We know Android 9.0 will have the formal designation of Pie, following Google's age-old tradition of naming their OS after items you'd normally find on a dessert menu. And thanks to a slew of new features that centers around your overall security, P could also stand for Privacy.
Android Pie will bring several changes to normal operations. Certain actions will be prevented to ensure protection, and support for a few advancements in cybersecurity will be included, making the mobile OS better protected against new threats. Finally, when it comes to our phones, danger can also come from nearby, so Android 9.0 will introduce new privacy protections to guard against this threat.
1. HTTPS Is the Default for Apps
By default, Android Pie will request that apps use HTTPS connections instead of HTTP. With HTTPS, data is secured during transit using TLS encryption, making it nearly impossible to intercept any data traveling to or from your device.
While Android 9.0 doesn't prevent HTTP usage for legacy compatibility issues, it does strongly encourage all apps to use it. For end users, apps built for the new version can provide peace of mind, as personally identifiable information (such as your name and login information) is secured by default.

2. Restoring Your Device Requires a Passcode
Backups in Android 9.0 Pie are now encrypted. Therefore, users must enter their device's PIN, pattern, or password before restoring their device. This is helpful for stolen devices where users may use the remote wipe feature to protect their data.
Previous versions allowed a tech-savvy thief to potentially use the restoration (if they knew your login) to gain access to your data. However, with Android Pie adding an extra layer of security, no one will have access to your data unless they know your login and PIN. However, like with all security measures, it's a double-edged sword. If you forget your own password or PIN, you may not be able to restore your device.
3. Unified Fingerprint Authentication Dialog
Many apps use the fingerprint scanner as a way to speed up authentication into your account. Android Pie standardize the look, feel, and placement of the fingerprint authentication dialog. Therefore, all apps (whether system or third-party) will have a similar prompt for fingerprint usage, allowing for a more consistent experience.

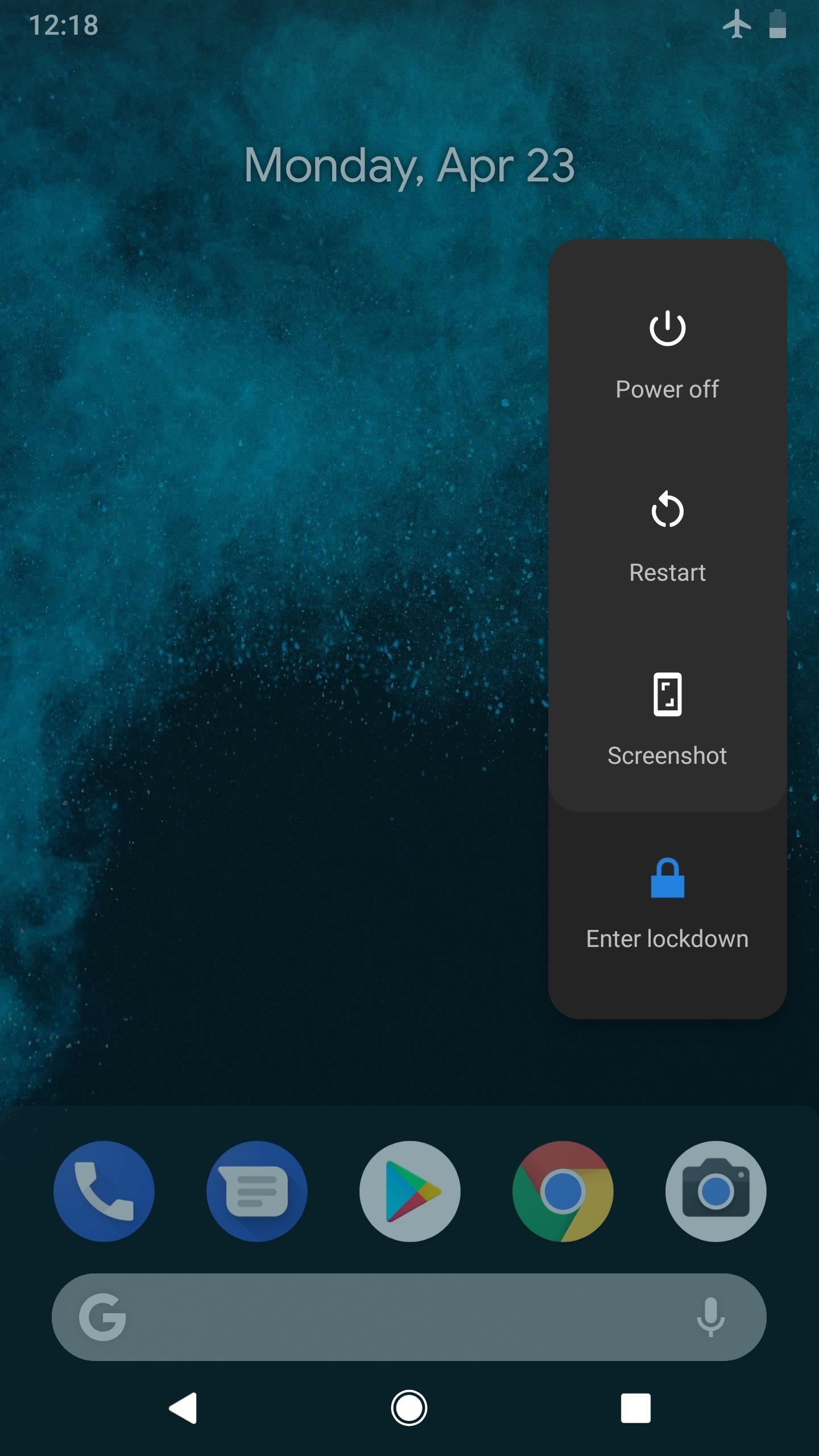
4. Lockdown Mode
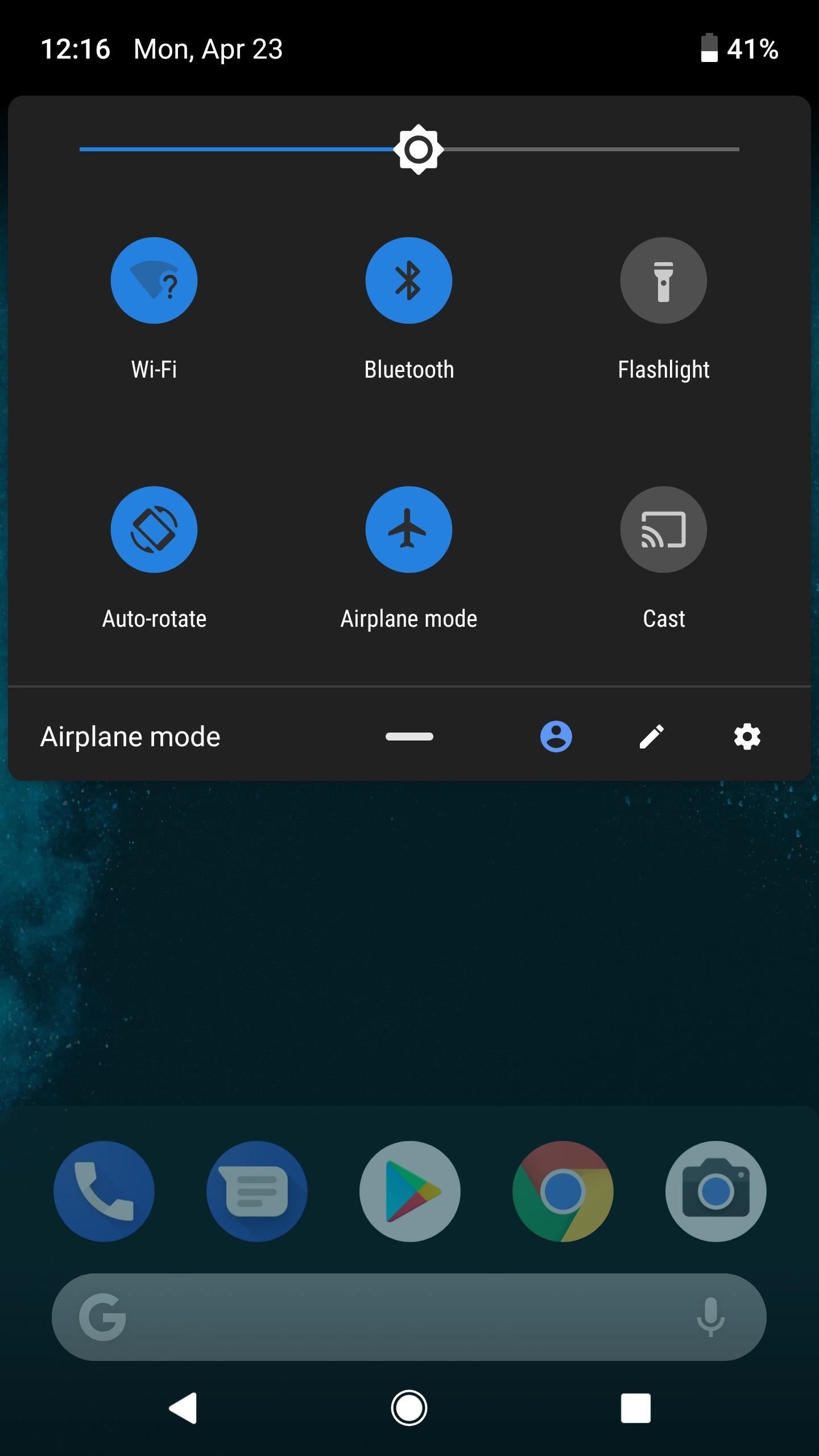
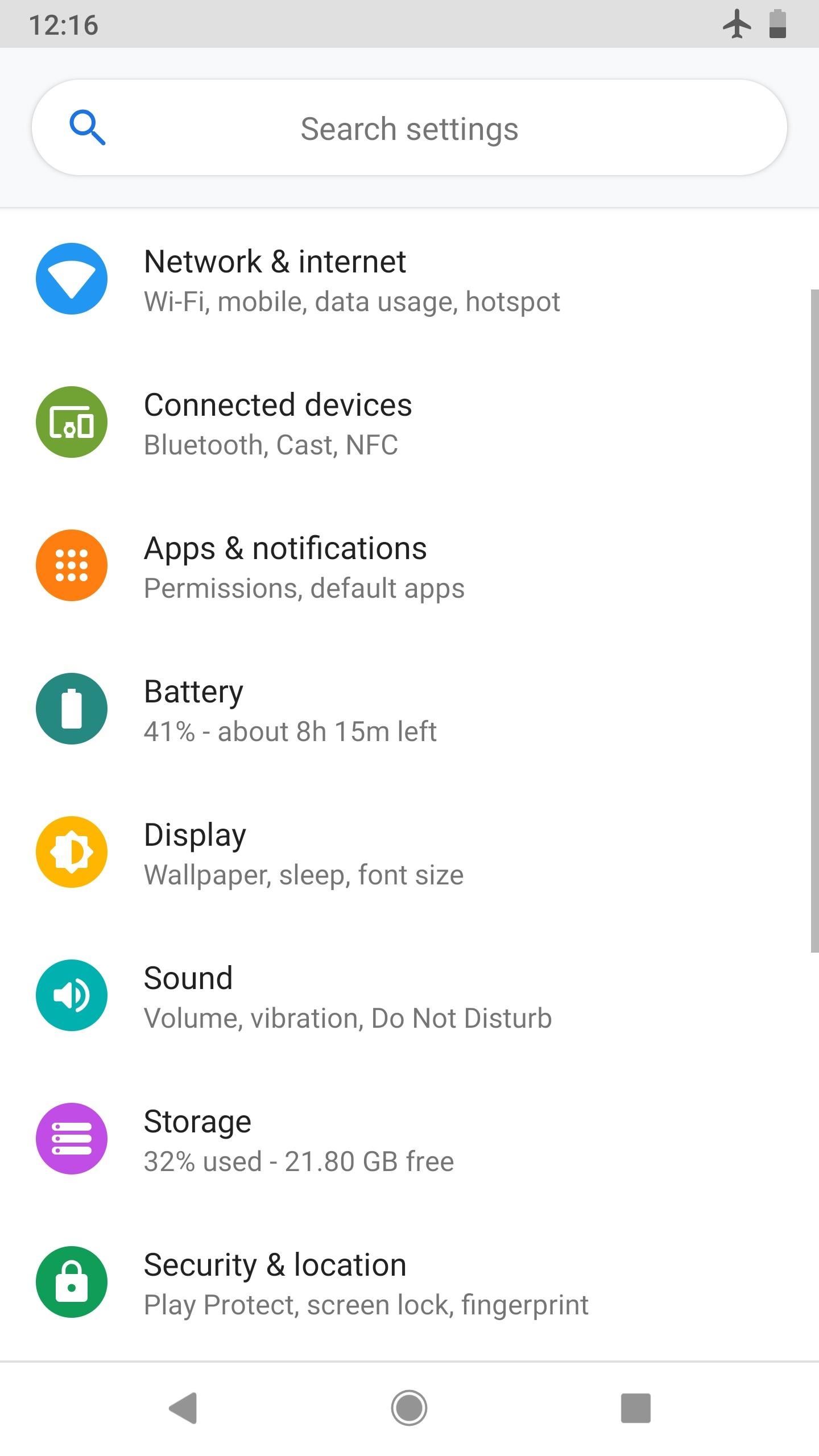
Android Pie introduces a new option in the power menu. Known as "Lockdown Mode," it's not enabled by default, but it can easily be toggled on under Settings –> Security –> Lock screen preferences.
Once you've enabled the option, just bring up the power menu by long-pressing the power button. From there, pressing "Enter lockdown" will disable the convenient and less secure authentication methods such as fingerprint scanning and Smart Lock. Therefore, the only way to unlock your device is with the PIN, pattern, gesture, or passcode.

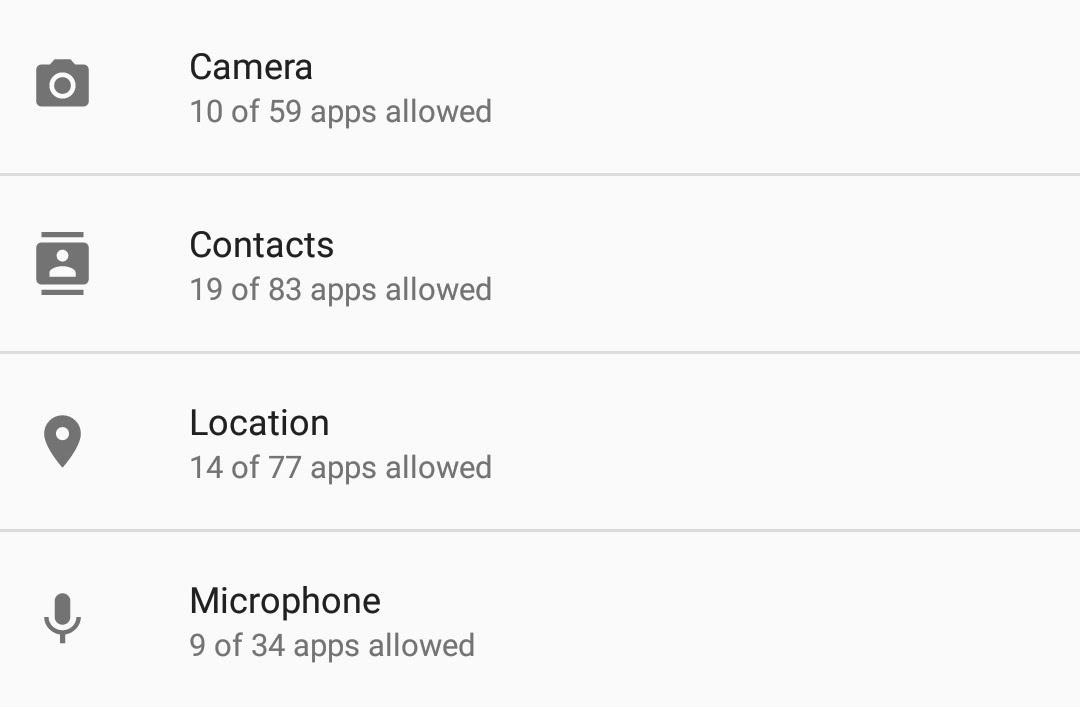
5. Background Apps Won't Have Mic Access
Android Pie will also introduce a number of changes to normal operations to combat malicious agents such as hackers. One such change come in the form of blocking apps' access to the microphone while the app is running in the background.
Initially discovered by XDA, when the app enters into an idle state, Android Pie's audio system will stop any further access to the microphone. If a malicious app requests it, Android will send it empty data.
6. Background Apps Won't Have Camera Access Either
Additionally, the same protection provided to the microphone will be extended to the camera. According to XDA, when an app is idle, Android will generate an error message and stop access if it tries to use the camera.
7. Data Privacy for Other Sensors
Android 9.0 Pie also includes new privacy changes to protect users against malicious use of the other sensors. As highlighted in our article, many of the other sensors included in our phones are quite dangerous when used incorrectly. It seems the Android team is aware of this and included several modifications to combat such threats.
The biggest change is that Android Pie will prevent continuous reporting from sensors such as the accelerometer and gyroscope. It was possible in the previous versions of Android to use continuous reporting mode for a number of unintended usages, such as learning your current location, including accounting for any turns in your commute.
Android Pie will also prevent on-change or one-shot reporting modes in sensors. The on-change reporting mode reports to an app whenever a change in an action is detected by the sensor. An example would be using the accelerometer to detect a change in your speed. One-shot reporting mode reports back to an app when a specific event is detected, and will then deactivate the sensor. When the sensor deactivates, an app could theoretically collect the data it reported without detection. This is no longer the case in Android 9.0.
When an app needs a sensor to remain on to detect an event, Android Pie is asking that developers use the foreground service, which keeps an active notification so users know exactly what the app is doing, including its usage of the sensor.
8. Alert Tone When Your Call Is Being Recorded
In cases where phones are able to record calls, Android Pie will play a tone every fifteen seconds, alerting the other party that they are being taped, according to XDA. The inclusion of this tone makes Android's call recording API more in line with some states' two-party consent laws, which require both parties to be aware of the recording for it to be legal.
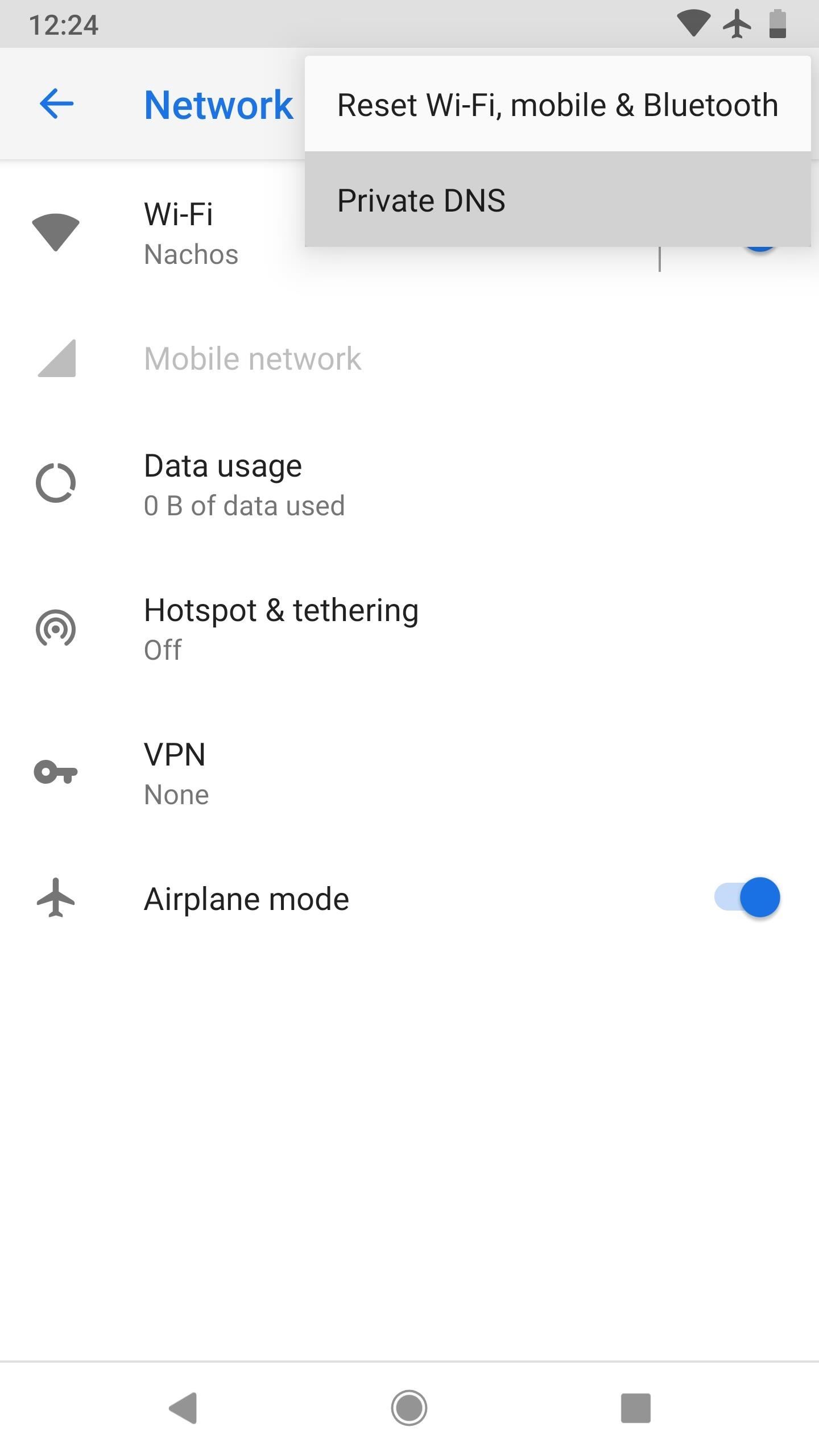
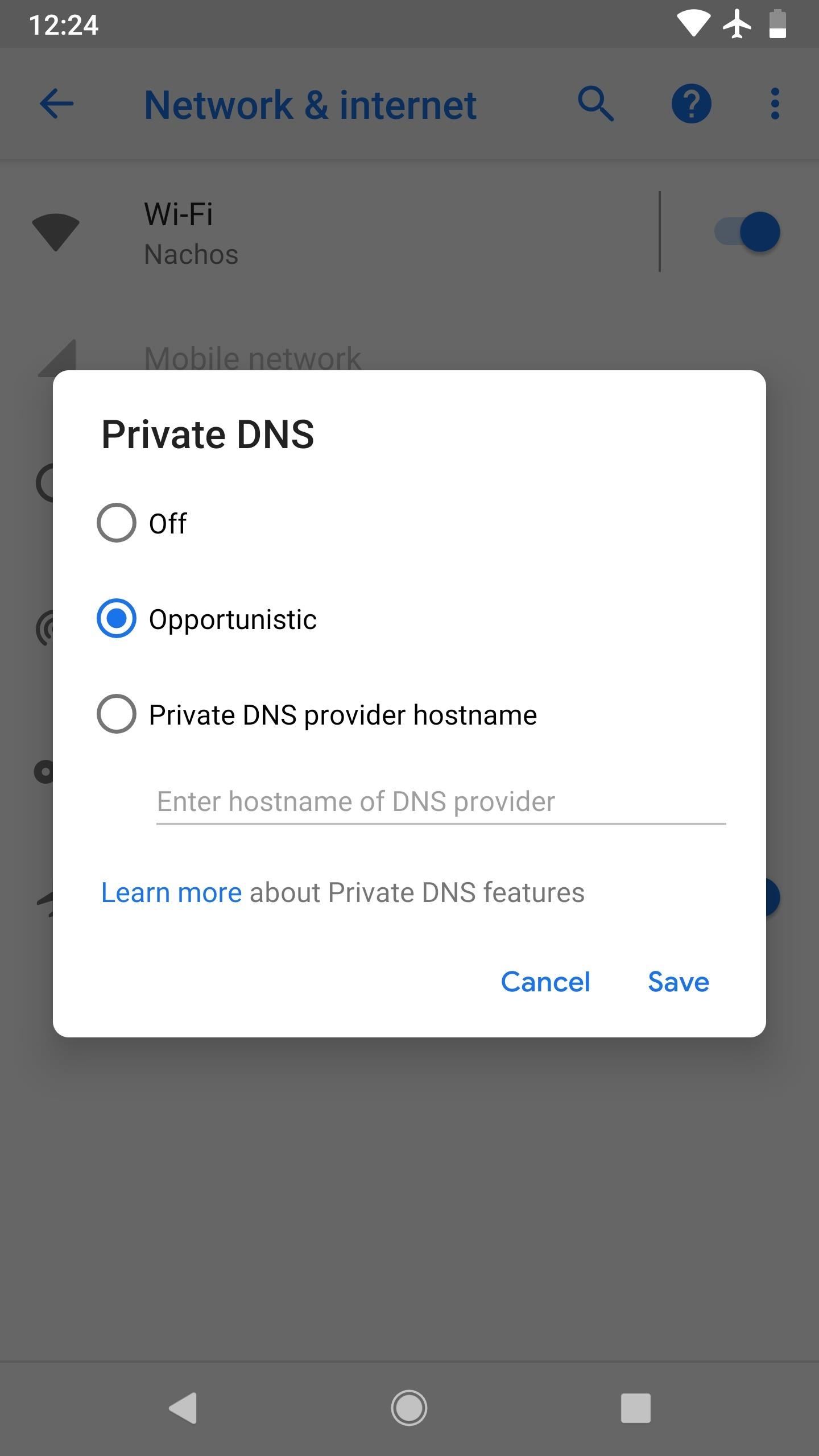
9. DNS Over TLS & Private DNS
Android 9.0 supports RFC 7858, commonly known as "DNS over TLS." The new protocol secures DNS queries by establishing an encrypted connection using TLS (the same protocol used for encrypted HTTPS connection). This protects your browsing history, as the name of the website you are visiting will also be protected using this encryption protocol.
By default, if your network's DNS server supports the feature, your device will automatically use the new protocol. However, for those not wishing to wait for their network, you can now switch the default DNS server for all apps on your phone. Previously, the only way to switch your DNS server was to establish a VPN connection.
10. Protected Confirmation API
When you conduct a transaction that involves sensitive information, developers can now use the Protected Confirmation API to ensure users agreed to the transaction (and all that it entailed). Using the new API, developers display a prompt to the user which reaffirms the transaction. Once the user agrees to the prompt, the app will receive a cryptographic signature which provides high assurance that the user read the prompt and agreed to the transaction.
11. Hardware Security Module
Devices launching with Android Pie can now support a feature called StrongBox Keymaster, which would reside in the hardware security module. Cryptographic keys can be checked within the module, which has a number of features to protect against tampering, including isolation from the rest of the hardware.
This wouldn't affect most current phones, but it paves the way for heightened security in new devices that ship with Android P or higher preinstalled.
12. Improved Protection for Hardware Serial Number
All smartphones include a unique serial number that remains on the device no matter what is done to the software. This unique ID is key for retrieving stolen phones, as this number stays the same no matter what others may try to do to it (including stealing it).
However, as mentioned in our article, this can also be used by advertisers to identify you. Continuing from the protection built in Android 8.0 Oreo, Android Pie will set the hardware serial number to unknown, protecting against apps trying to access this information.
It looks like Android 9.0 Pie is shaping up to be a true full-number update. With the expected visual changes known as Material Design 2, combined with the numerous modifications both under-the-hood and on the surface, users can expect Android Pie to a big step forward. From a security and privacy perspective, Android Pie will be the most secure version yet, helping to quell the arguments that when it comes to a secure phone, you should opt for an iPhone.
Who needs a wand? Unlock your magical powers and transform yourself from a Muggle into a Wizard or Witch just by using your Android phone. See how:





















Be the First to Comment
Share Your Thoughts