When Google introduced the Pixel 3 on October 9th, one of new additions they briefly mentioned was the Titan M security chip. While they did talk about how it will improve overall security, they didn't expand on the number of changes it brings to the Pixel 3's security. Well, they finally shared more, and it's a pretty big deal.
The Titan M is a more advanced version of the hardware security module on last year's Pixel 2 lineup. They borrowed from the Titan chip used in their data centers and tailored it for mobile users (hence the M). And thanks to security improvements of Android 9.0 Pie, Google better integrated the security chip so that apps can also take advantage of its power.
With the new improvements, both the OS and apps will benefit from secure hardware. Titan M will make sure your phone boots up with verified software each time, checking each layer of booting. Apps can be sure passwords and payments are authorized and uncorrupt as they leave your phone. The result is a potential end to exploits applied on locked phones, stronger encryption, and a rewrite of Google's past failures to protect its users.
Protecting Vertified Boot
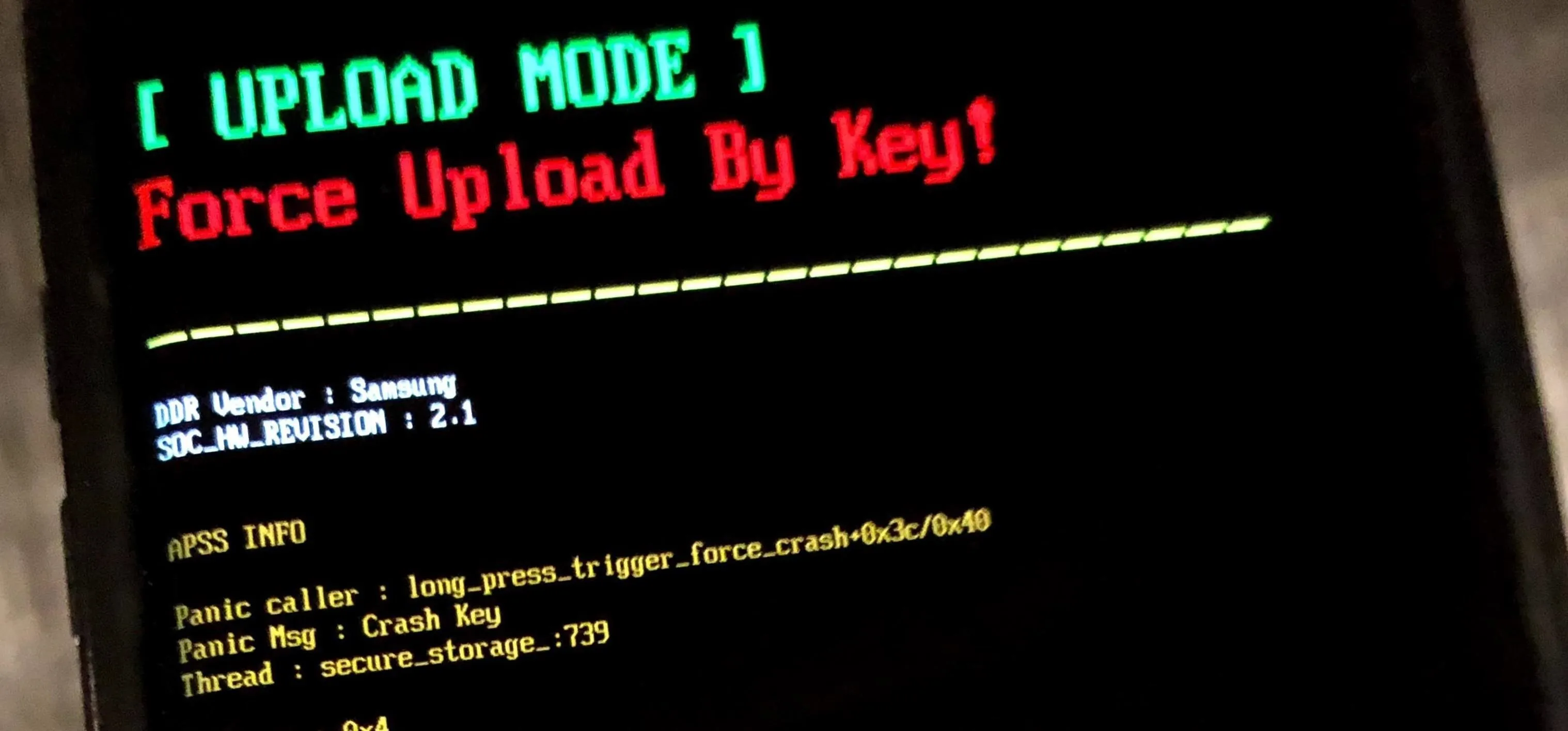
Expanding on Android's Verified Boot system, Google is taking a page from BlackBerry and integrating the security chip into the secure boot process. The Pixel 3 will validate the version number of the Android operating system to ensure you are using the right version. Specifically, it offers rollback protection to prevent someone from downgrading your phone to an older Android version.
This way, an attacker can't downgrade the operating system to circumvent new security tools introduced in the latest version. For the Pixel 3, this is very important, since Android 9.0 Pie introduced a host of new security features. By downgrading you to Oreo, an attacker could circumvent these upgrades. However, with the Android version now being verified in the Titan M chip, you're protected against foreign attacks during the verification process since the Titan M is separate from the SoC.
Additionally, Titan M also protects your device from running a corrupted version of Android. During each boot-up, Verified Boot (performed in the Titan M) will ensure all code comes from a trusted source, requiring each partition to be checked before moving to the next one.
Finally, by executing the verification process in the Titan M chip, it prevents exploits from unlocking the bootloader within Android. The bootloader won't pass the verification process, and it would fail to advance to the next stage. To be clear, this doesn't prevent you from unlocking the bootloader on the Pixel 3 — that's still as easy as ever.
Protect Transactions
With Android 9.0 Pie, Google introduced Strongbox KeyStore APIs, a new tool which specifically dealt with the hardware security module. Using this API, Titan M can now generate and store private keys for apps, thereby extending its protection not only to the OS, but third-party apps as well.
Android 9.0 Pie also introduced Protected Confirmation, a feature which displays a prompt asking a user to approve a short statement. By accepting the statement, the app can reaffirm the user read the message and is willing to complete the sensitive transaction such as payments or voting. Using Titan M, a key will be generated to sign the message. Because Titan M is separate from the OS, the signature is unique and leaves the app with a high level of certainty that the user has read the message and agreed to it.
Protection Against Tampering
For years, phones have used secure environments to protect encryption keys. These environments run firmware that is highly secure and responsible for checking the users' passcode to obtain the key to decrypt the storage partition.
However, malicious users could attack this system by replacing the secure firmware they run with an exploitable one, making it easier for them to access. To prevent this, OEMs, including Google, apply a digital signature which confirms the software being used is from Google. However, attackers can defeat this process in one of two ways: find a vulnerability in the signature-confirmation process or gain access to a signed key and use that to sign their malicious software.
The former is pretty difficult, but with the second option, keys can be captured using coercion or social engineering. Therefore, Google felt the need to improve this protection to prevent these keys from being accessible to the wrong individual.
What Google has done with Titan M is improved protection by building in insider attack resistance. With this protection, Titan M is protected against the use of malicious software by preventing any updating to its firmware from occurring without the user first entering a passcode. This means that without your passcode to unlock your lock screen, there is no way for a malicious actor to change the firmware of the Titan M, resulting in the keys become comprised. This will make encryption of your Pixel 3 or 3 XL that much stronger and more resistant to tampering.
With the changes Google is making, it looks like BlackBerry is rubbing off on them. Google is prioritizing security and doing everything they can to make sure your Pixel 3 and 3 XL is safe from unintended changes by utilizing the power of the Titan M security chip. What do you think about these changes? Are you excited about this level of protection? Let us know in the comments below.
- Follow Gadget Hacks on Pinterest, Twitter, YouTube, and Flipboard
- Sign up for Gadget Hacks' daily newsletter or weekly Android and iOS updates
- Follow WonderHowTo on Facebook, Twitter, Pinterest, and Flipboard
Cover image by Dallas Thomas/Gadget Hacks




















Comments
Be the first, drop a comment!