When BlackBerry made the move to Android OS, they were aware of the limitations it presented. Unlike with BB10, they didn't create the operating system and would have to deal with the vulnerabilities already included. As a result, they added numerous security enhancements, and at the heart of this is DTEK.
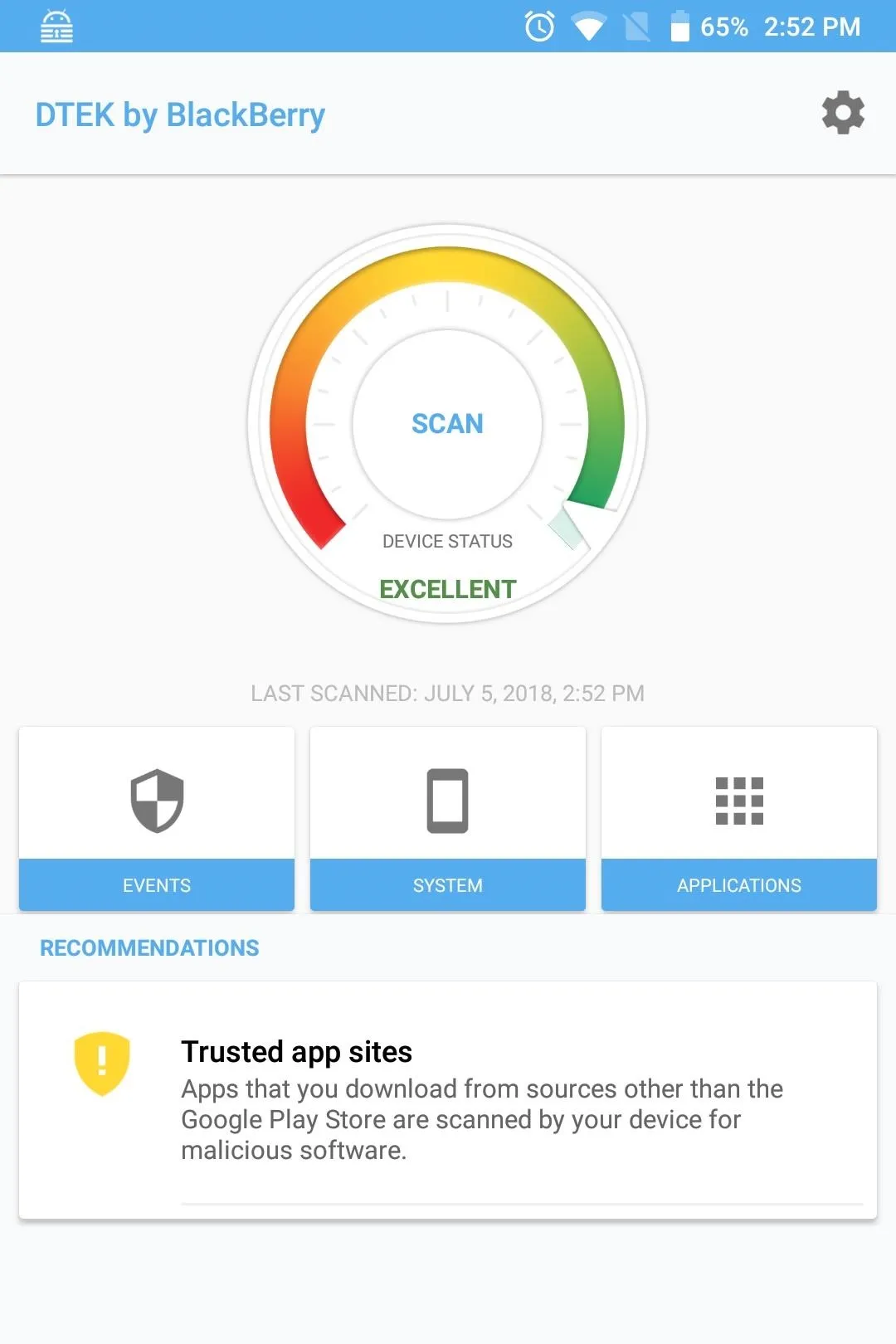
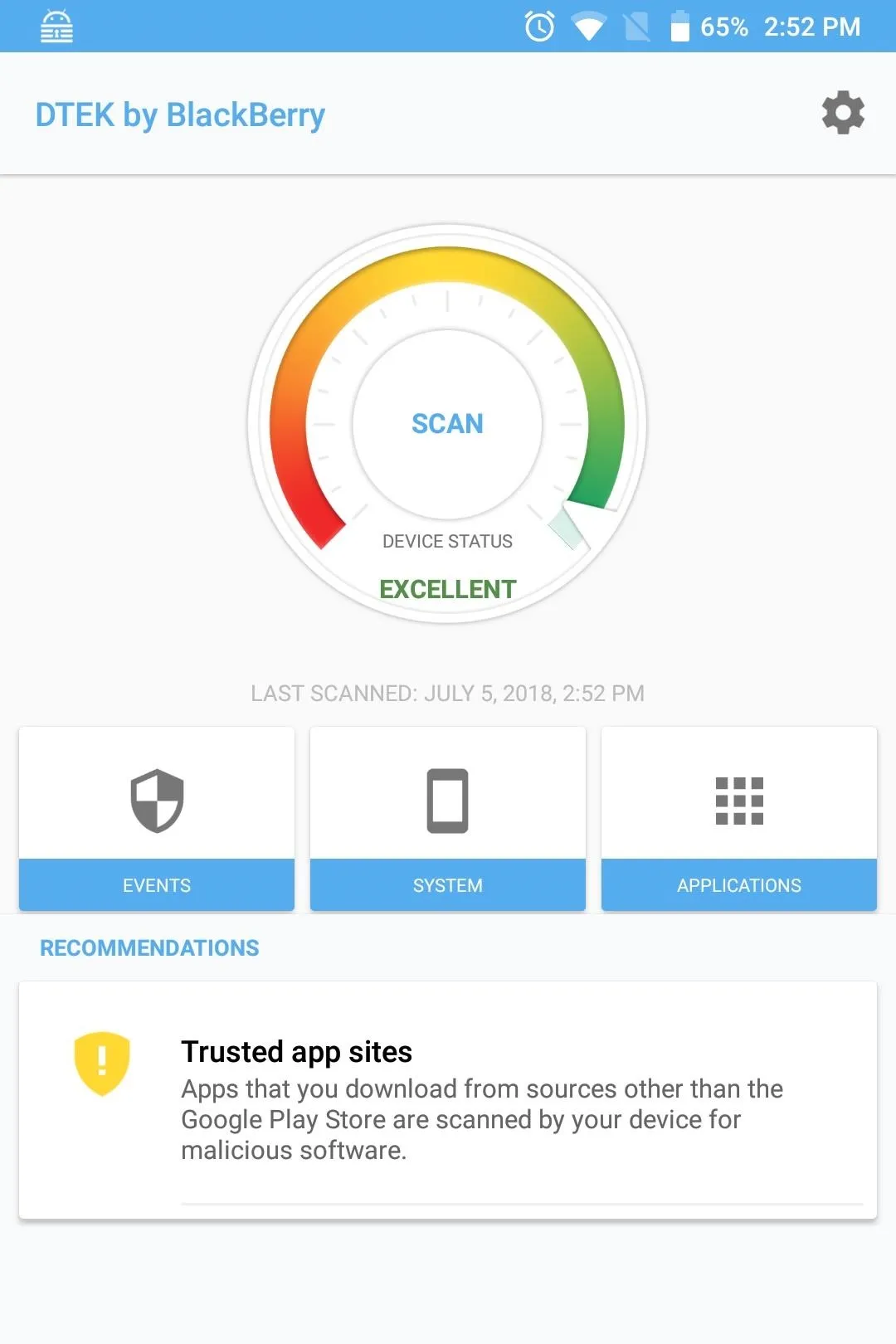
DTEK is a dashboard for the advanced security system included with every Android-powered BlackBerry. It has a number of software tools that improve the security of Android and ensure that your phone remains protected for the entirety of its life.
While many of the tools operate automatically, BlackBerry has provided its customers with some options to further improve security if they so choose. For those of us who are particularly security-conscious, it's only when you adjust things in DTEK's settings menu that your BlackBerry device become almost impenetrable.
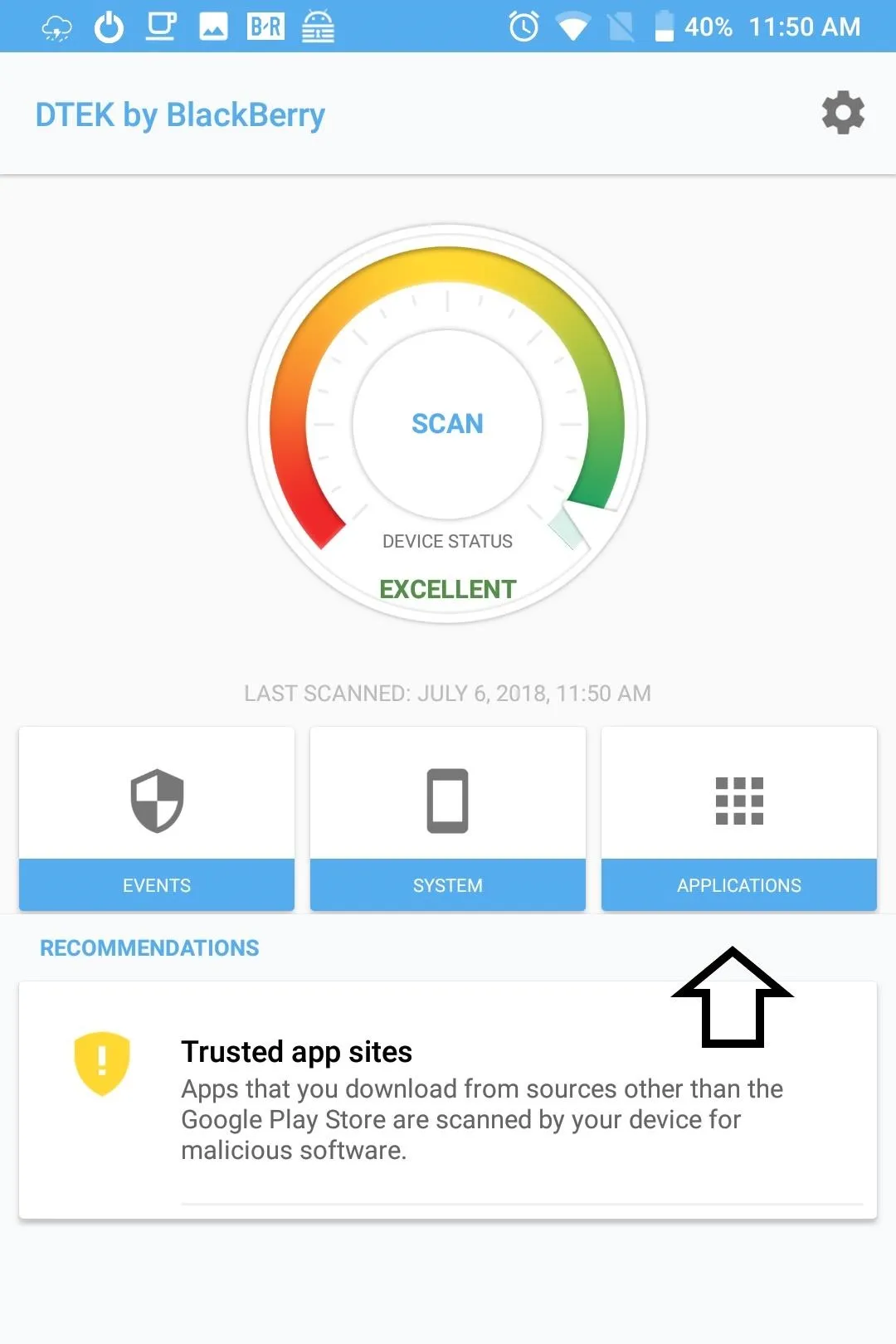
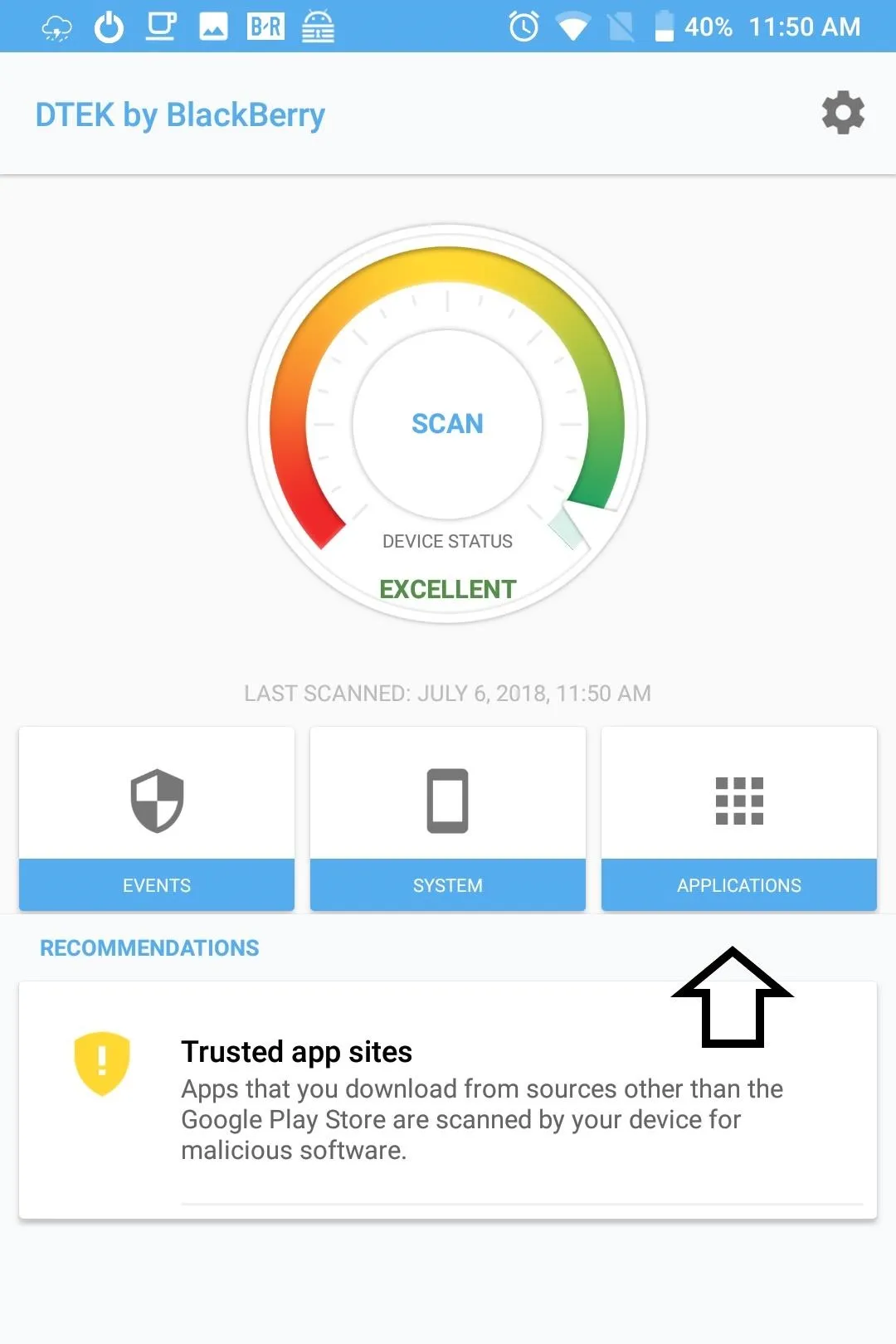
Quickly Identify Security Issues
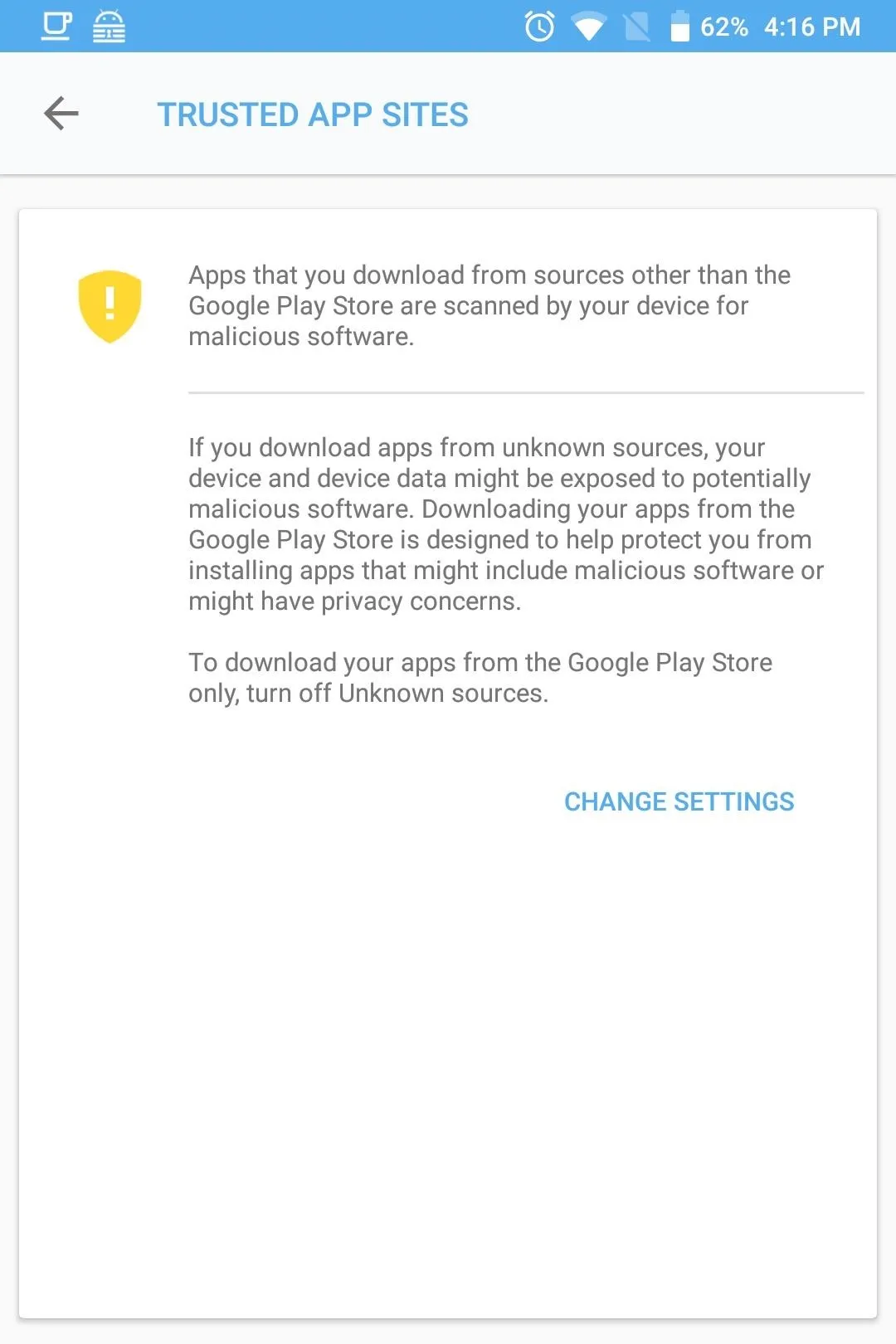
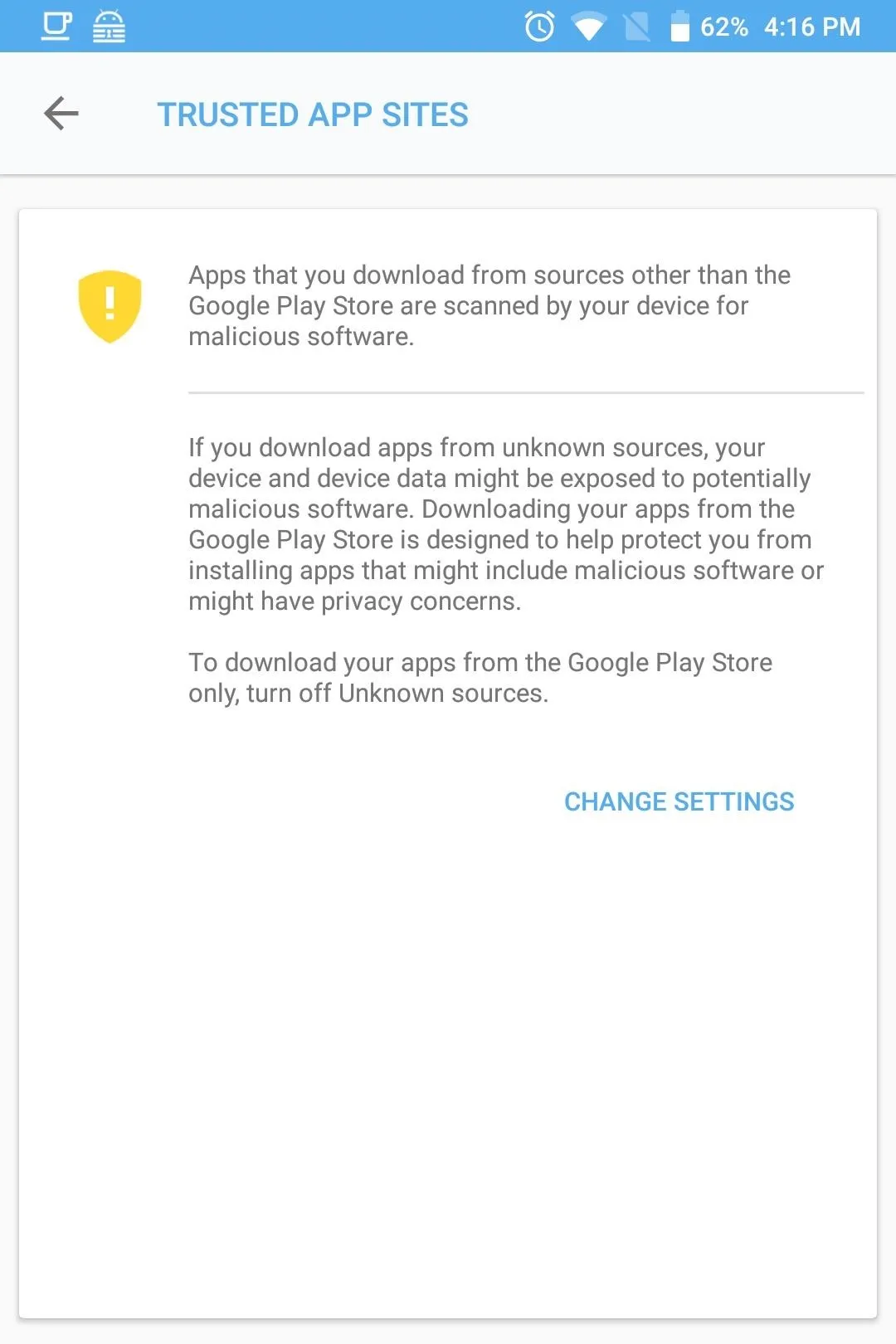
One of the first things you will notice on DTEK's homepage is the Recommendations section. Recommendations are changes you should make to improve the security of your device.
For example, if you enable the hidden "Developer options" menu or grant third-party apps the ability to sideload apps, you will see alerts here explaining why it can compromise the security of your device and a button to correct the situation. Keep an eye out on this section.
Manage Sensitive Permissions
With stock Android, users can manage access to data obtained from various sensors and apps. Specifically, Android allows you to enable (or disable) access to this data by specific apps requesting permission. However, some apps prevent you from disabling their access by force-closing the app after permission is revoked, or by bombarding you with a prompt to enable the permission the next time you open the app. Fortunately, DTEK offers additional control for this situation.
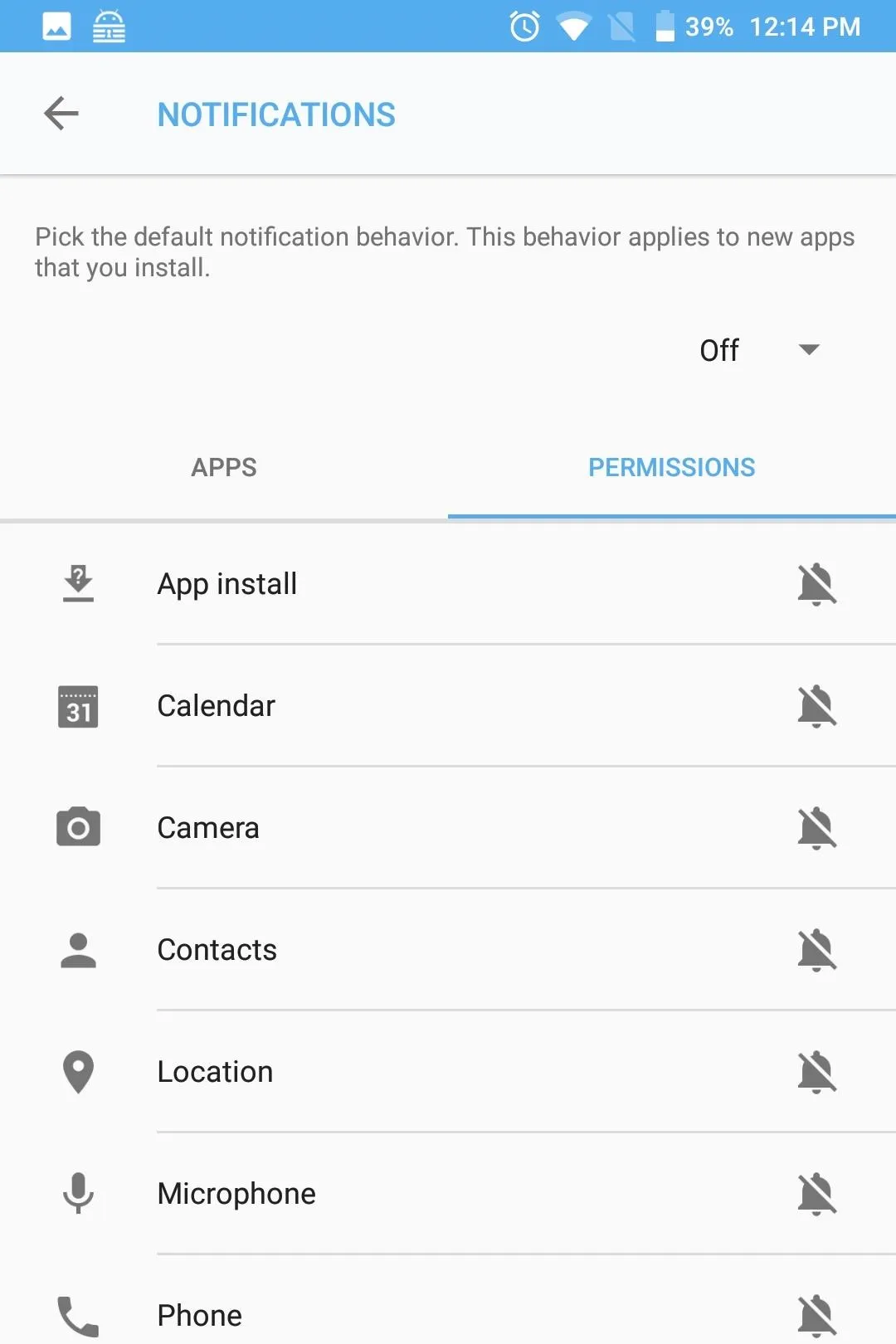
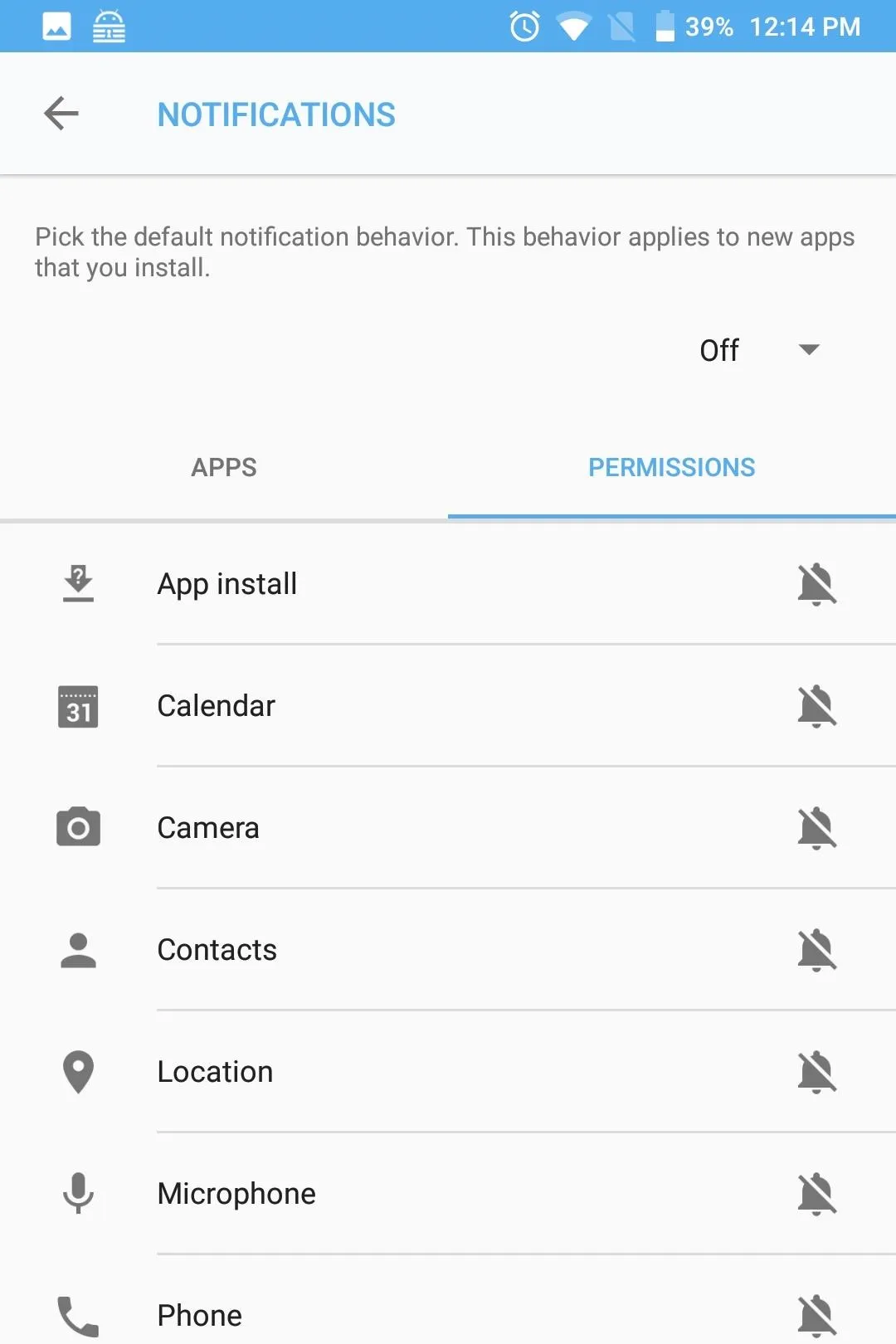
To access these controls, select the gear icon in the upper-right corner of DTEK's main menu and choose"Set sensitive permissions." A new page will emerge. By configuring a permission to "sensitive," any time an app requests permission to access its data in the background, you'll receive a notification.
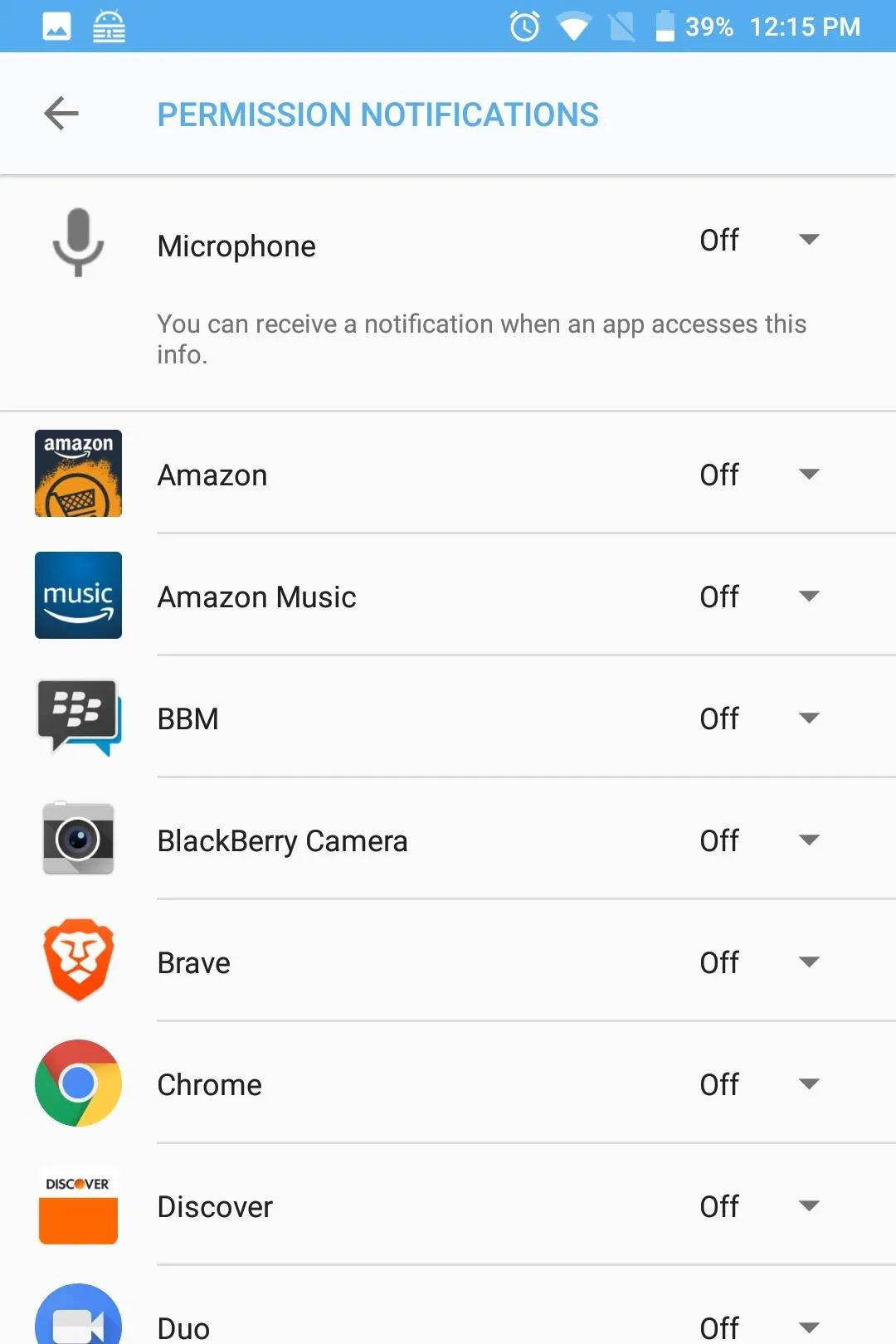
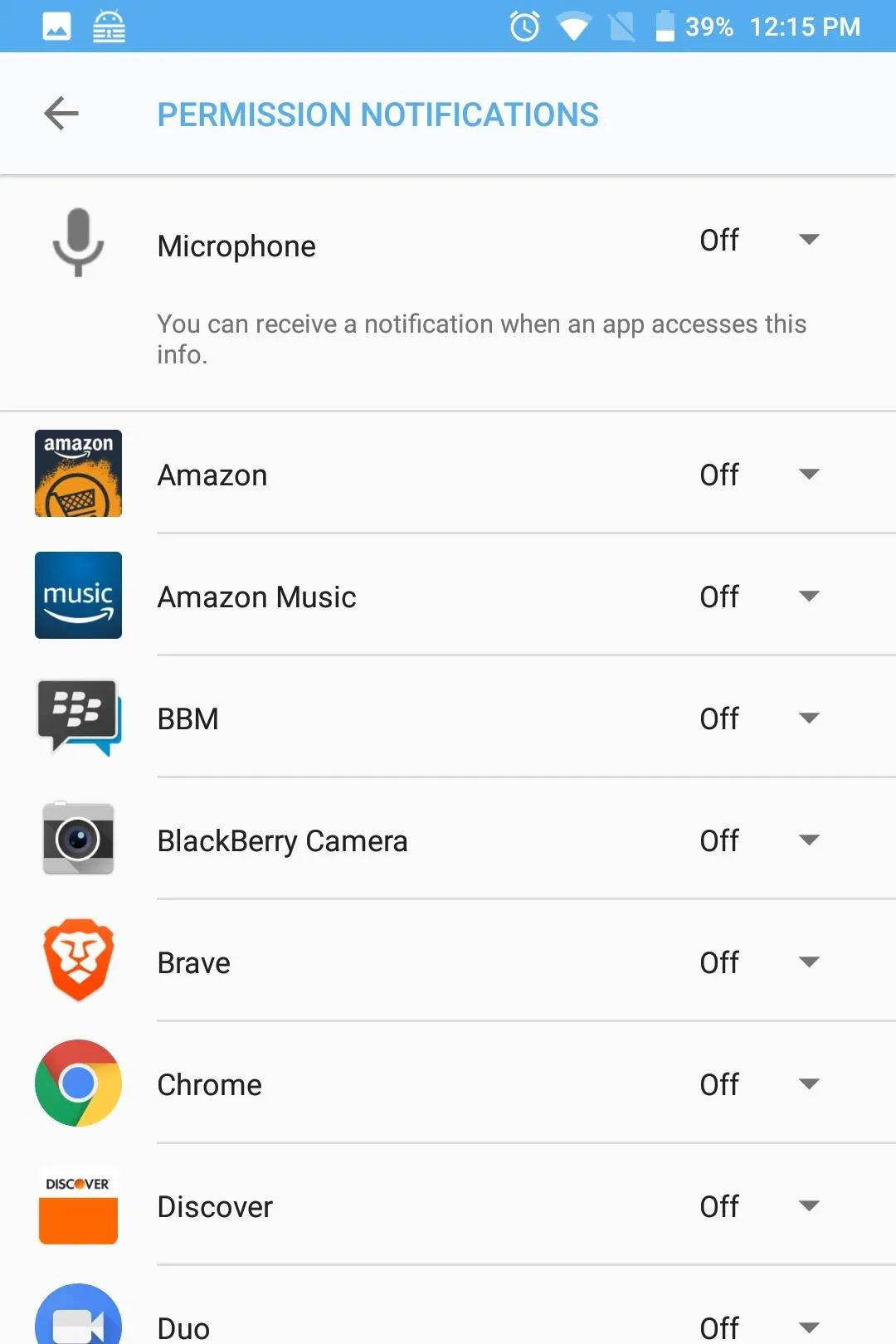
For years, a common hacking tool was to create malicious apps that perform one thing but steal your data in the background. For example, malicious apps could request access to the microphone or camera in the background to record you and blackmail you. However, by setting these permissions to sensitive, as soon as the app requests the permission in the background, you will know, allowing you to take the necessary action to protect your data.
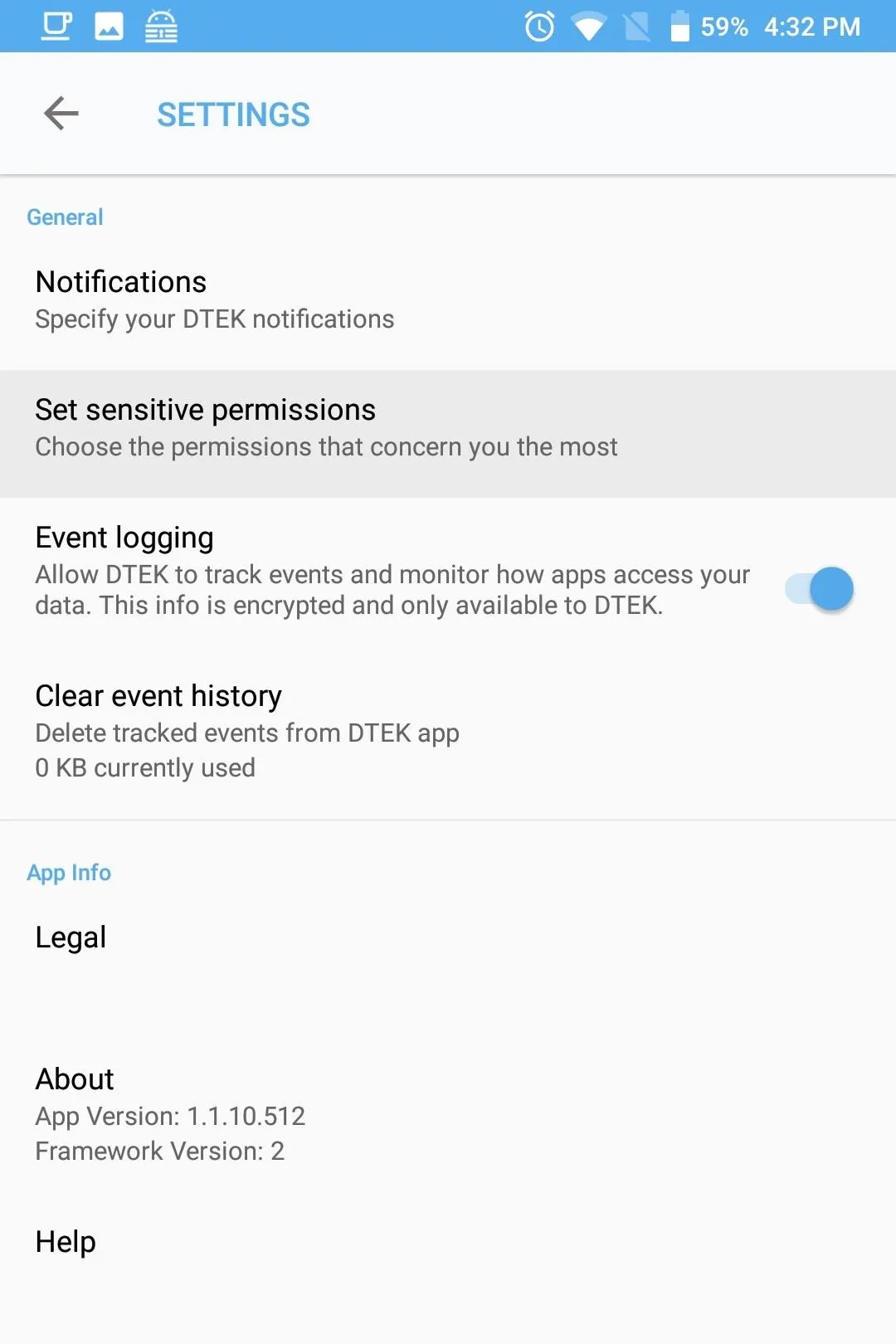
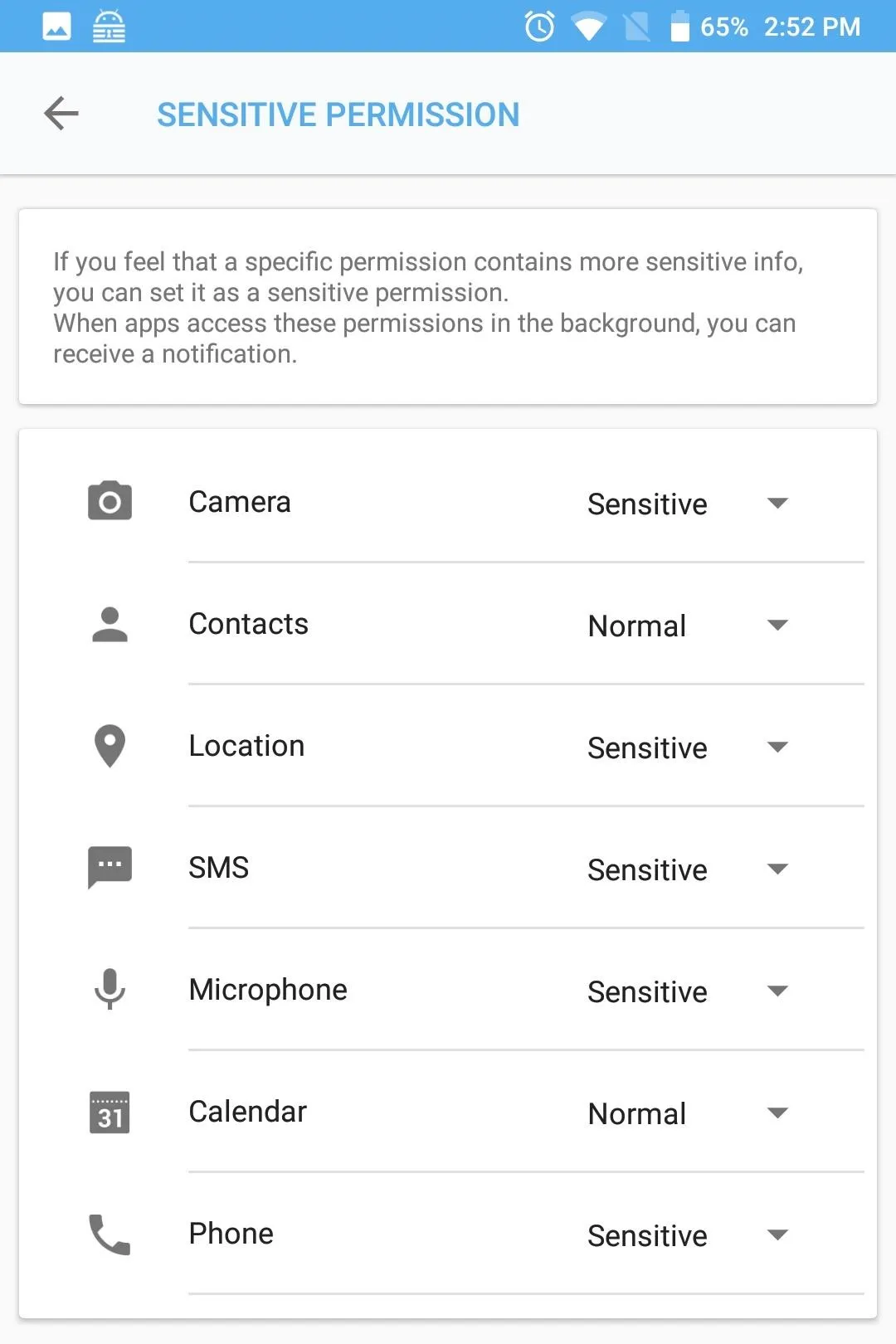
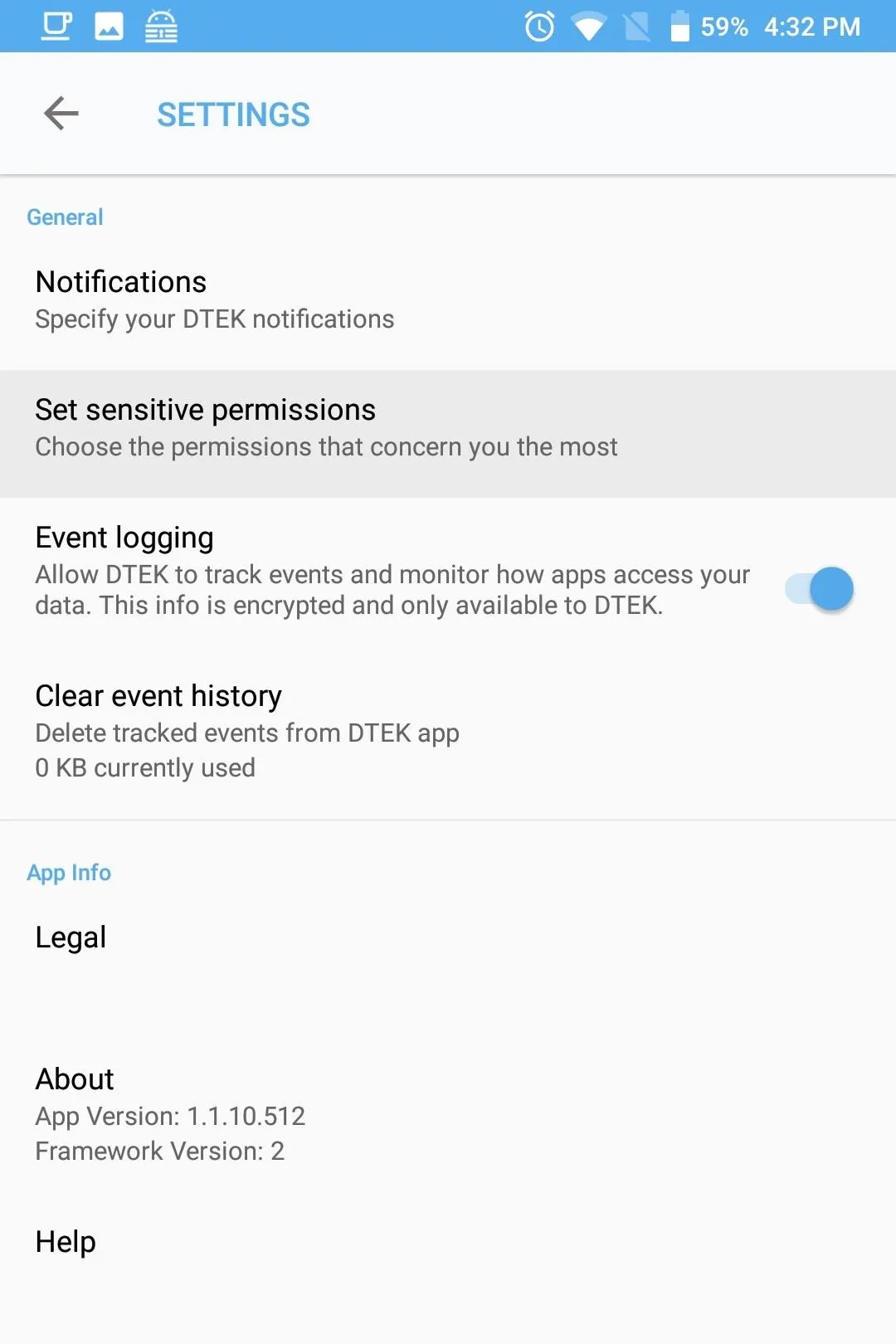
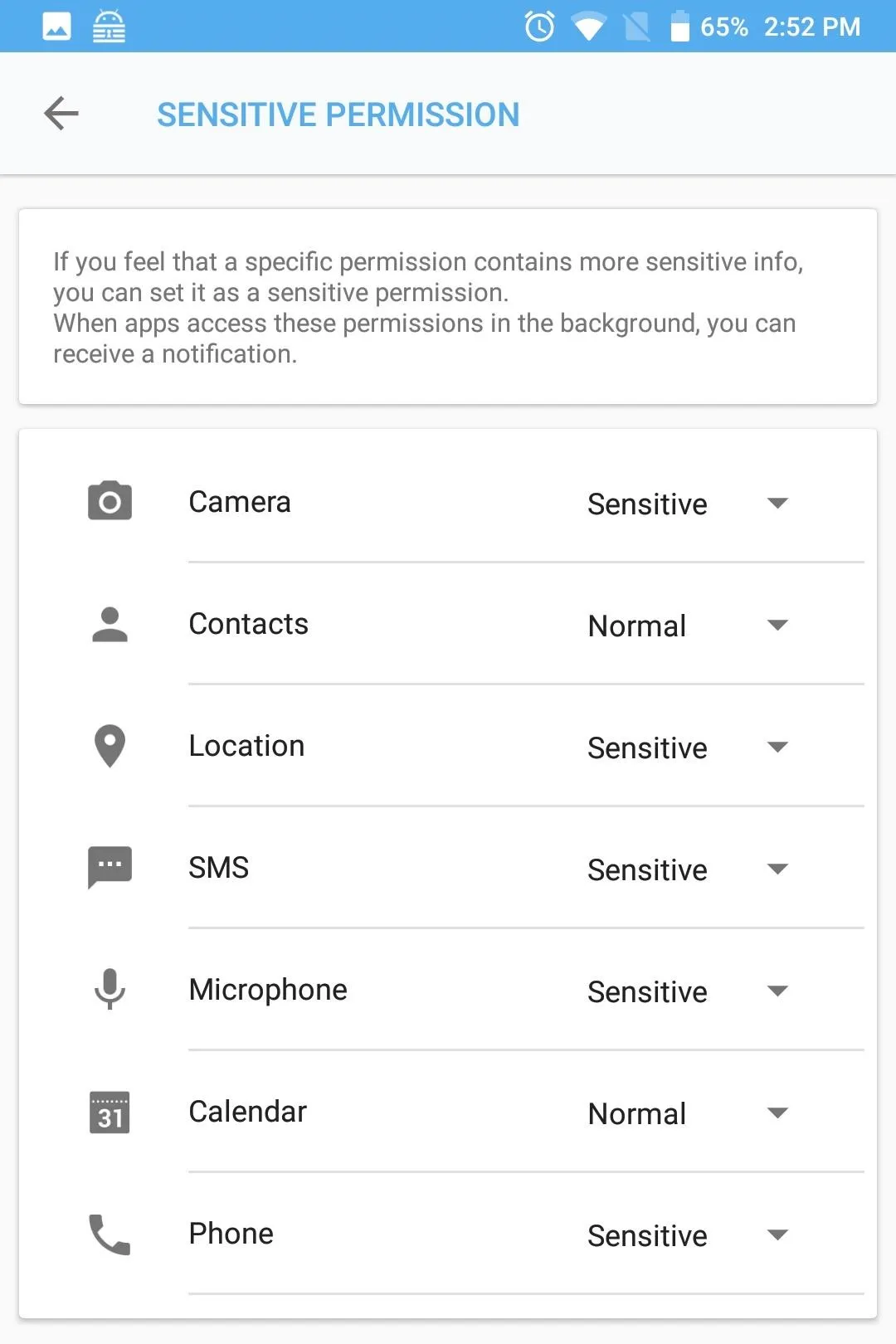
Google has just introduced a similar feature in Android 9.0 P, but it's limited to just the camera and microphone. However, with DTEK, BlackBerry is ahead of the curve, not only bringing the feature to Android 8.1 Oreo, but including all permissions.
Customize Alerts
Besides being notified for background requests for certain apps and sensor permissions, DTEK allows even further control via customizable notifications. To access this extra control, select the gear icon found on the main page of DTEK. Choose "Notifications," then select "Customize app notifications.
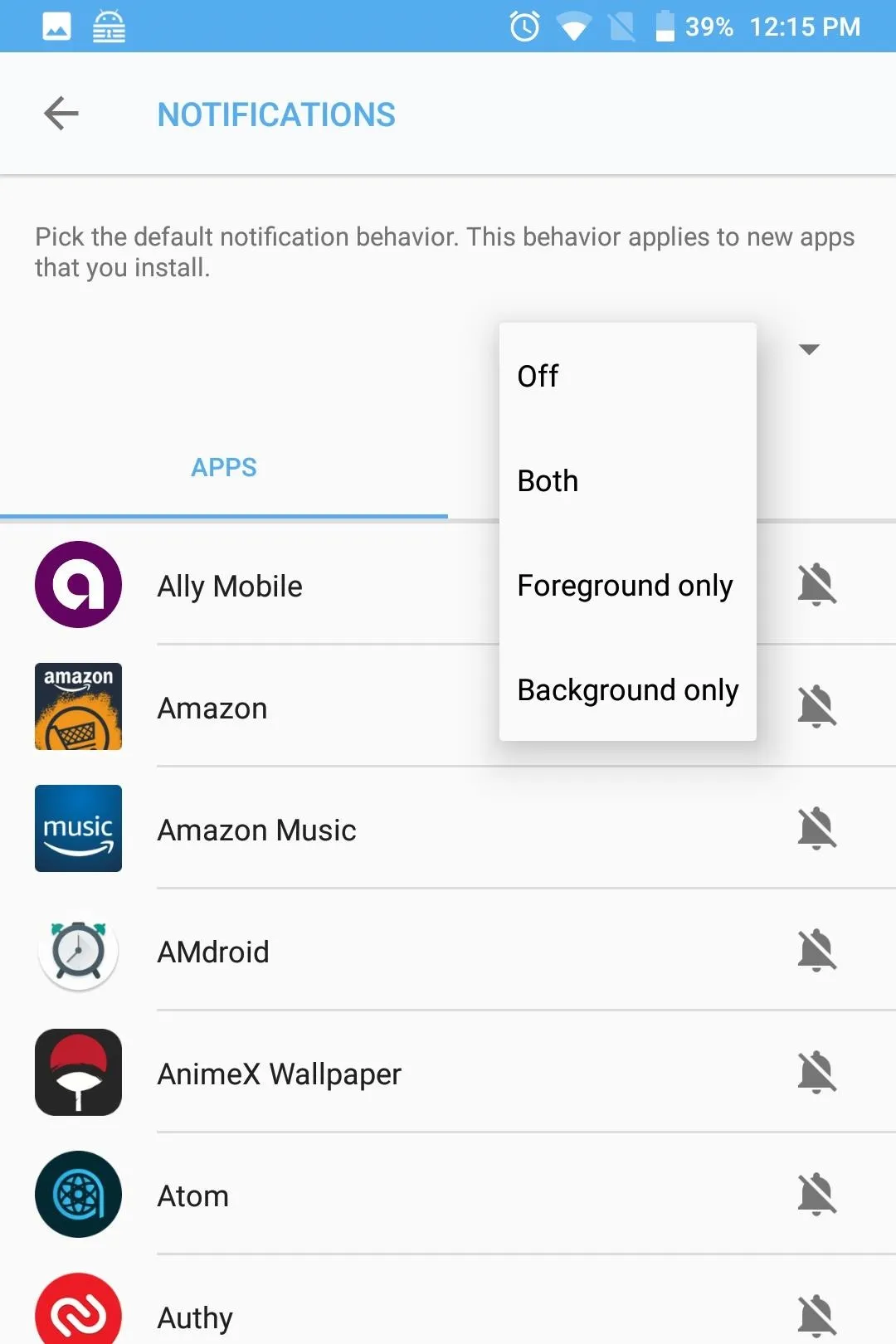
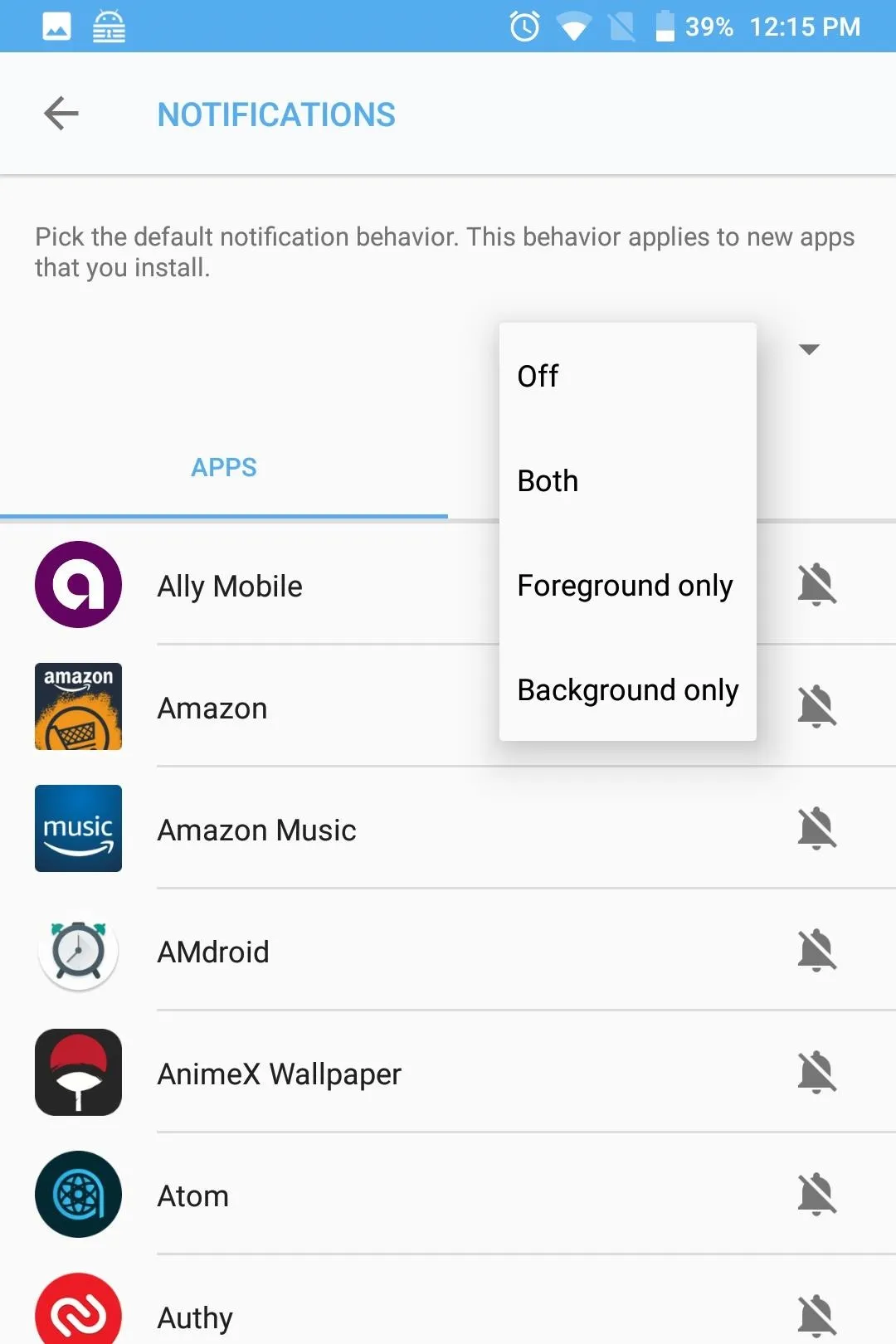
Here, you can choose to get notifications when a specific app asks to use a specific permission, or when any app asks to use a certain permission. The top option on the Apps tab manages how DTEK handles notifications for newly-installed apps. "Foreground" will alert you any time a new app accesses your data while you are using it, and "Background" will alert whenever the app is running in the background and requests access to your data. "Both" alerts you for each scenario.
You can also select an individual app to control how alerts are handled specifically for that app. The drop-down menu to the right of the app name manages alerts just like the main option above it does, so choose background, foreground, or both.
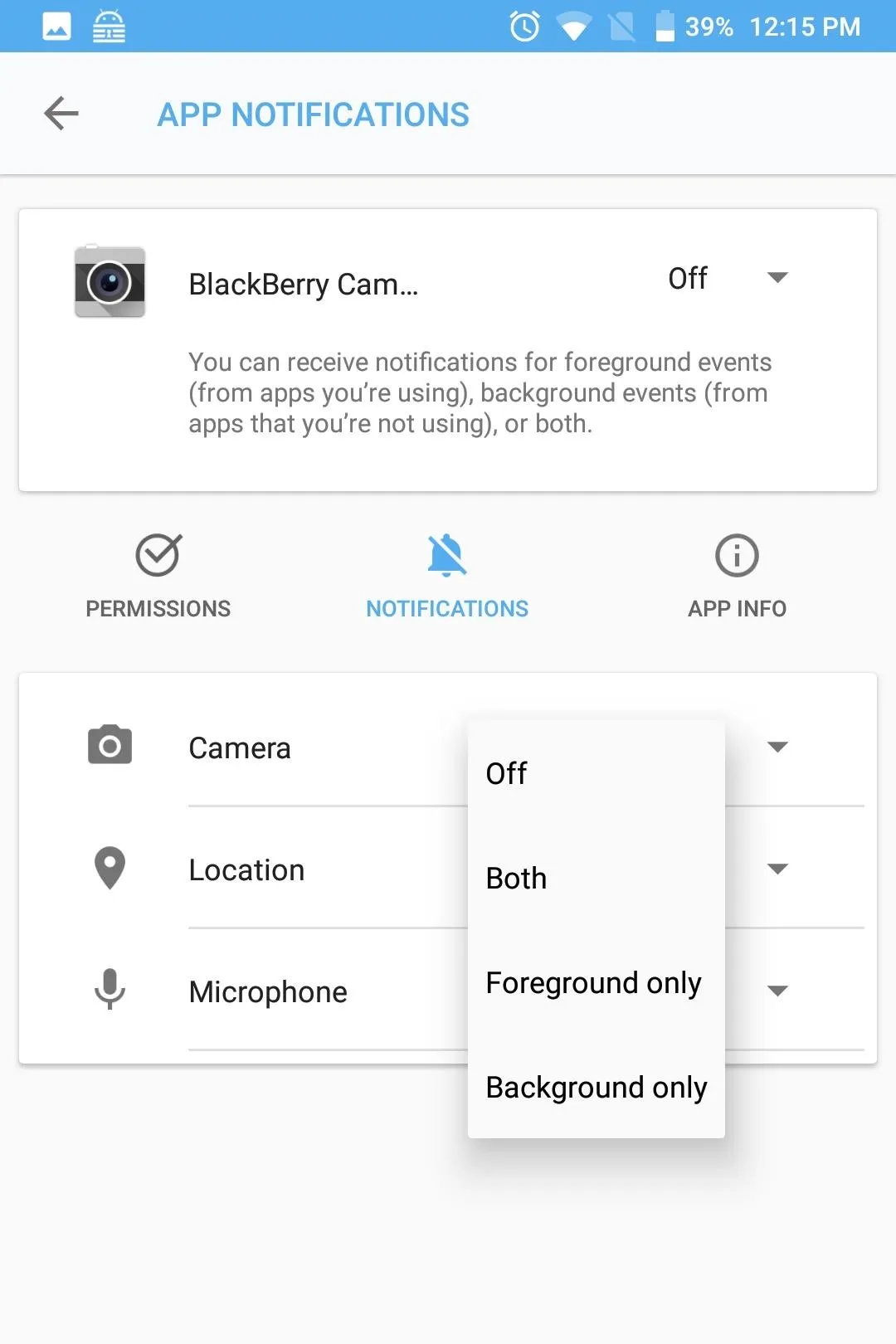
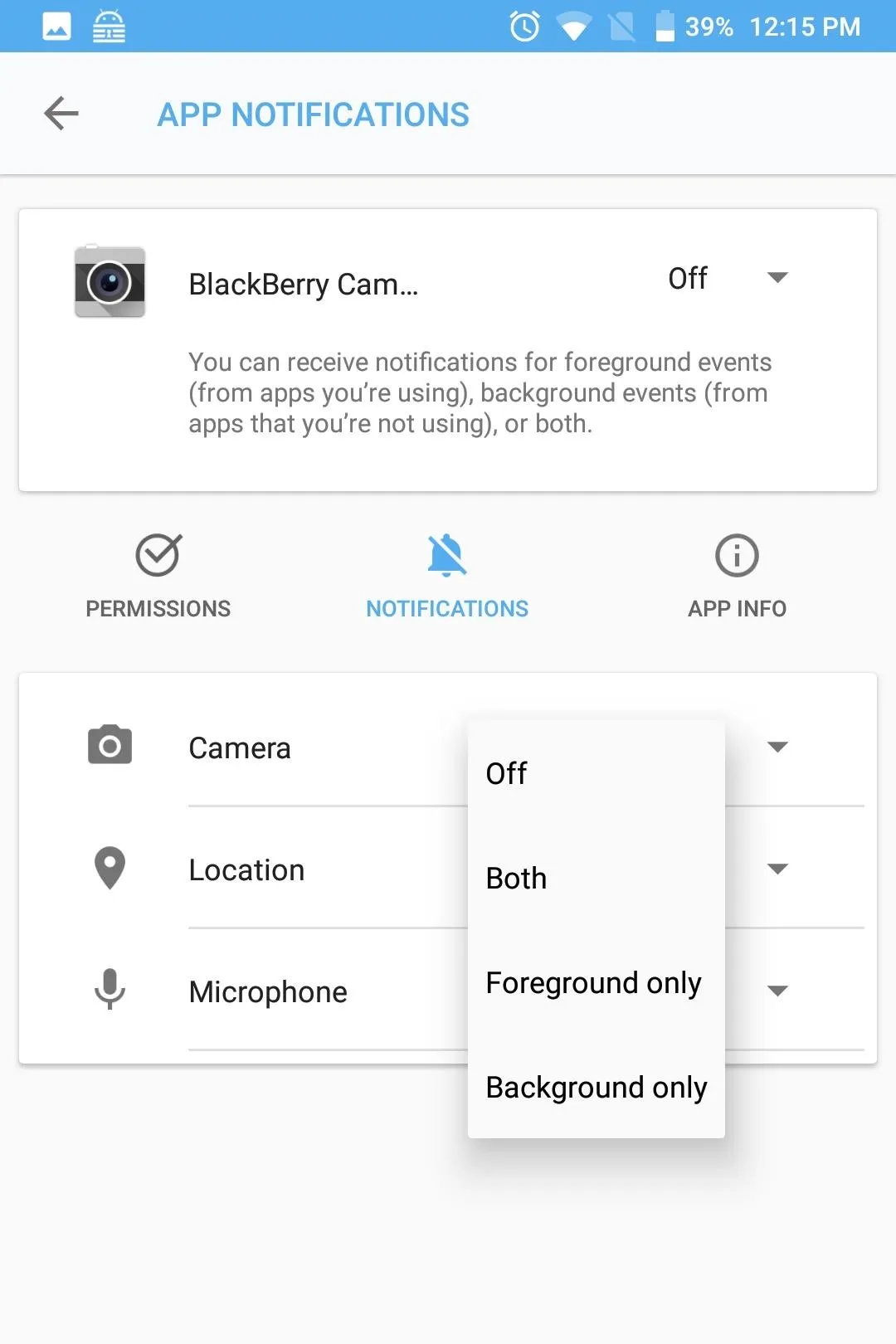
The Permissions tab offers the same functionality, but organized by the different types of permissions. By selecting the individual permission, you can manage how notifications are handled for any app which currently has access to its data. As with the Apps tab, the options available are "Foreground," "Background," "Both," and "Off."
Track Permission Requests
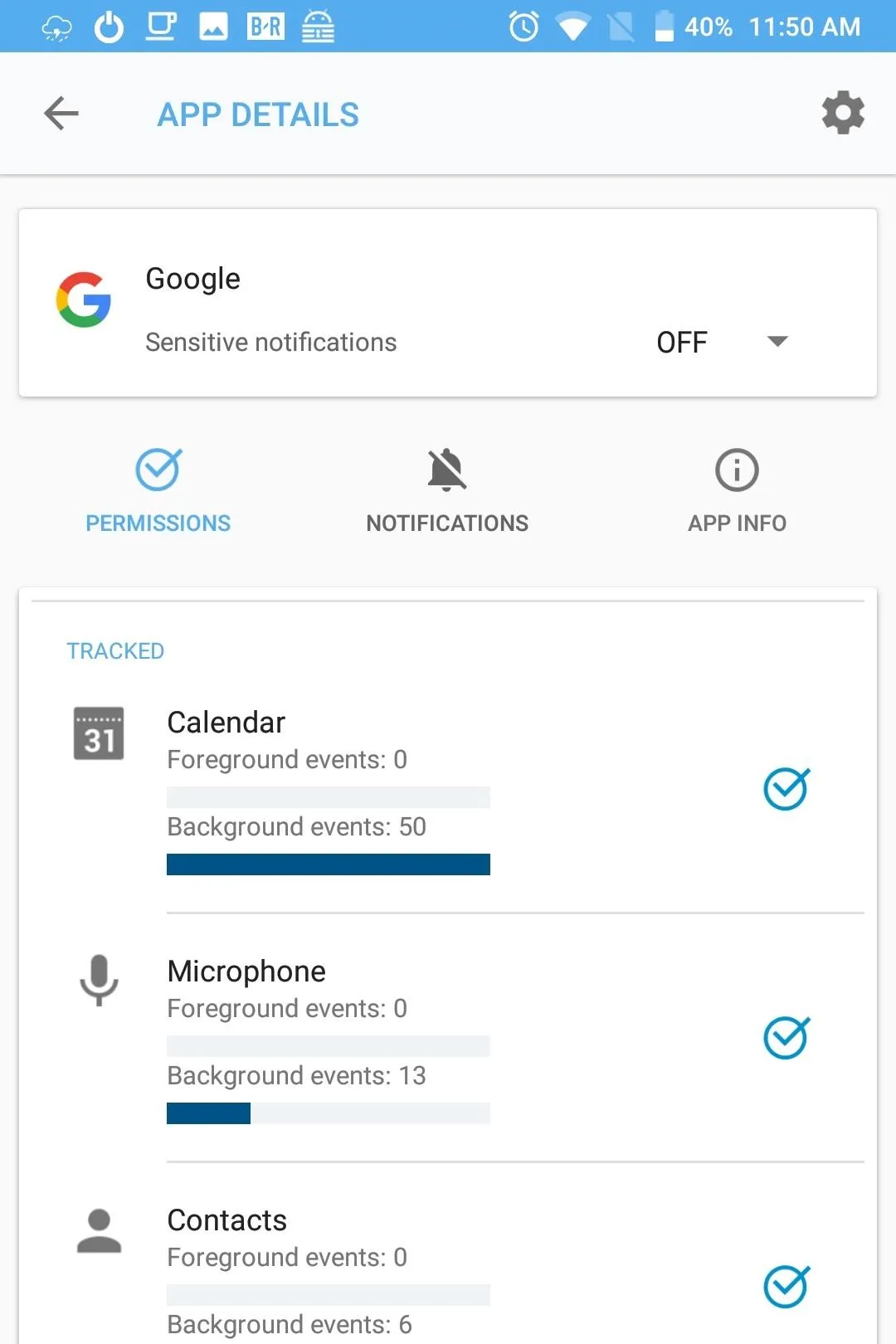
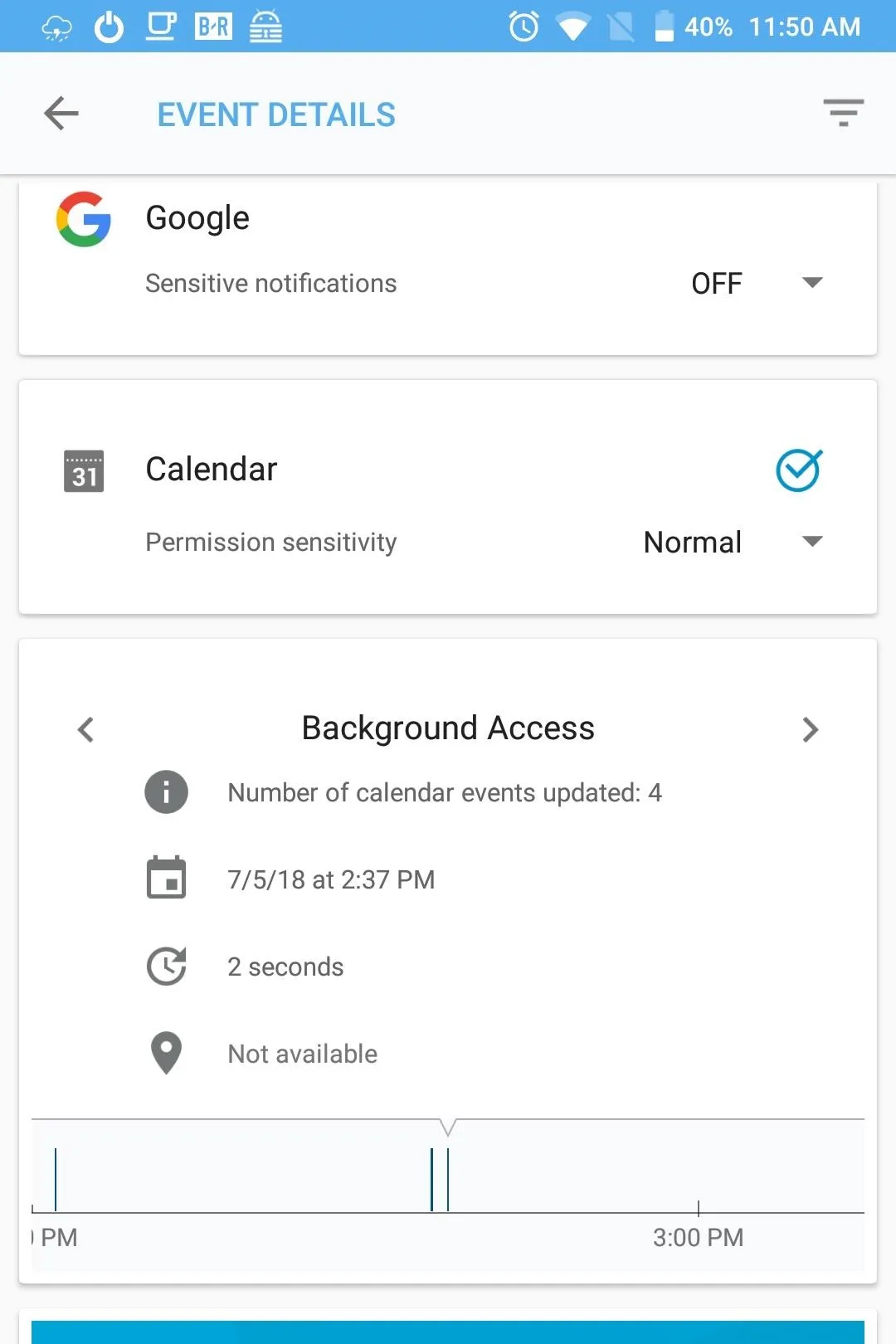
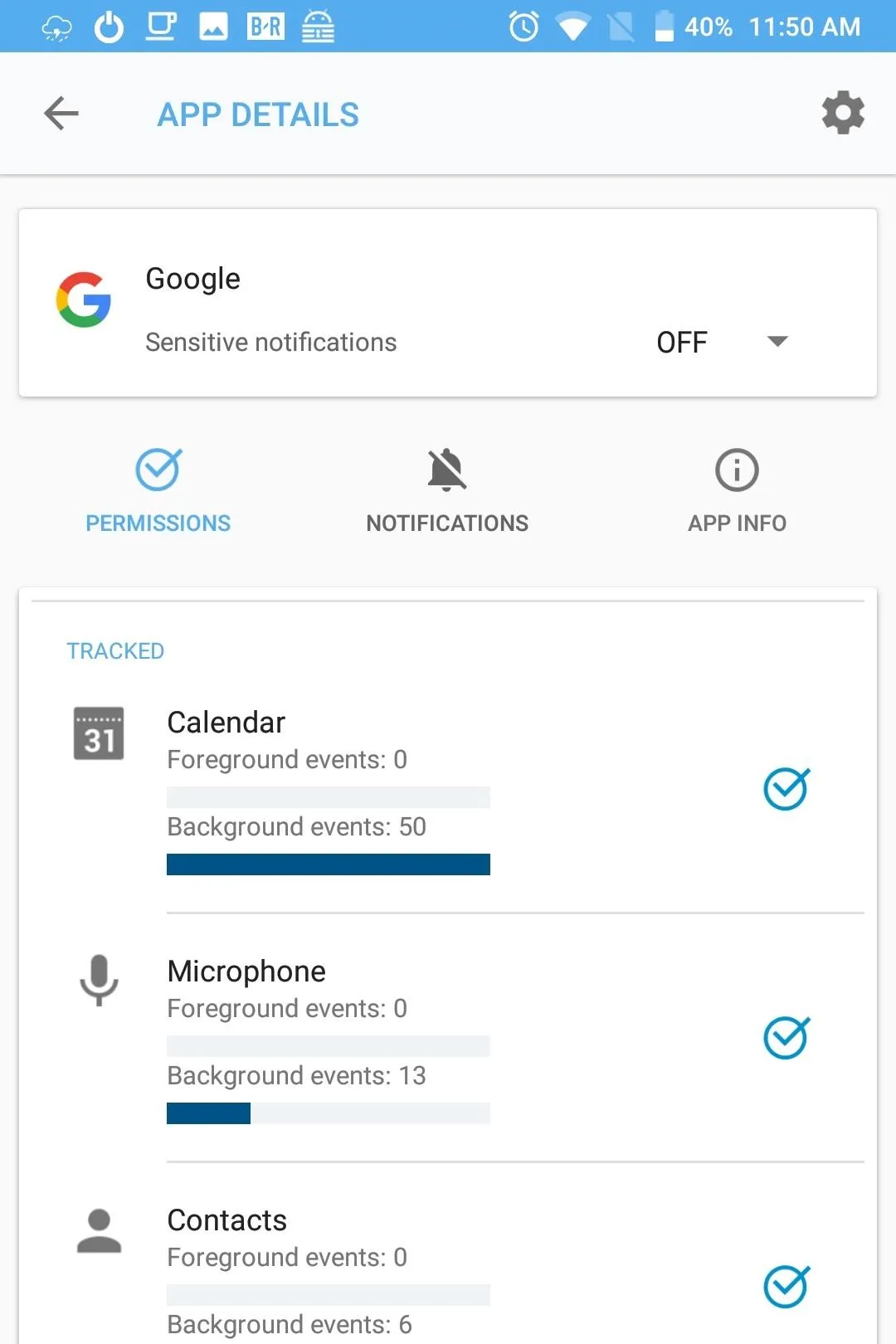
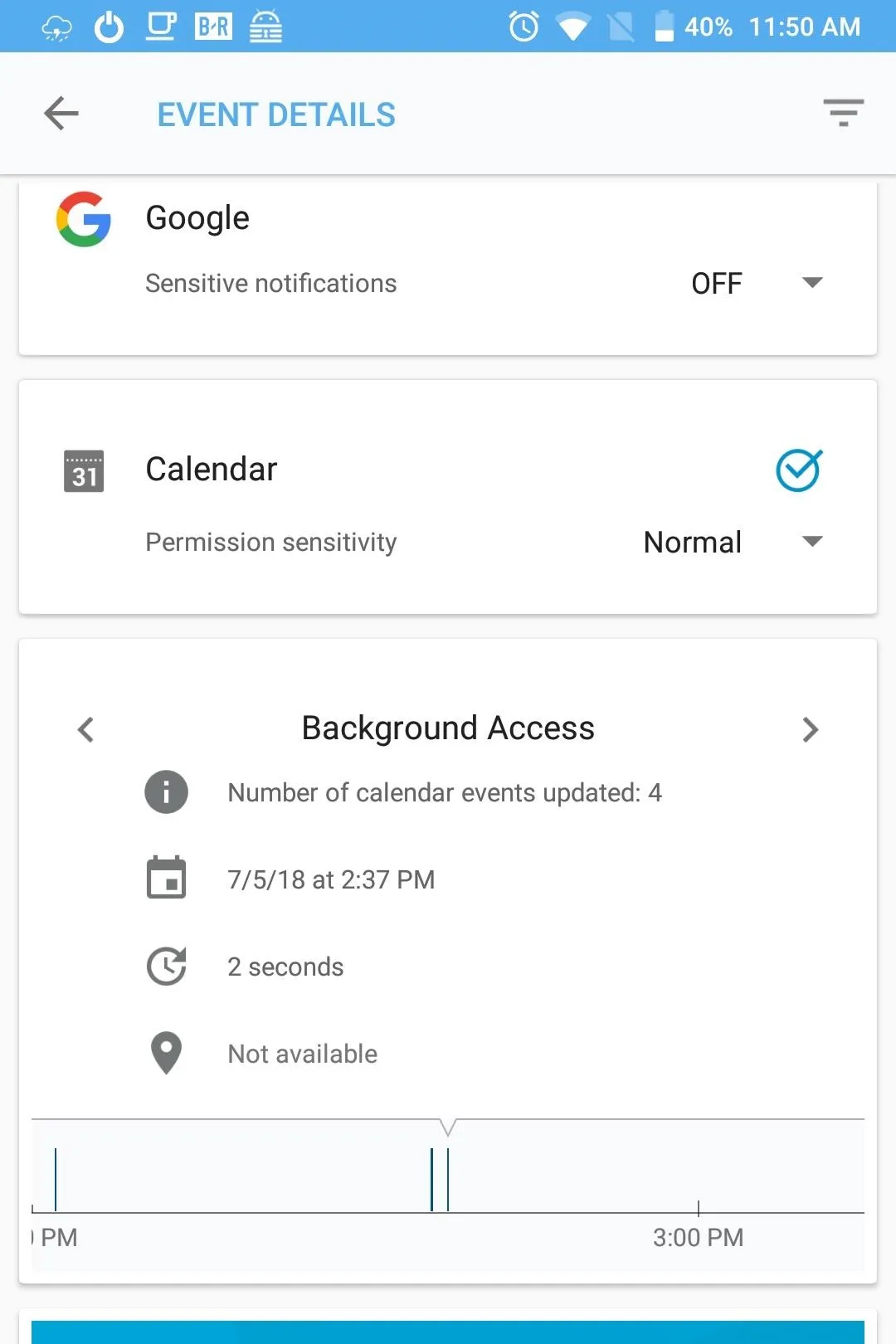
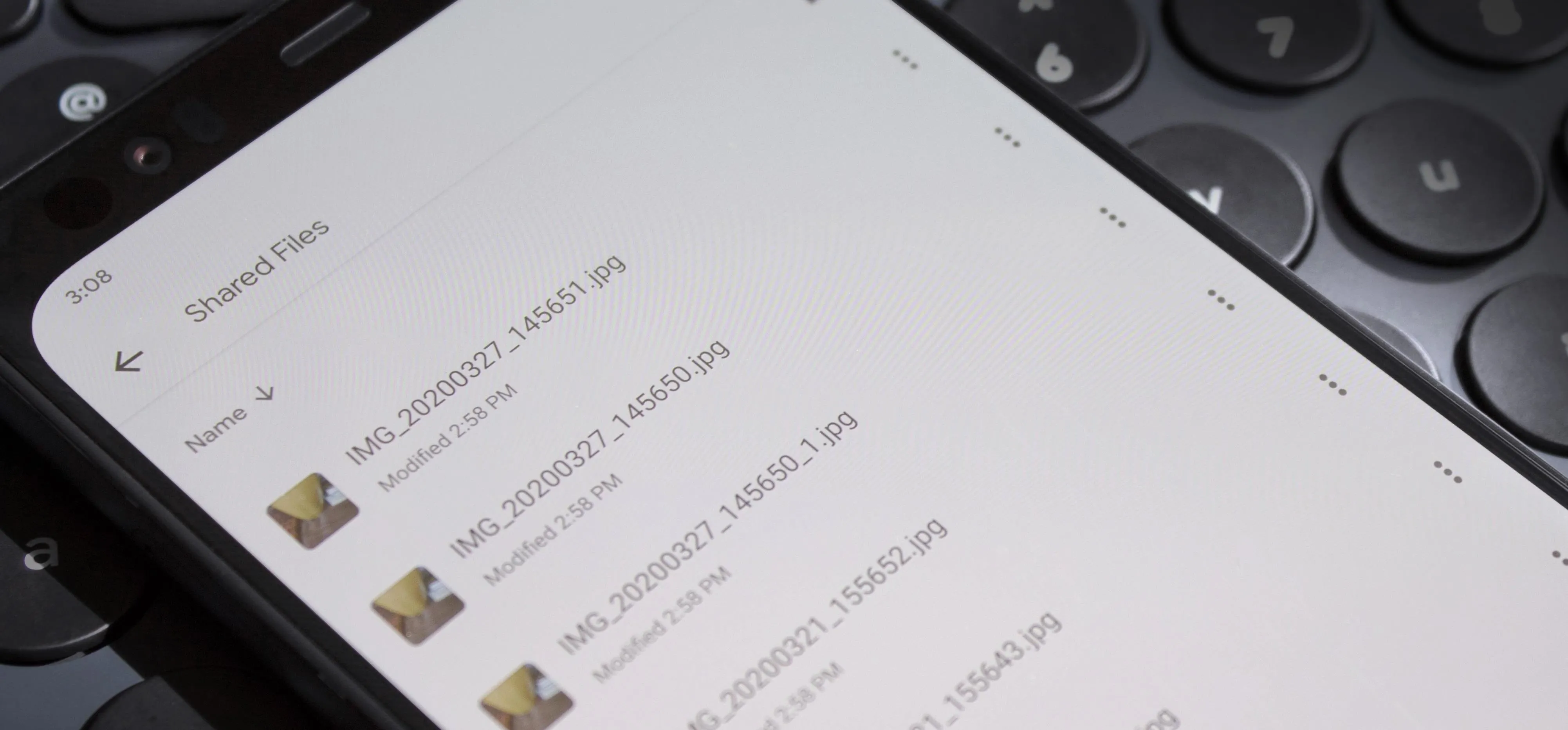
From the DTEK home page, when you select "Applications," you will be presented with a list of all the apps you currently have installed on your device, along with an icon representing what trackable permissions each app presently has access to. DTEK can track each request for any permission except for the device storage.
To view the tracked information, select any app on the list. Currently monitored permissions will have a blue checkmark. Below each permission is gauge representing the number of times the app accessed this data or sensor, with a separate gauge for background requests and foreground requests.
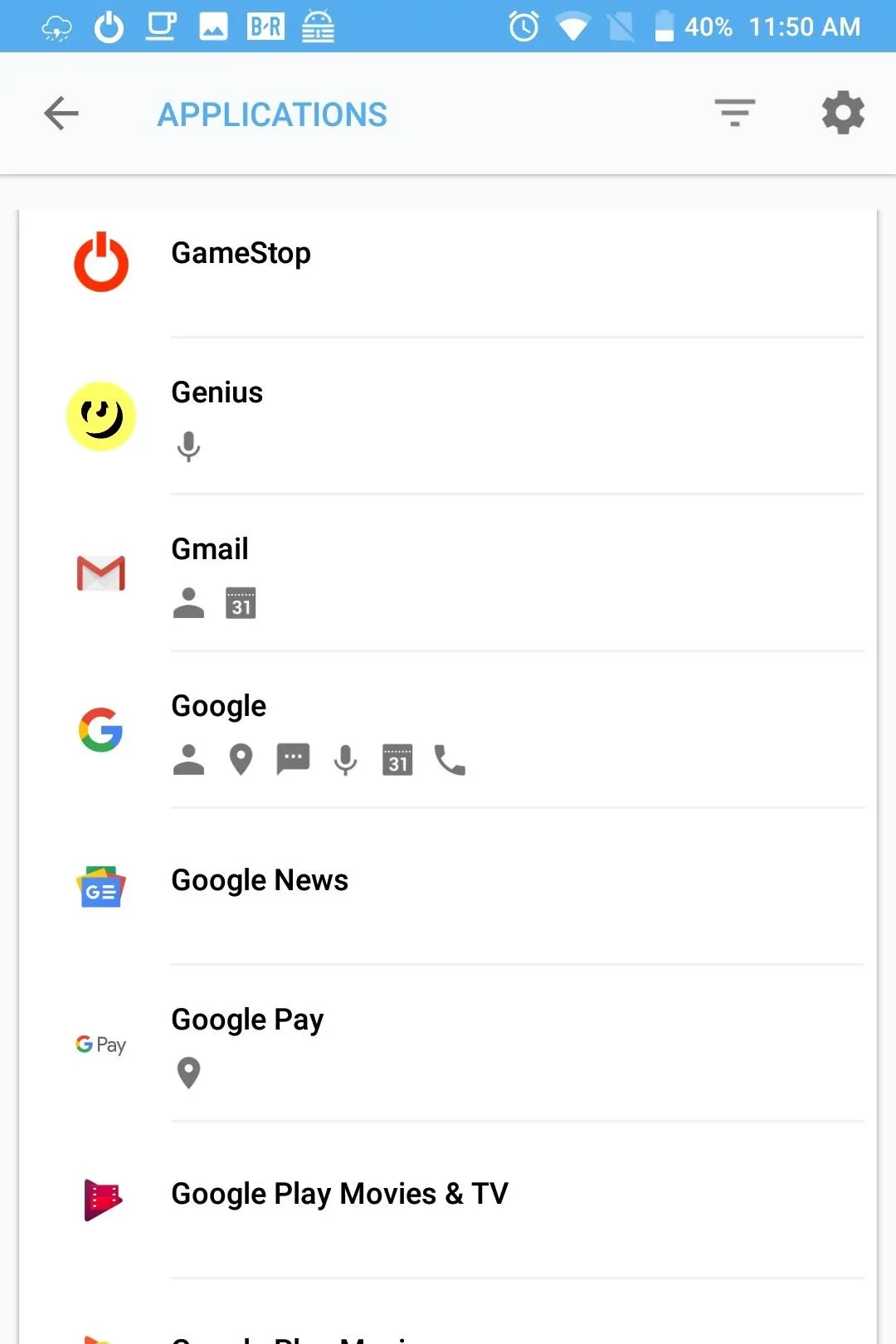
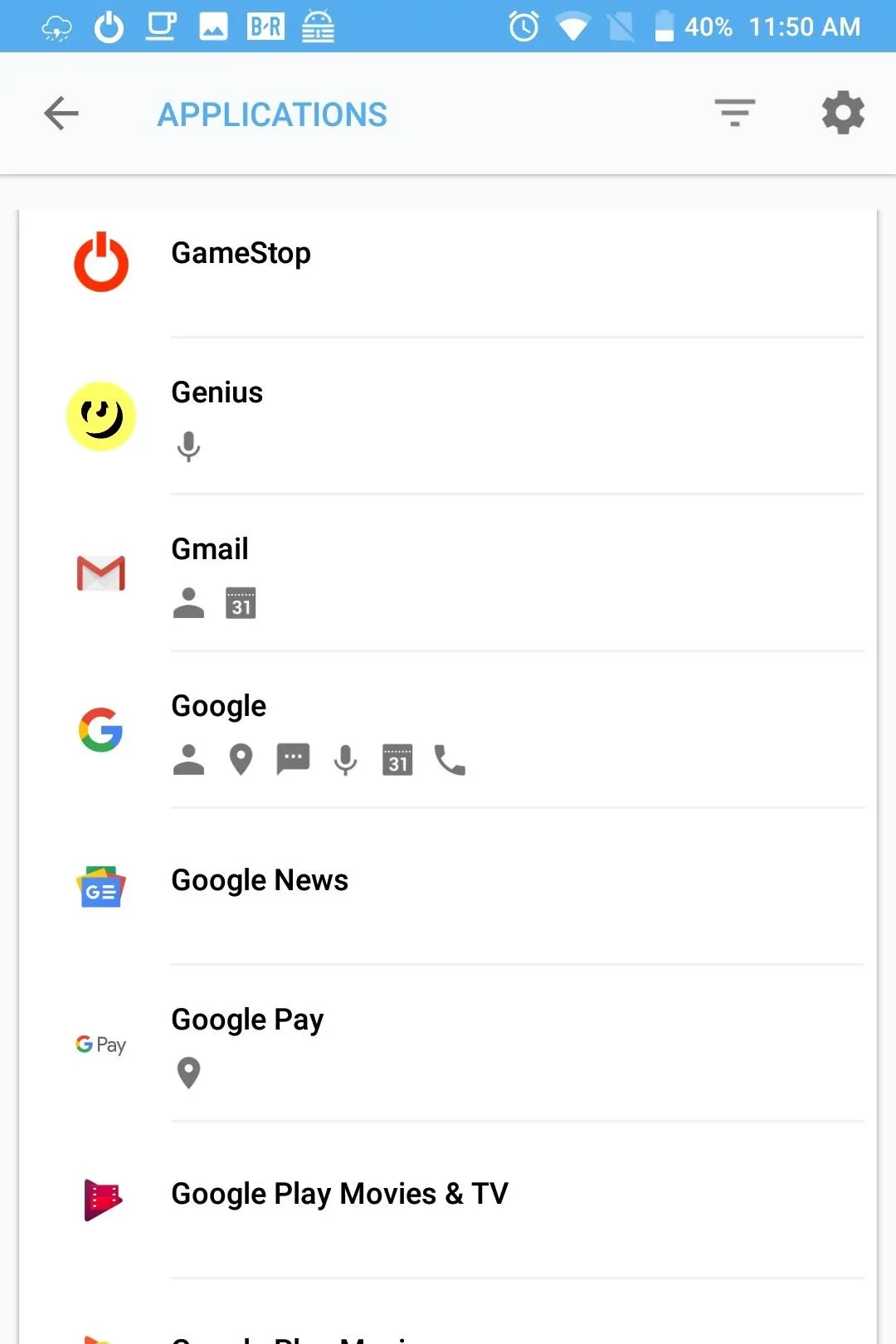
By selecting a permission, more information is presented such as the date, time, and duration for each request. Additionally, you can also adjust notifications based on this data. For example, you can make all requests by this app for this specific permission create a notification to alert you. Additionally, you can change the permission to "Sensitive," generating a notification for all requests, regardless of app.
DTEK is a powerful tool for security-conscious individuals. For many, it will remain untouched in the background, providing you automated protections against the dangers lurking on the web. However, for those of us who don't mind tinkering, DTEK can become even more powerful, allowing you to know precisely how apps are operating on your device.
- Follow Gadget Hacks on Facebook, Twitter, YouTube, and Flipboard
- Follow WonderHowTo on Facebook, Twitter, Pinterest, and Flipboard
Cover image and screenshots by Jon Knight/Gadget Hacks




















Comments
Be the first, drop a comment!