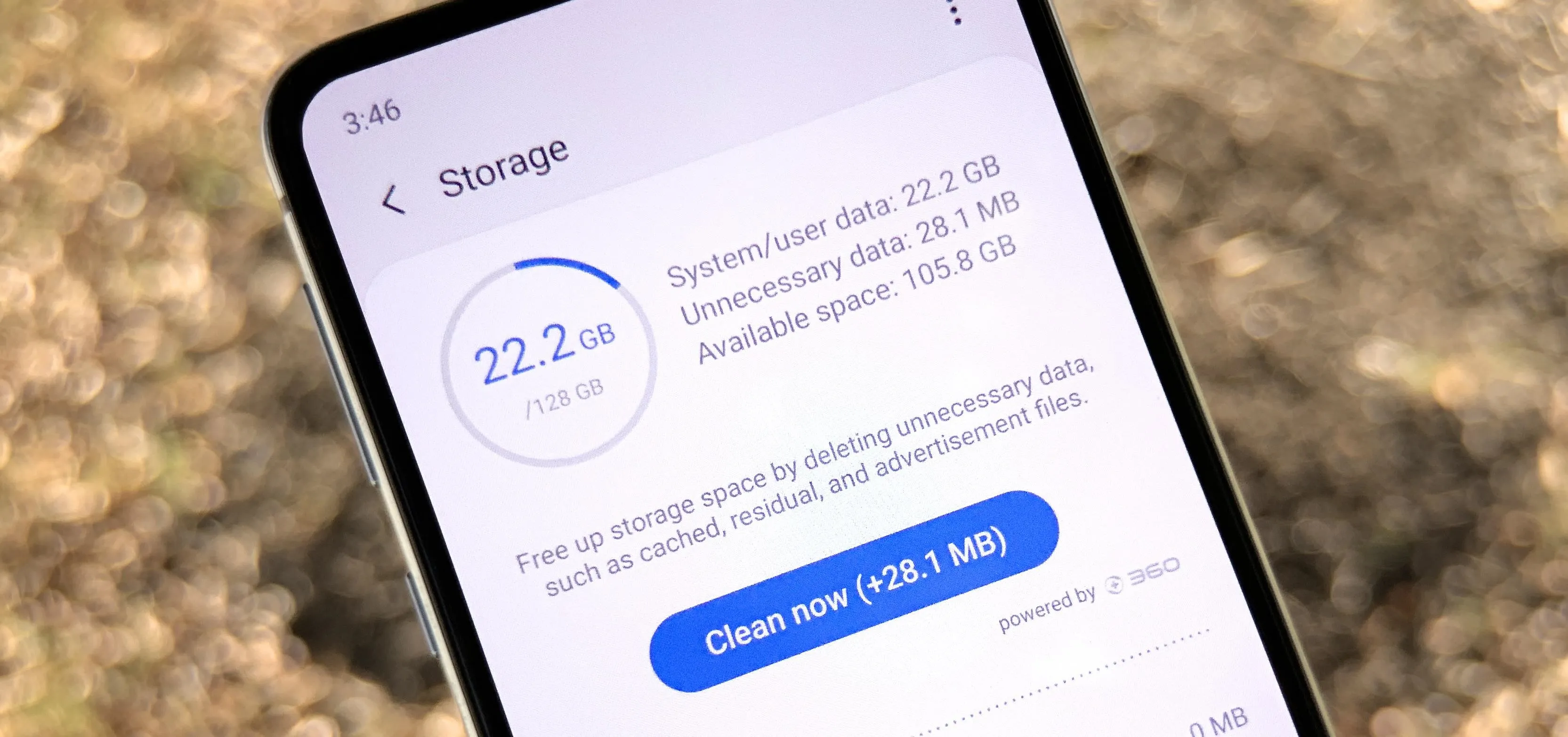
All recent Samsung phones have a menu called Device Care in Settings. This is a set of features that help optimize various parts of the phone for better performance. One of these features will scan your internal storage to find unused apps and other unnecessary data, then make it easy to delete these files to free up space.
But if you look at the Storage menu in Device Care, you'll see "powered by +360" or similar. +360 is the icon for Qihoo 360, a Chinese data-mining and antivirus company which has some shady practices. Their software has been alleged to be spyware, as reports indicate their willingness to hand over any data to the Chinese government. And this same company is powering the storage scanner on your device with full access to your data.
Recently, a Reddit user found that this app is communicating with 360's servers during each scan. But this isn't new — XDA users found the same shady behavior last year. While we don't know what data is being sent, we do know the servers are Qihoo 360's Chinese servers.
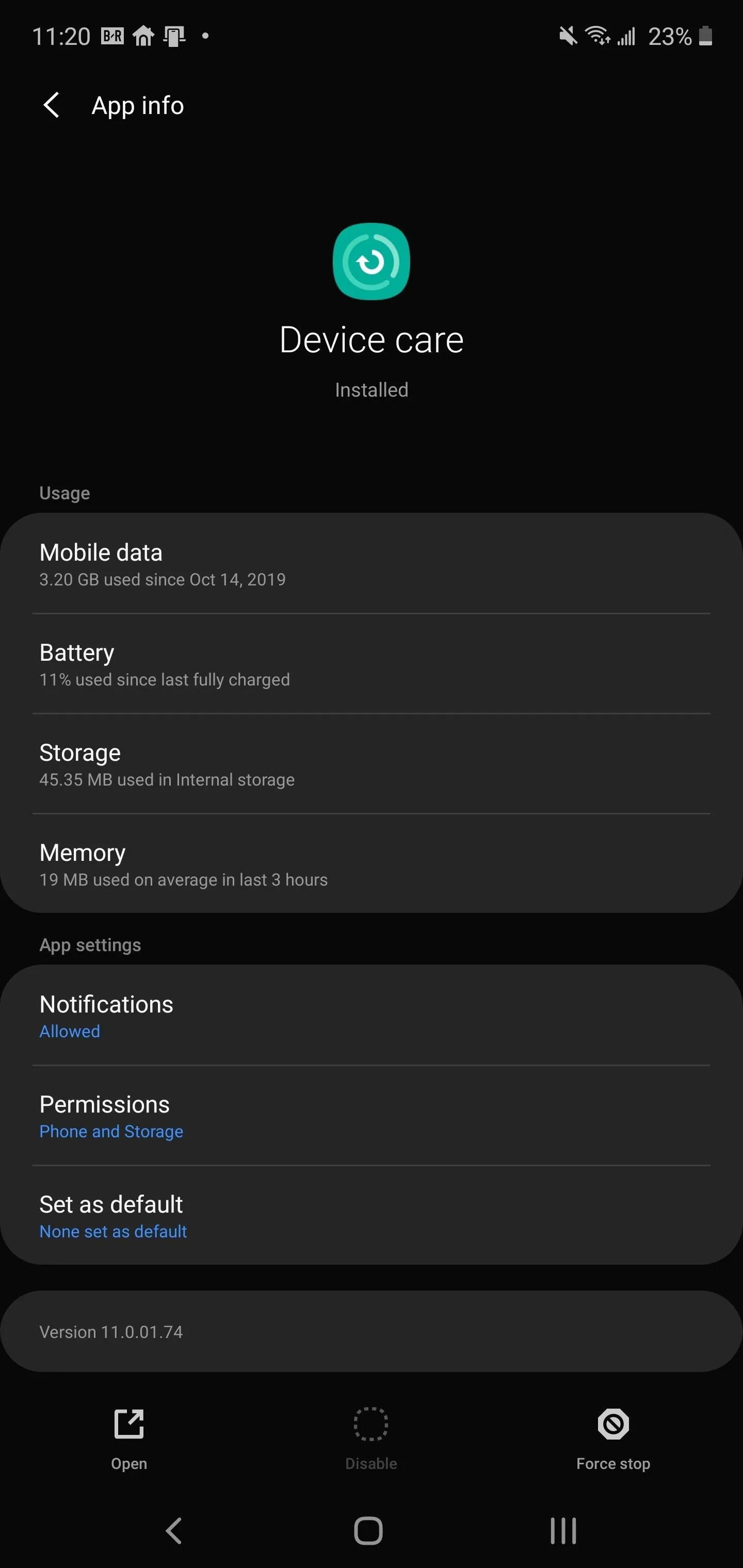
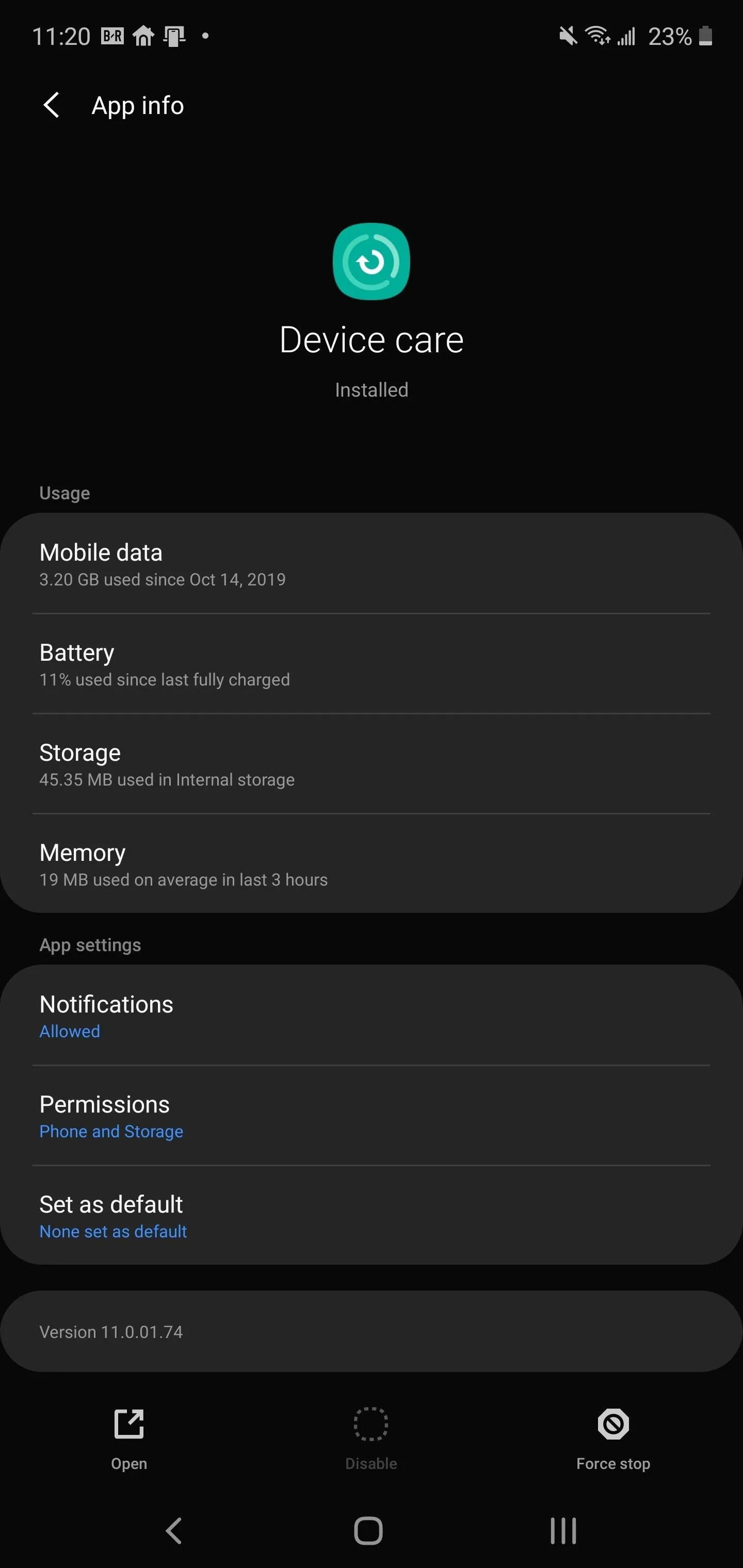
If it were solely the storage scanner in device care, you could possibly just disable the problematic app with ADB. But the same communication with Qihoo 360's servers has been observed in other pre-installed apps:
- Samsung ApexService
- ANT+ HAL Service
- Application installer
- Assistant Menu
- AirCommandManager
And these are just a few of the apps. This means, potentially, Qihoo360 could have data pertaining to all aspects of your phone usage. And since all these services are so deeply integrated, you can't just uninstall them. Instead, your best bet is to block network traffic from your phone to Qihoo 360's servers.
Blocking Qihoo 360 Servers on Your Galaxy
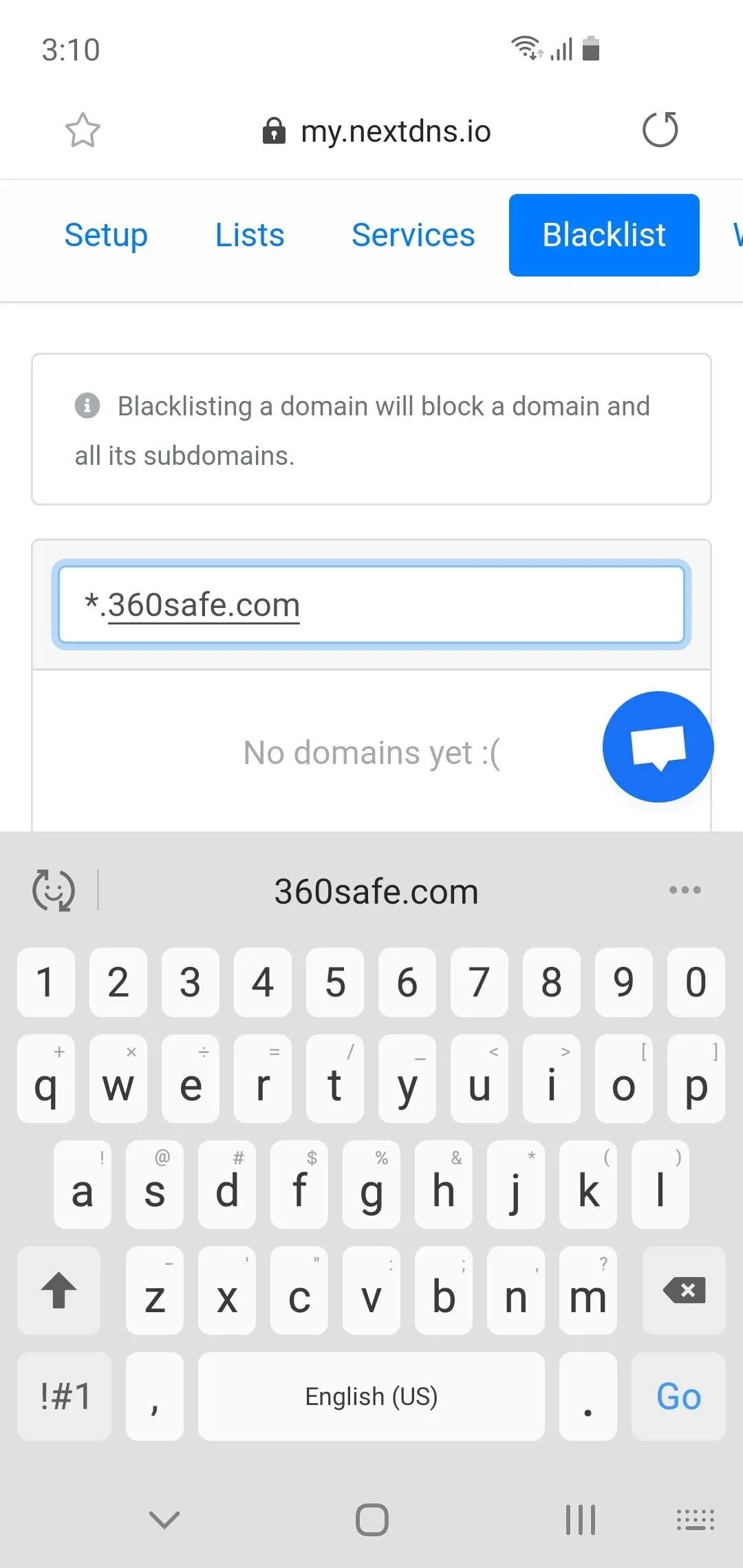
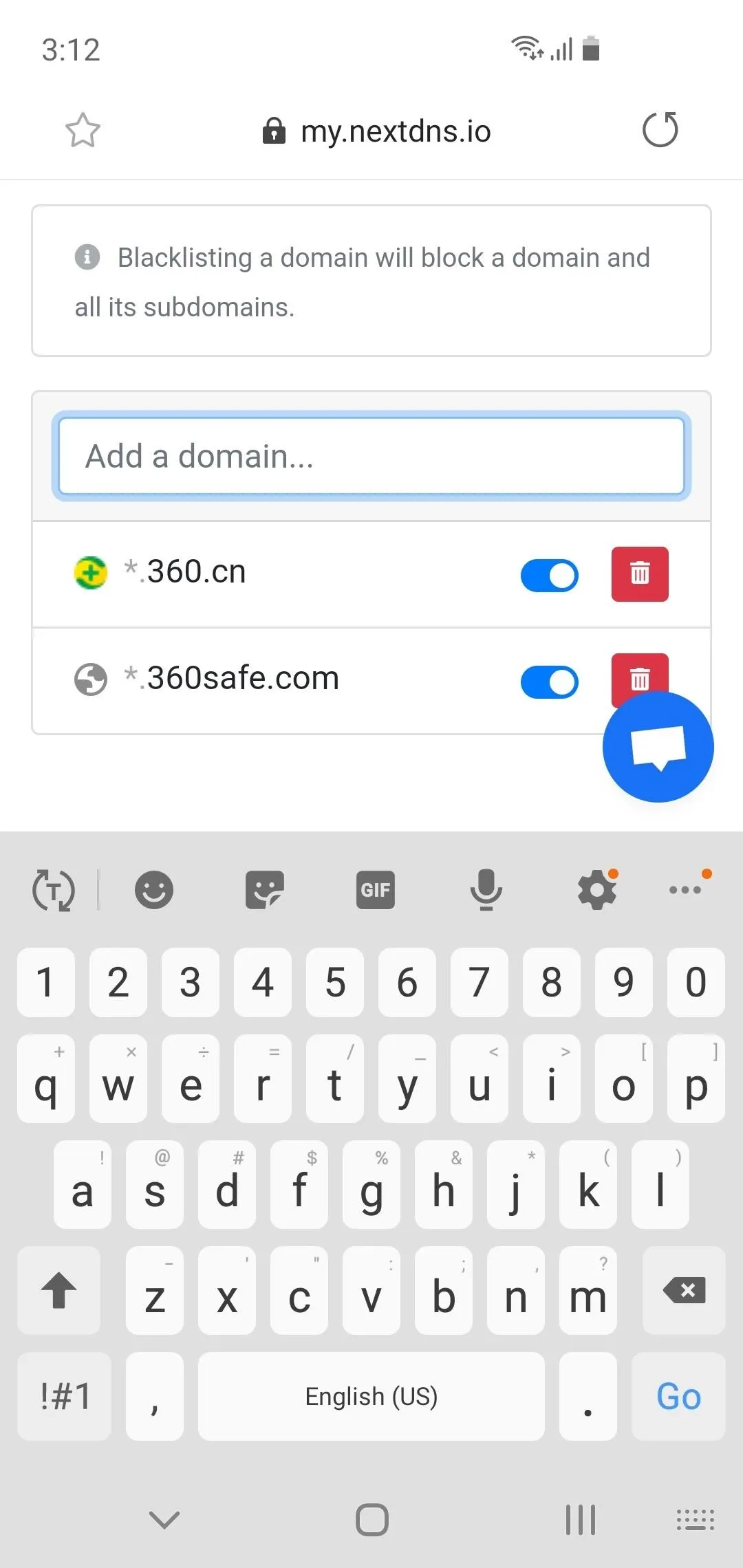
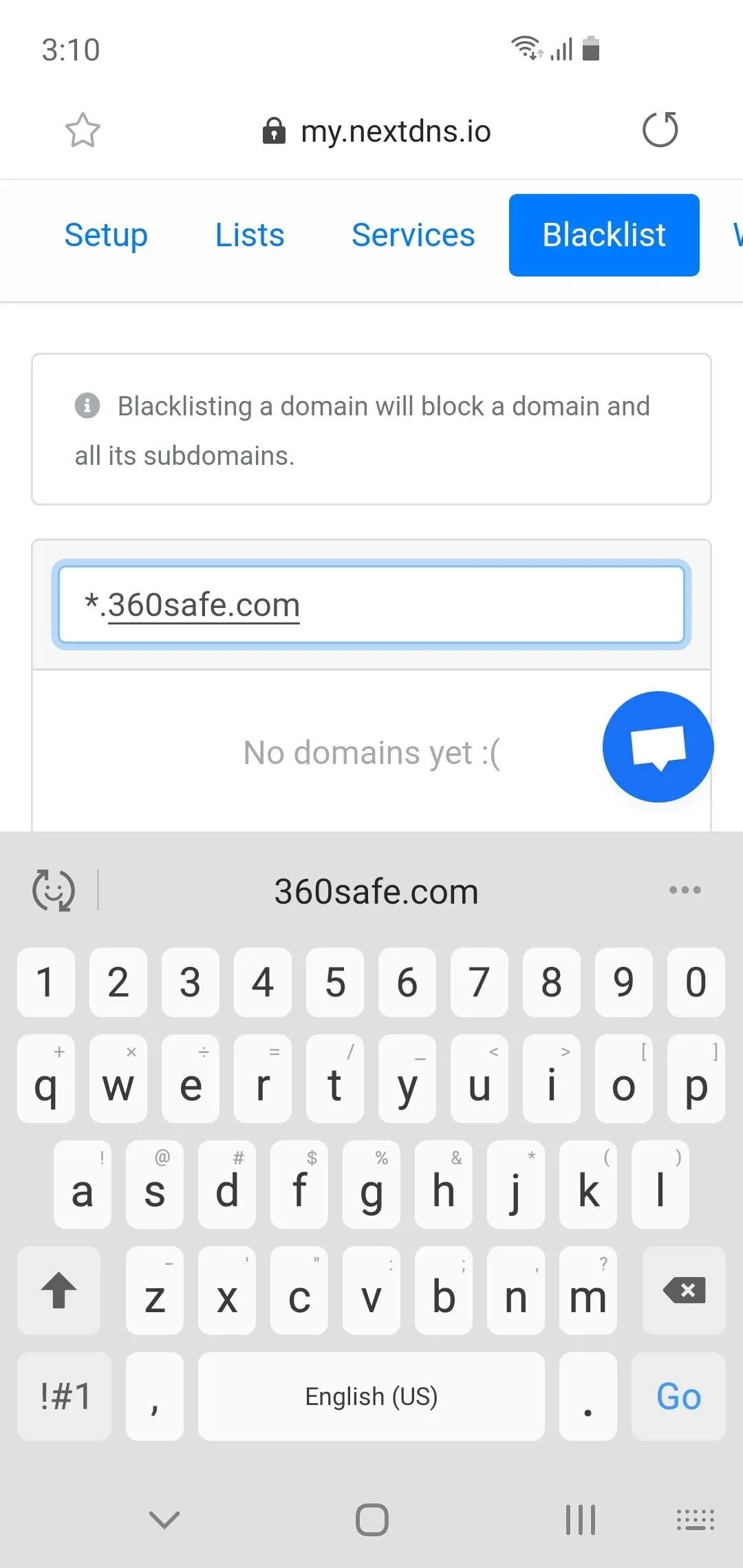
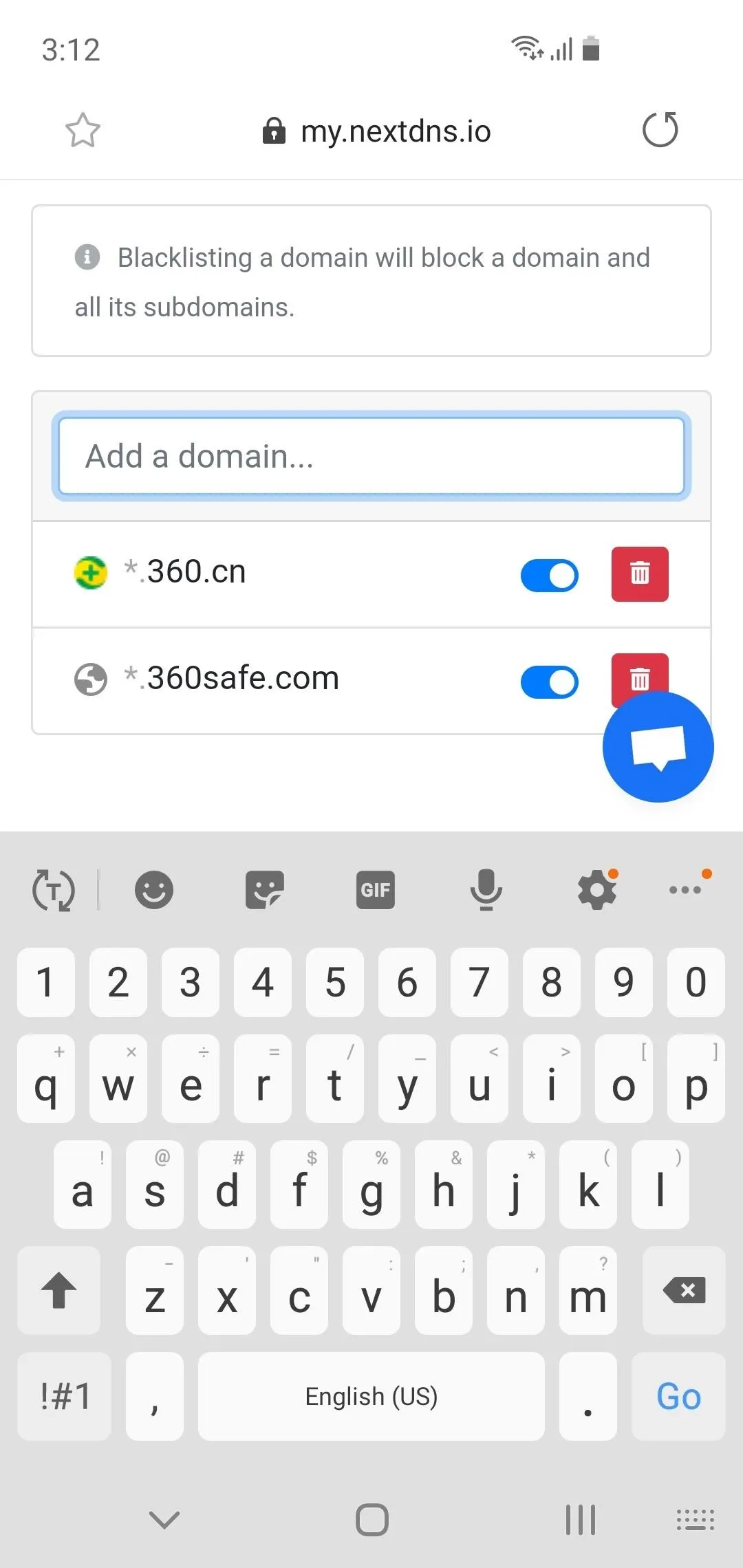
First, visit NextDNS from your phone and tap the "Try it now for free" button. Select the Blacklist tab and enter both of the following URLs one by one in the "Add a domain" text box:
*.360safe.com
*.360.cn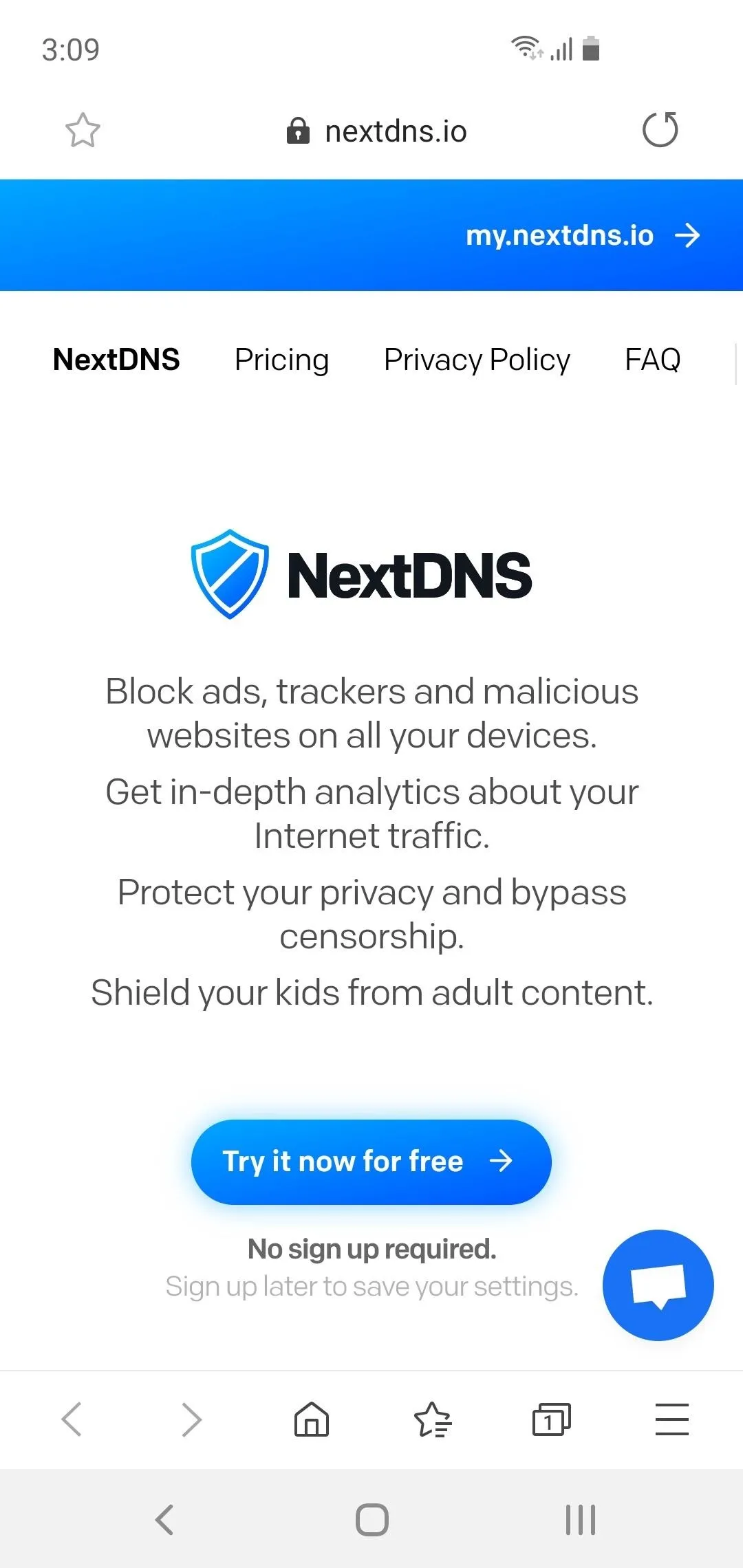
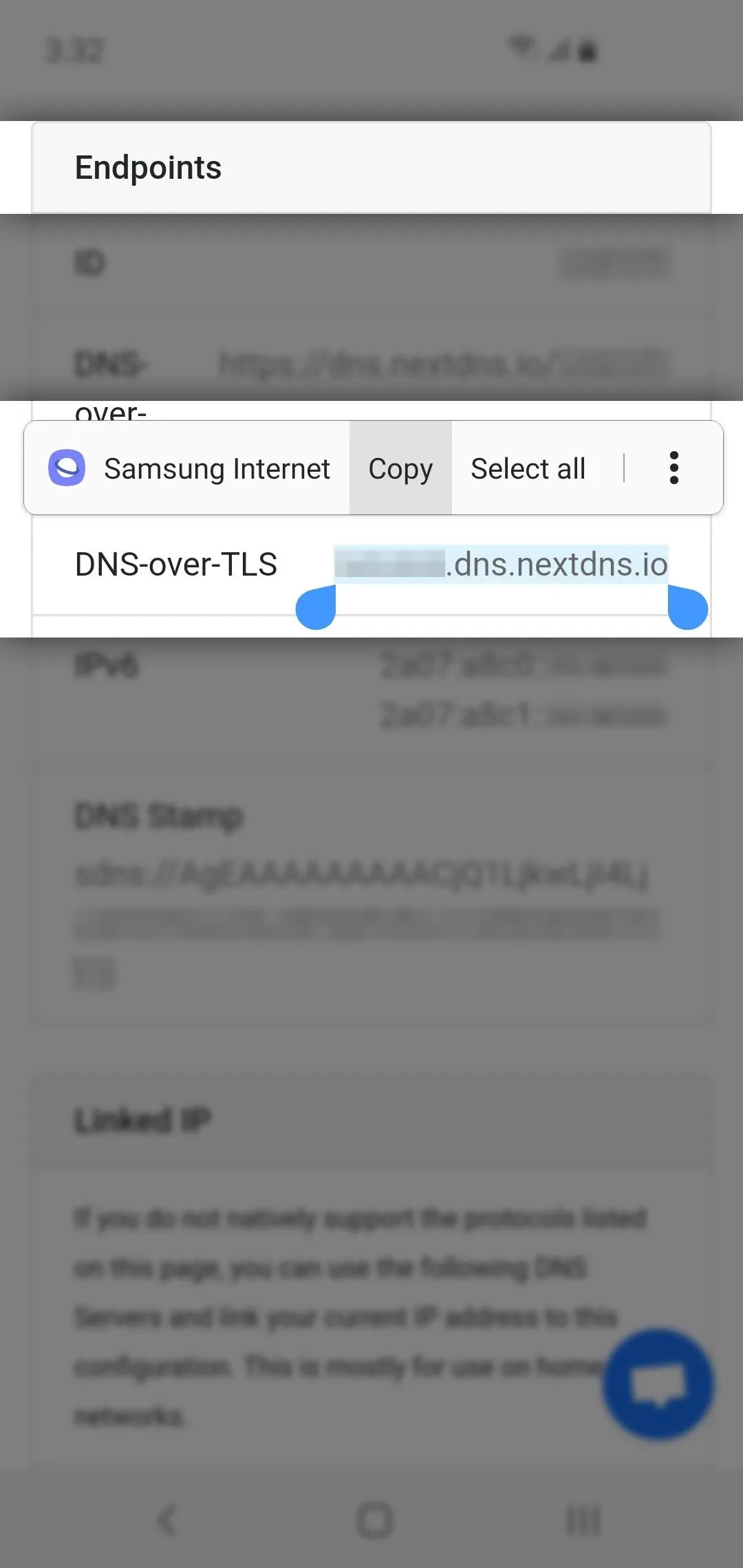
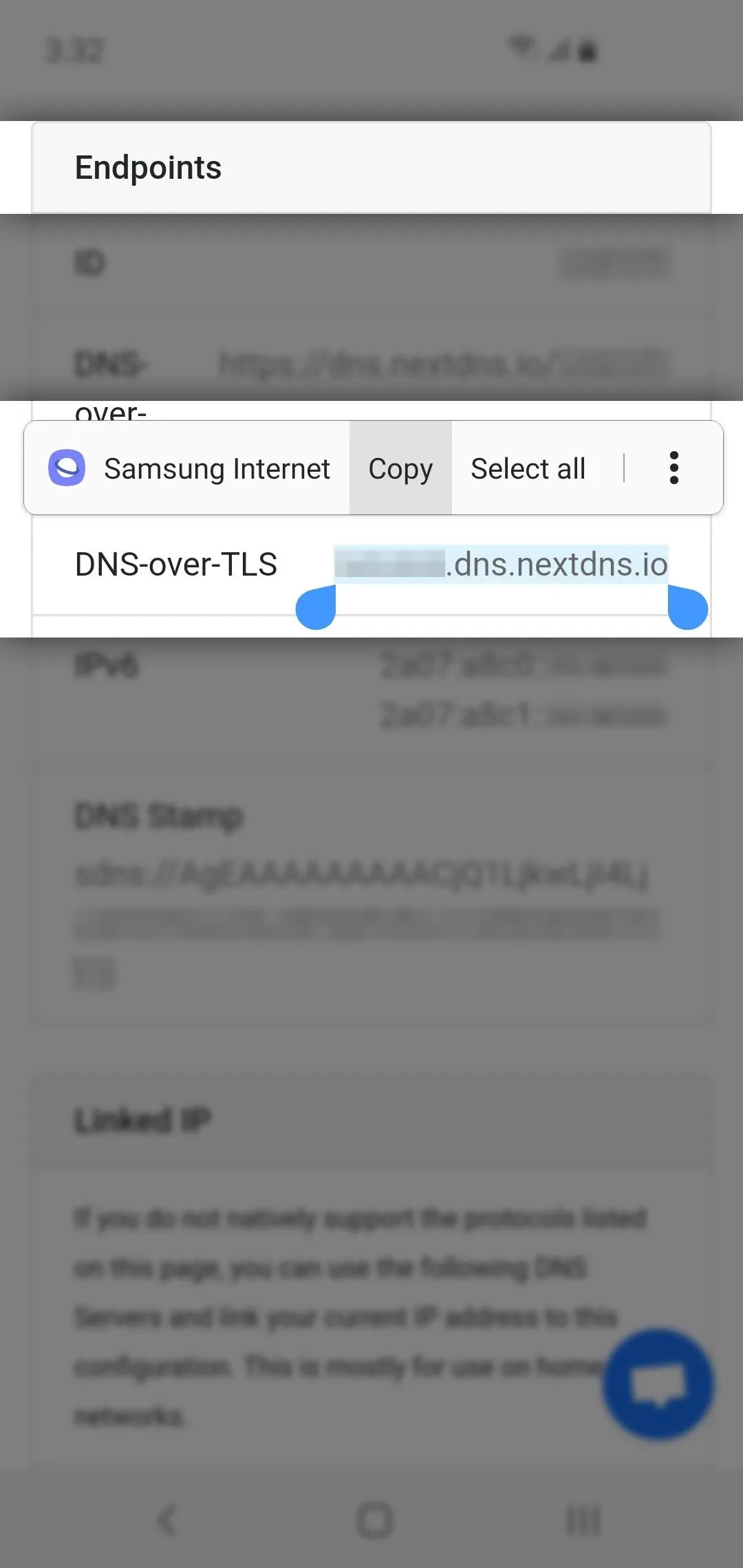
Return to the Setup tab and scroll down to the Endpoints table. Long-press the URL to the right of "DNS-over-TLS," then select "Copy" on the popup. Make sure the entire URL is selected — even the ".io" at the end!
Now, open your phone's Settings and choose "Connections," then "More connection settings." Tap "Private DNS," then select "Private DNS provider hostname" on the popup and paste the URL you copied into the provided field. Hit "Save," and now, when any app tries to send data to Qihoo 360's servers, it will be blocked.
Not only does this method work on both cellular and public Wi-Fi, but it starts immediately when you turn on your phone. No VPN connection needs to be established first, leaving a gap where your data could get out. And as a bonus, you are using DNS-over-TLS, protecting your browsing history from hackers and your ISP.
Cover image by Jon Knight/Gadget Hacks




















Comments
Be the first, drop a comment!